A network attack type recognition method based on multi-layer detection
A network attack and type recognition technology, applied in the field of information security, can solve the problems of low accuracy and recall rate of network attack classification algorithms, unbalanced data sets, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0123] According to the above technical solutions, the present invention will be described in detail below in conjunction with the accompanying drawings and implementation examples.
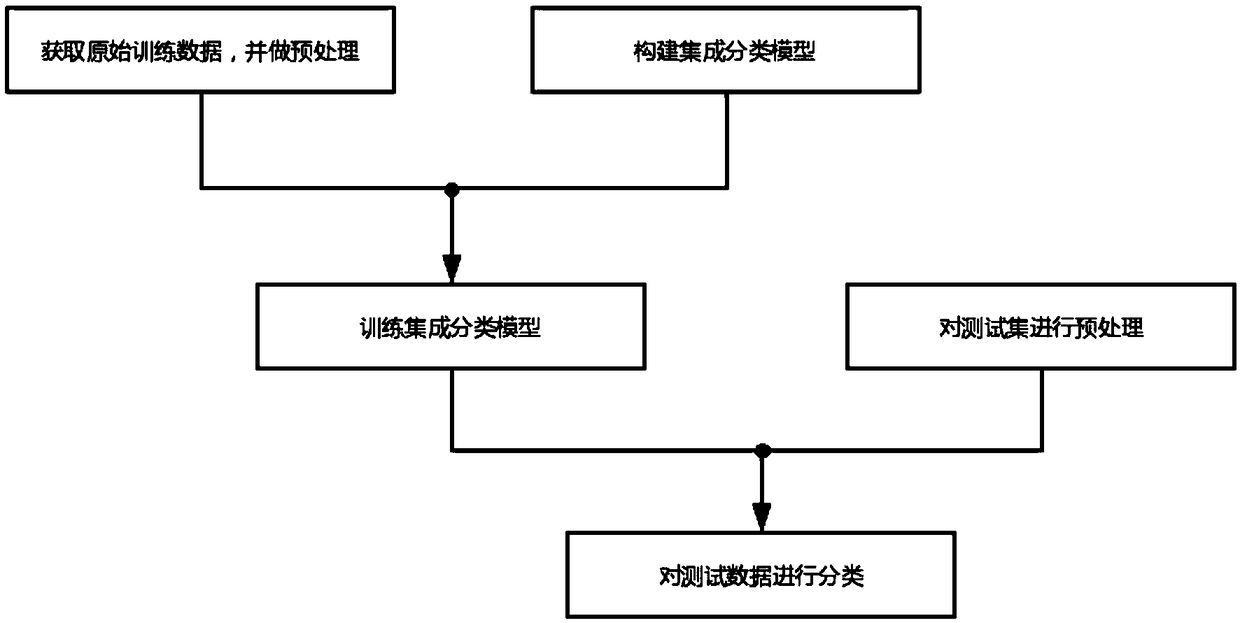
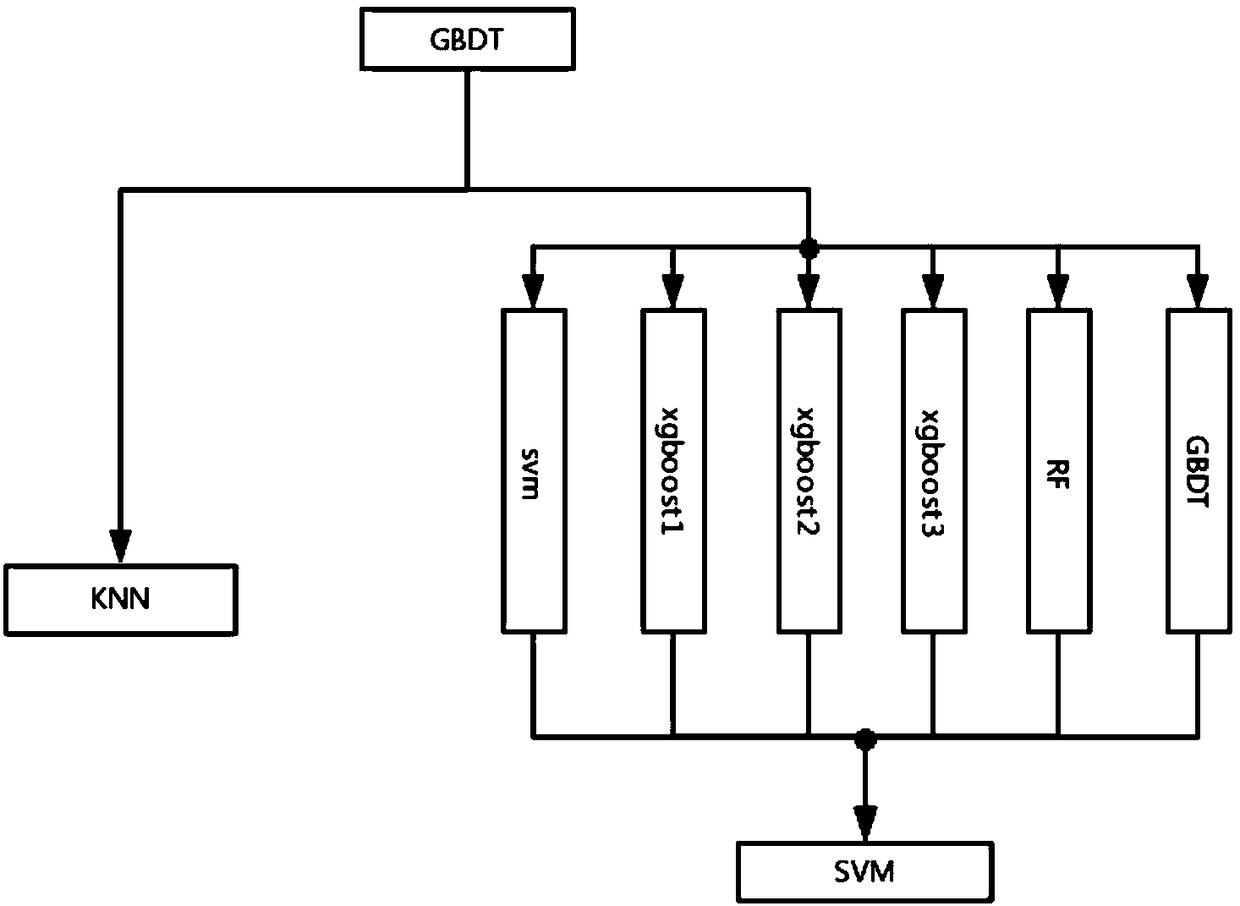
[0124] Using a network attack type identification method based on multi-layer detection proposed by the present invention, its operation flow is as follows figure 1 As shown, the specific operation steps are as follows.
[0125] Step 1. Obtain the original training data and perform preprocessing.
[0126] Step 1.1: Obtain network attack data to form the original training data set. This experiment uses the KDD99 data set. The data distribution in the original training data set is shown in Table 1, including Normal (normal), DoS (denial of service), PROBE (detection and scanning), U2L (illegal acquisition of super user privileges), R2L ( Unauthorized remote host access), five types of data. The distribution of subtypes of DoS data is shown in Table 2. Each piece of normal data or attack data co...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More