A credential stuffing attack monitoring method, device, system and computer storage medium
A business system and behavior technology, applied in the Internet field, can solve the problems of low ability to identify credential stuffing attacks, increase the difficulty of normal user login, and affect normal business development, so as to reduce the impact and improve the ability to identify.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
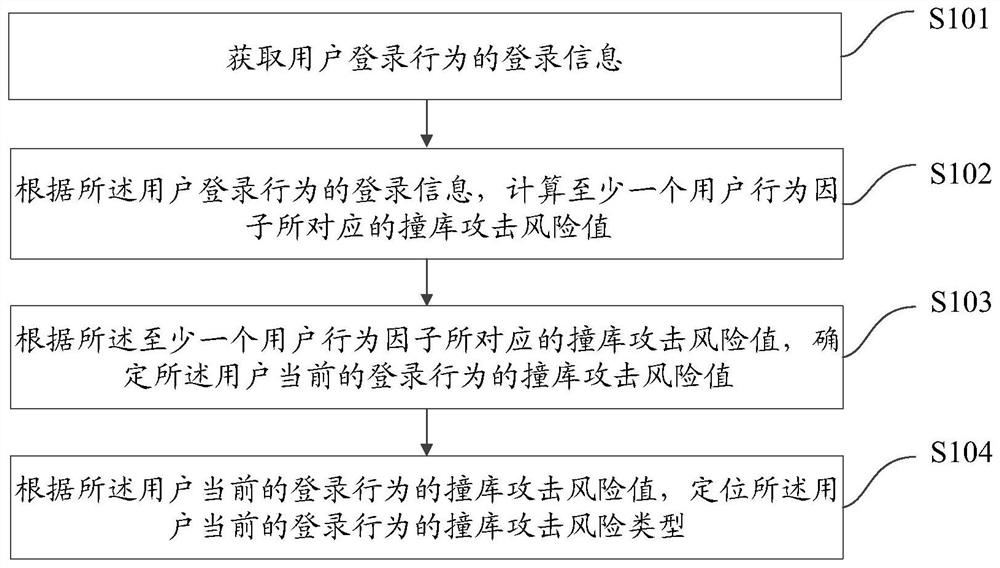
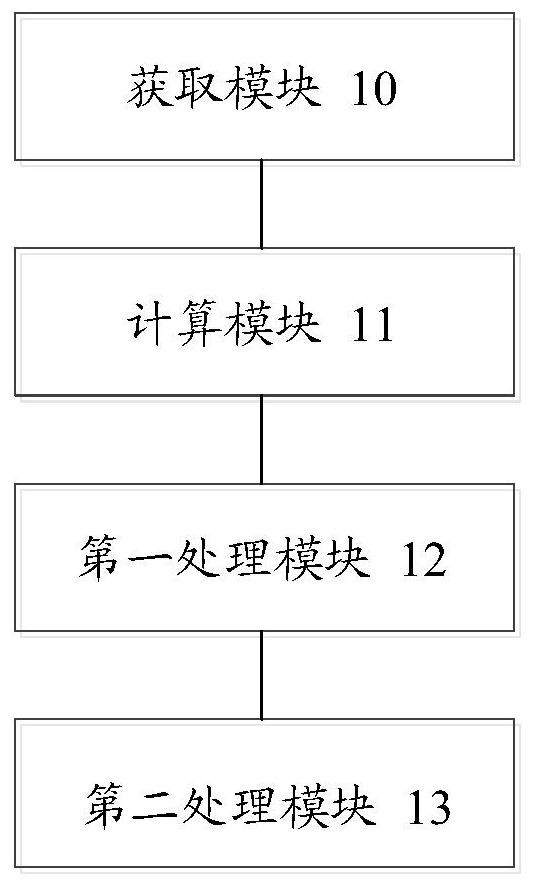
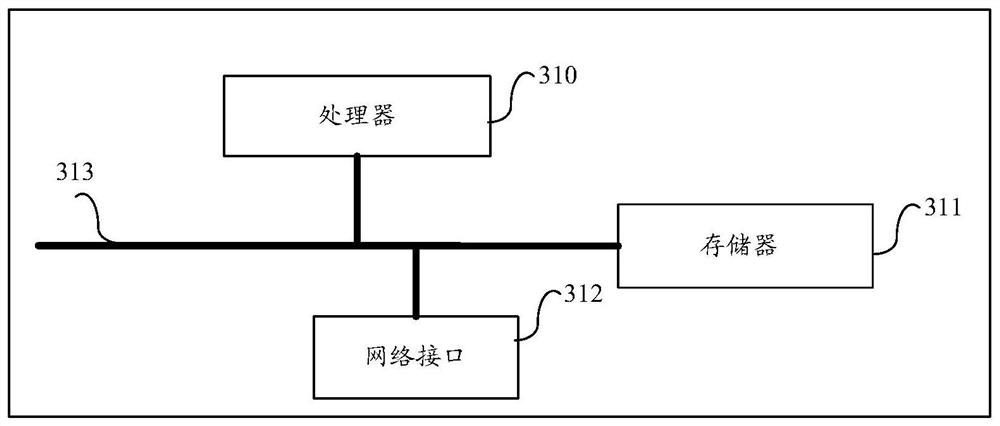
Method used
Image
Examples
Embodiment Construction
[0107] The technical solutions of the present invention will be further described in detail below in conjunction with the drawings and specific embodiments of the description. Unless otherwise defined, all technical and scientific terms used herein have the same meaning as commonly understood by one of ordinary skill in the technical field of the invention. The terms used herein in the description of the present invention are for the purpose of describing specific embodiments only, and are not intended to limit the present invention. As used herein, the term "and / or" includes any and all combinations of one or more of the associated listed items.
[0108]Credential stuffing attack is a way to obtain a series of user account information that can be logged in by collecting user names and login password information leaked from A business and generating corresponding dictionary tables, and trying to log in to B business and other businesses in batches. When hackers attack, they o...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More