A statistical identity authentication and log processing micro service system and an implementation method thereof
A technology of identity authentication and implementation method, applied in the field of network security, can solve the problems of many hidden dangers of single application, system downtime, low efficiency, etc., and achieve the effect of achieving high cohesion and low coupling requirements
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] In order to make the purpose, content, and advantages of the present invention clearer, the specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments.
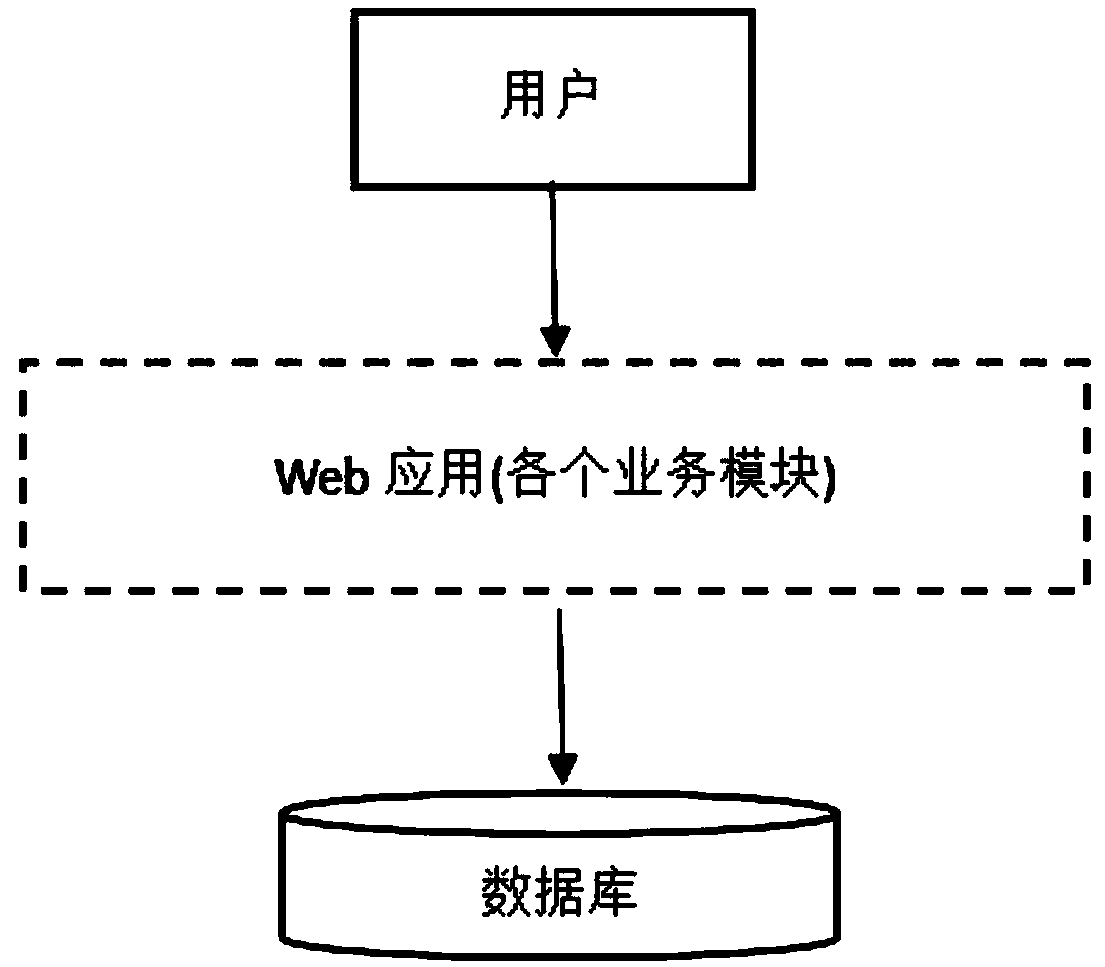
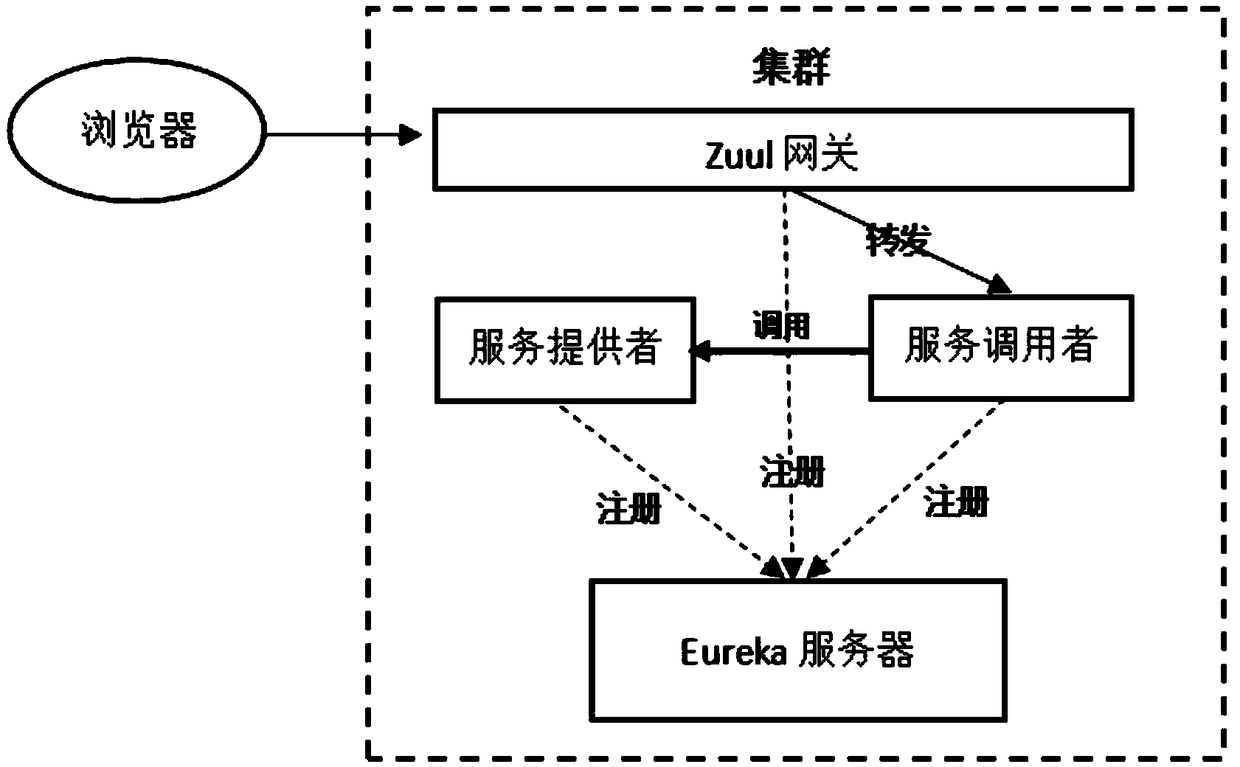
