Authentication and key agreement method capable of resisting leakage of password
A technology of key agreement and password, which is applied in the field of information security and can solve problems affecting the efficiency of the protocol
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
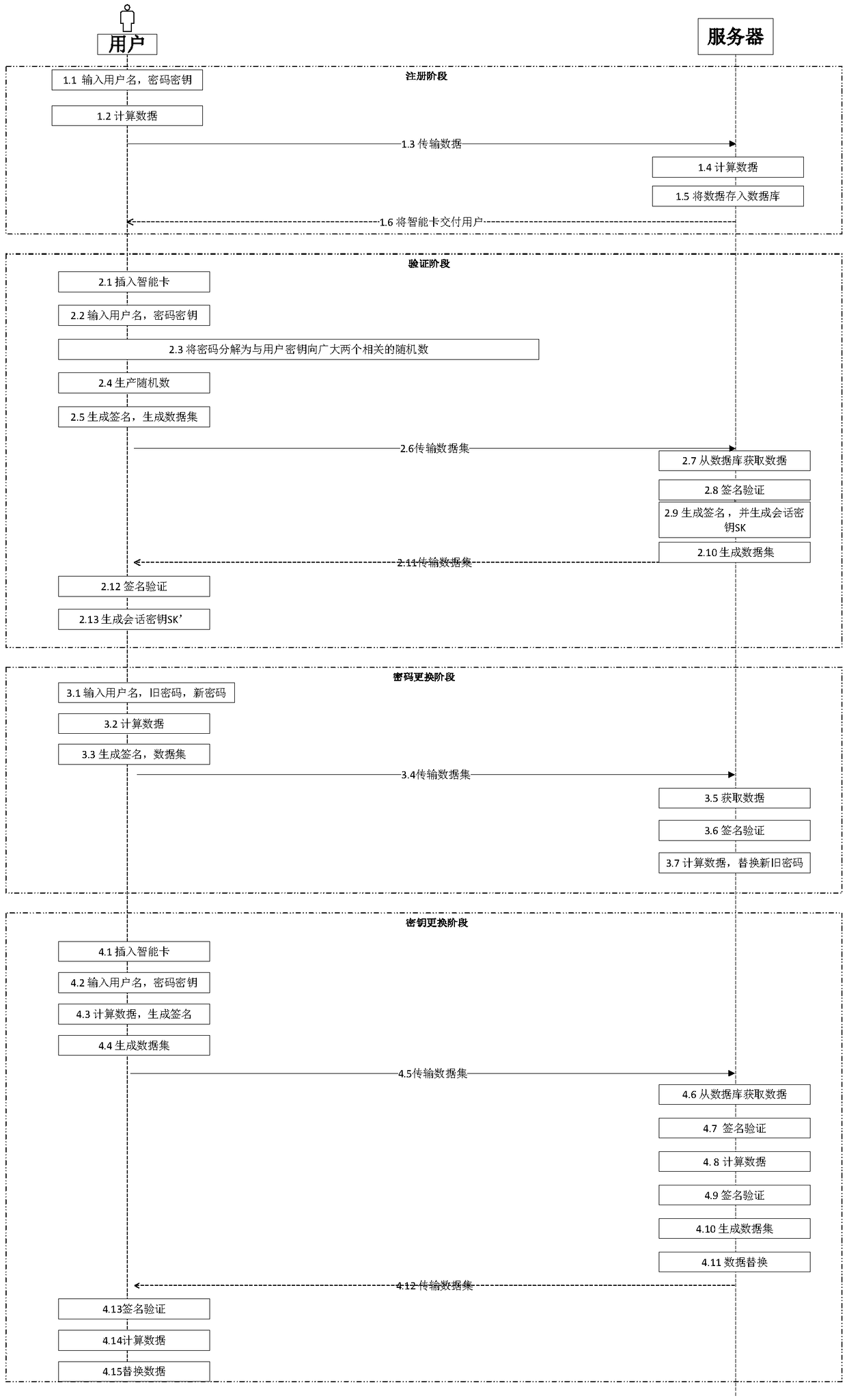
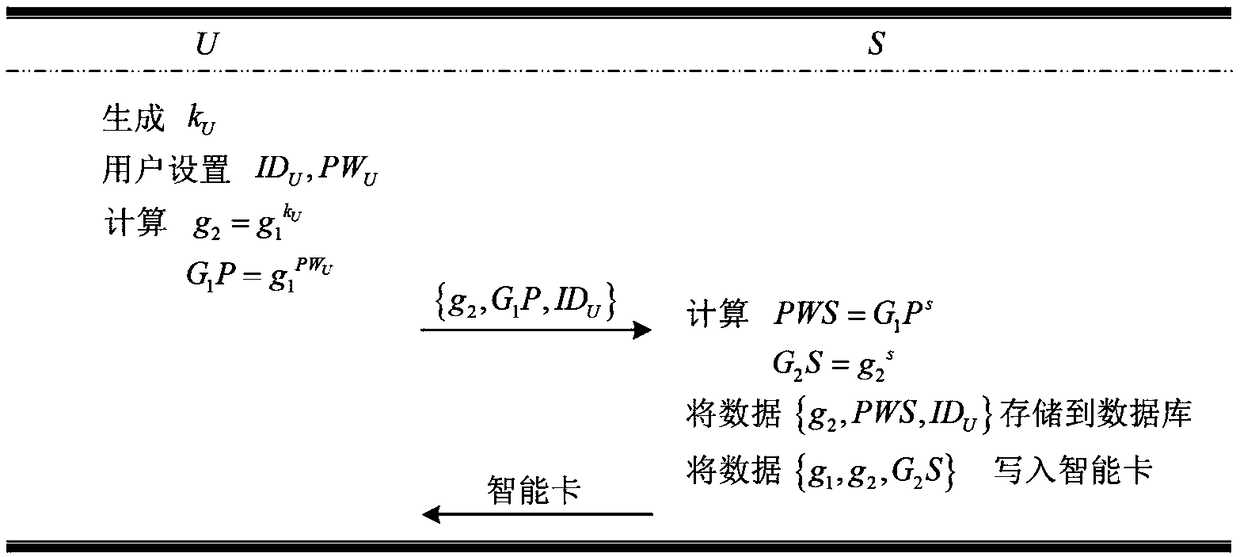
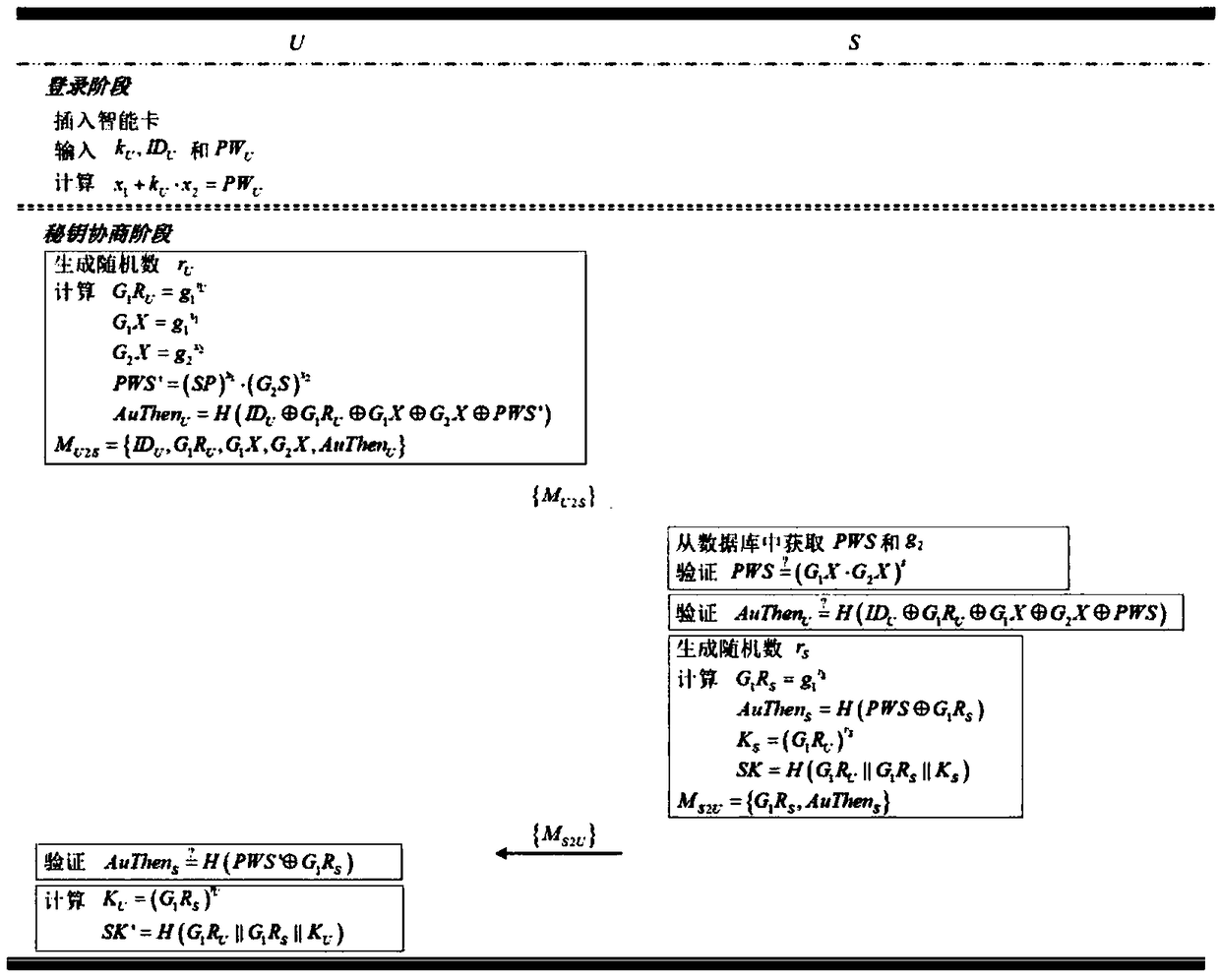
[0072] In order to facilitate those of ordinary skill in the art to understand and implement the present invention, the present invention will be described in further detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the implementation examples described here are only used to illustrate and explain the present invention, and are not intended to limit the invention.
[0073] please see figure 1 , a kind of anti-password leakage authentication and key agreement method provided by the present invention, comprises the following steps:
[0074] Step 1: Initialization, the server generates public parameters, private key and public key;
[0075] The specific implementation includes the following sub-steps:
[0076] Step 1.1: The server S chooses a random large prime number p, chooses one with g 1 is the multiplicative group of generators The order of the group is q, and the above data are disclosed;
[0077] Step 1.2: Selec...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More