Authenticity query method, terminal and computer storage medium
A query method and terminal technology, applied in computing, network data query, business and other directions, can solve the problems of complicated operation process and low query efficiency.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
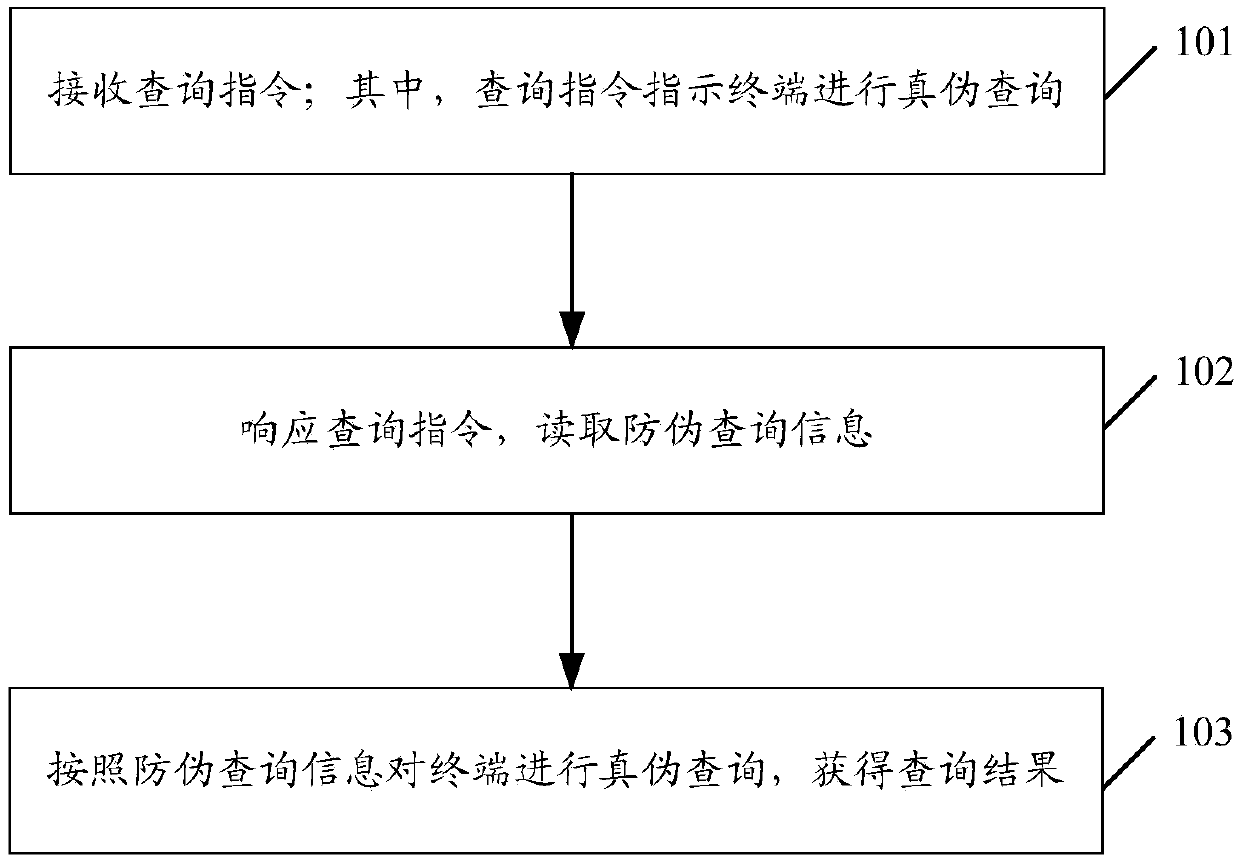
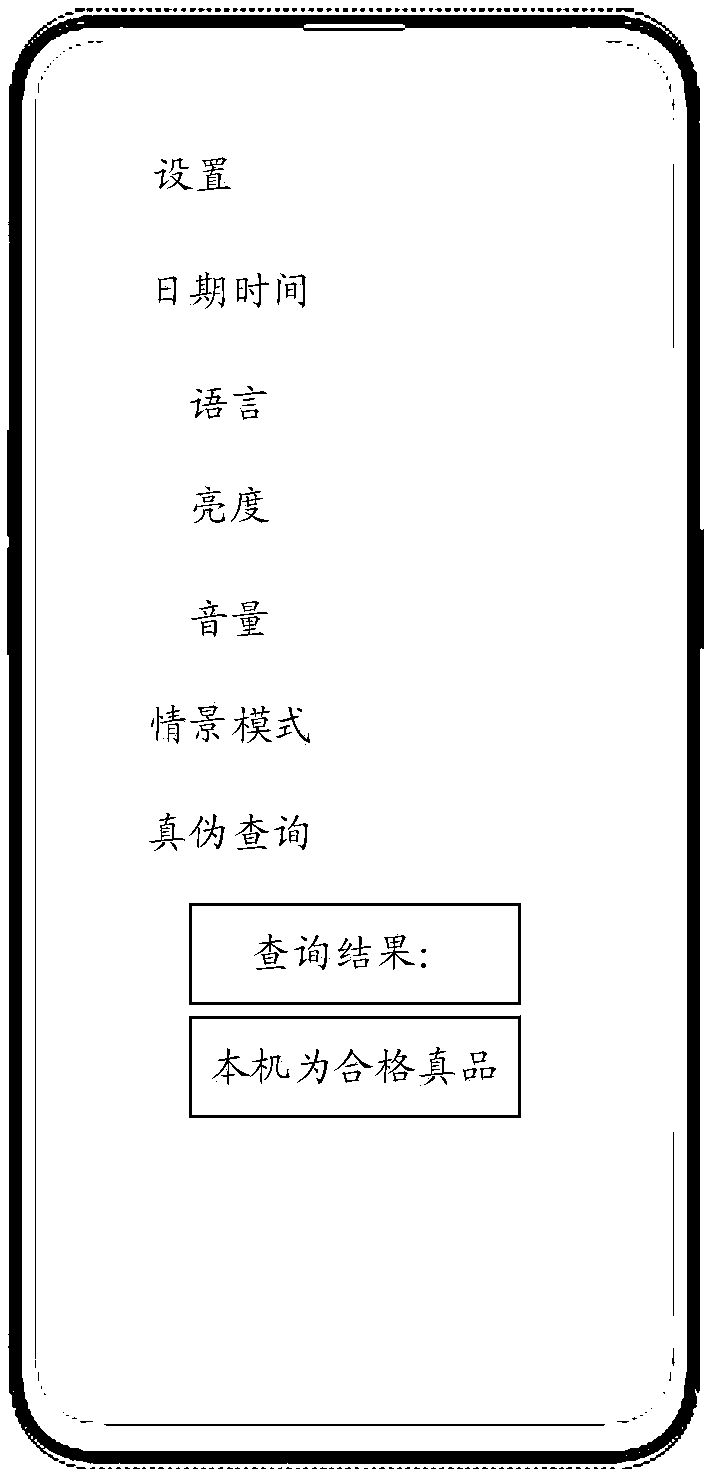
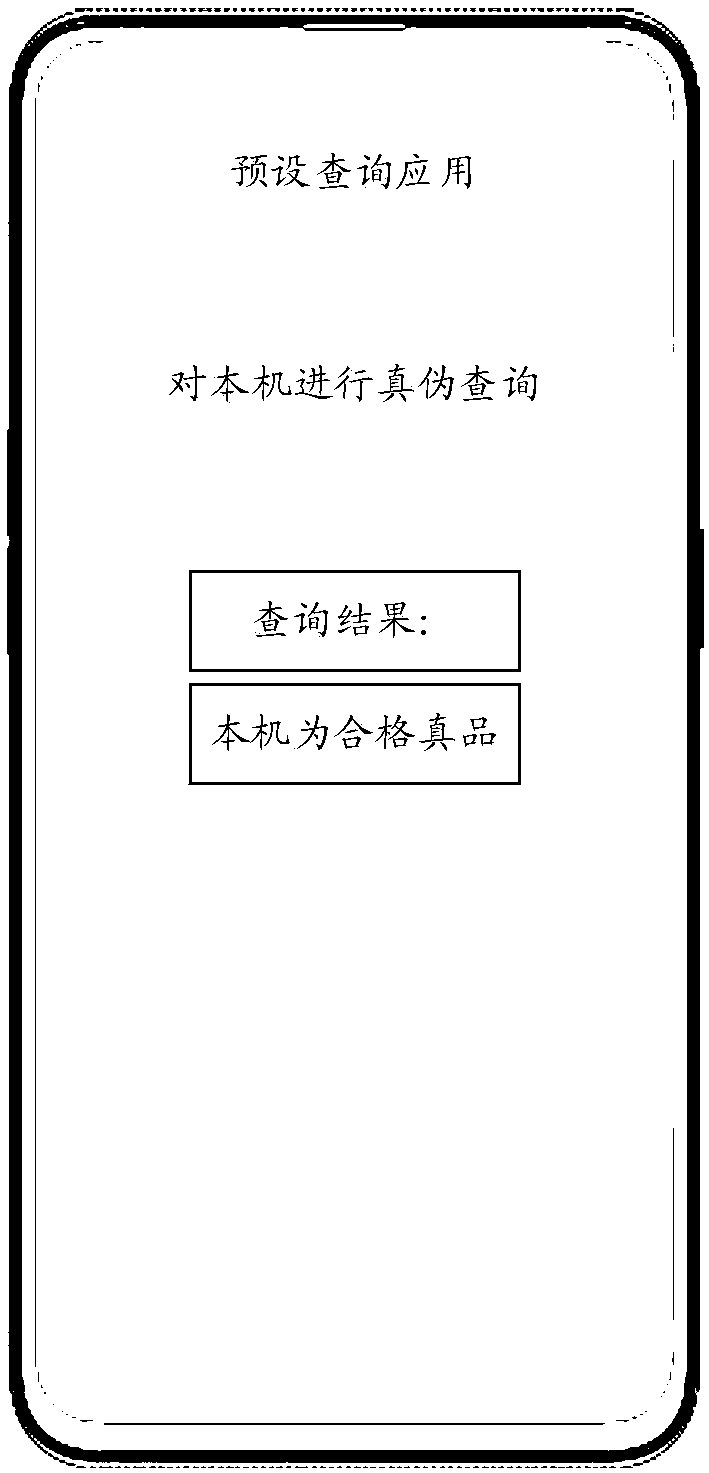
[0050] The technical solutions in the embodiments of the present application will be clearly and completely described below in conjunction with the drawings in the embodiments of the present application. It should be understood that the specific embodiments described here are only used to explain the related application, not to limit the application. It should also be noted that, for the convenience of description, only the parts related to the relevant application are shown in the drawings.
[0051] Existing terminal authenticity query methods mainly include International Mobile Equipment Identity (IMEI) query, identification of machine packaging and manuals, identification of network license certificate numbers, and identification of terminal appearance and accessories. Among them, the IMEI code query method is to enter the IMEI code into the official website for query; when identifying the outer packaging and manual of the machine, the packaging and manual based on the regu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More