[0030] A statistical identity authentication and log processing microservice system designed by the present invention adopts a microservice architecture, as follows figure 2 as shown, figure 2 As one of the components in the microservice architecture, compared with single applications, microservices modularize the various business modules that were previously coupled together, making each business module a separate component, which improves the performance of the application It is also easy to manage, and once a bug or other problem occurs in an independent module, it will not affect other modules or the entire application.
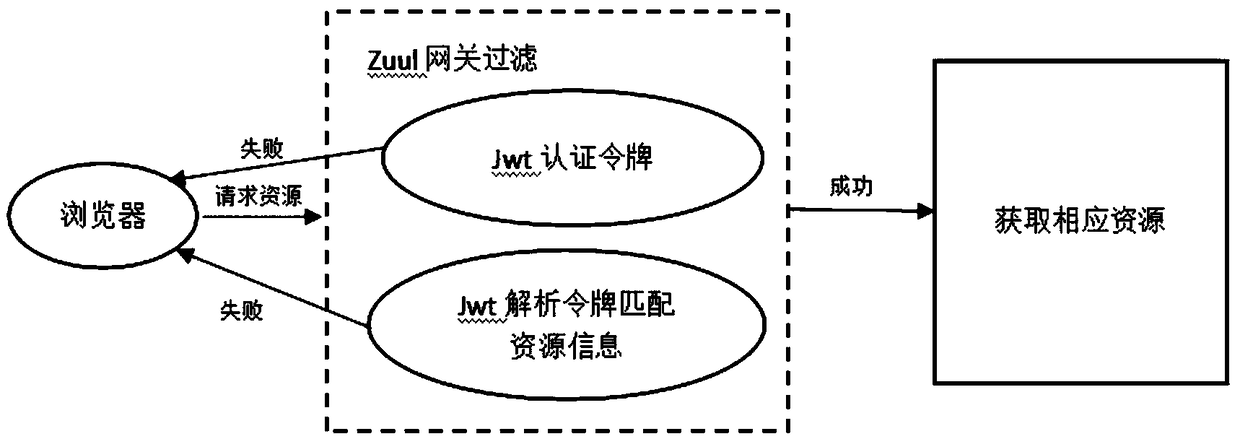
[0031] Identity authentication and log management are indispensable modules for every secur...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More