Suspicious transaction message generation method and device and server
A transaction message, suspicious technology, applied in the computer field, can solve problems such as prone to missing writing, time-consuming and labor-intensive, and achieve the effect of avoiding message connection and reducing complexity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
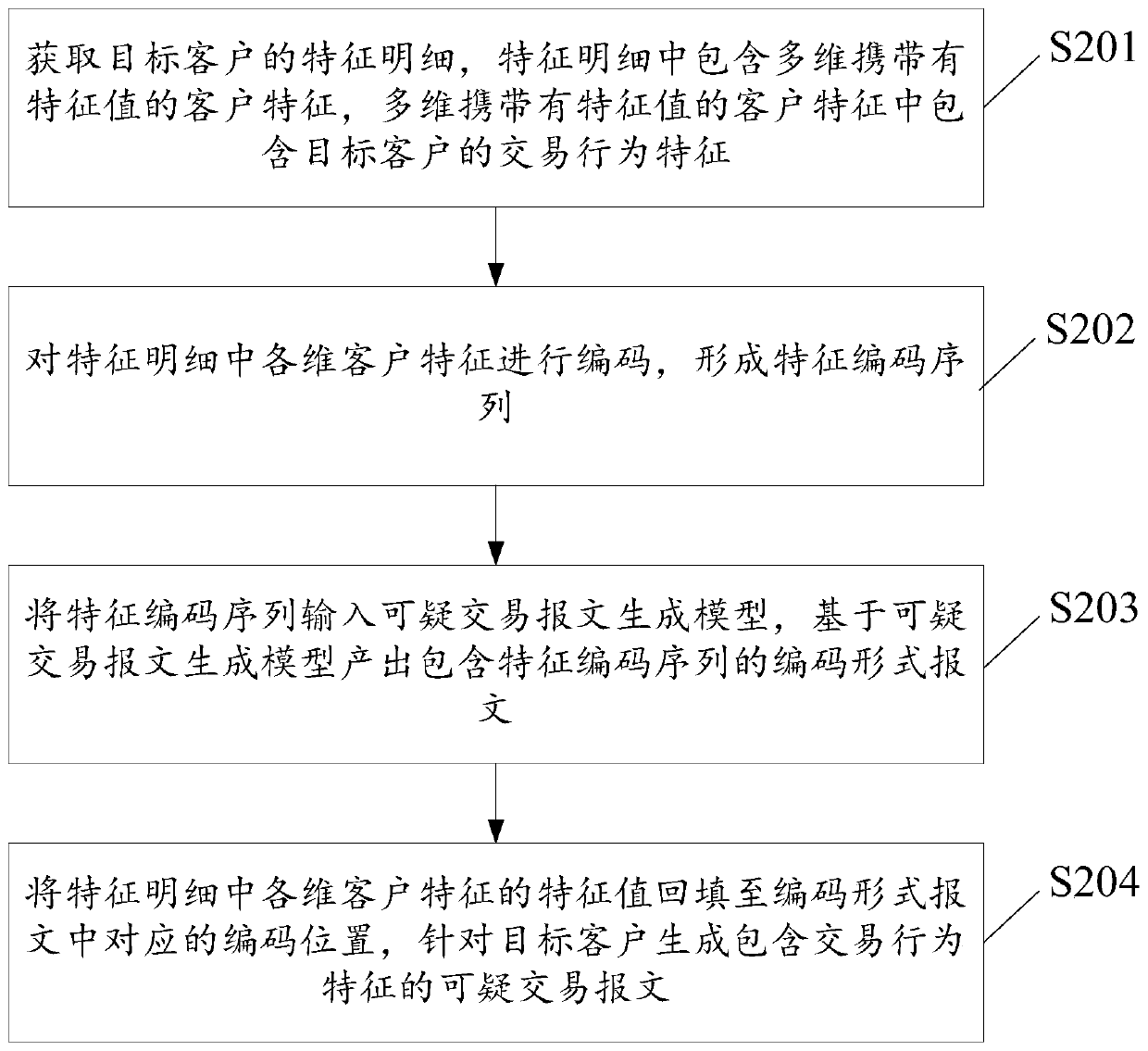
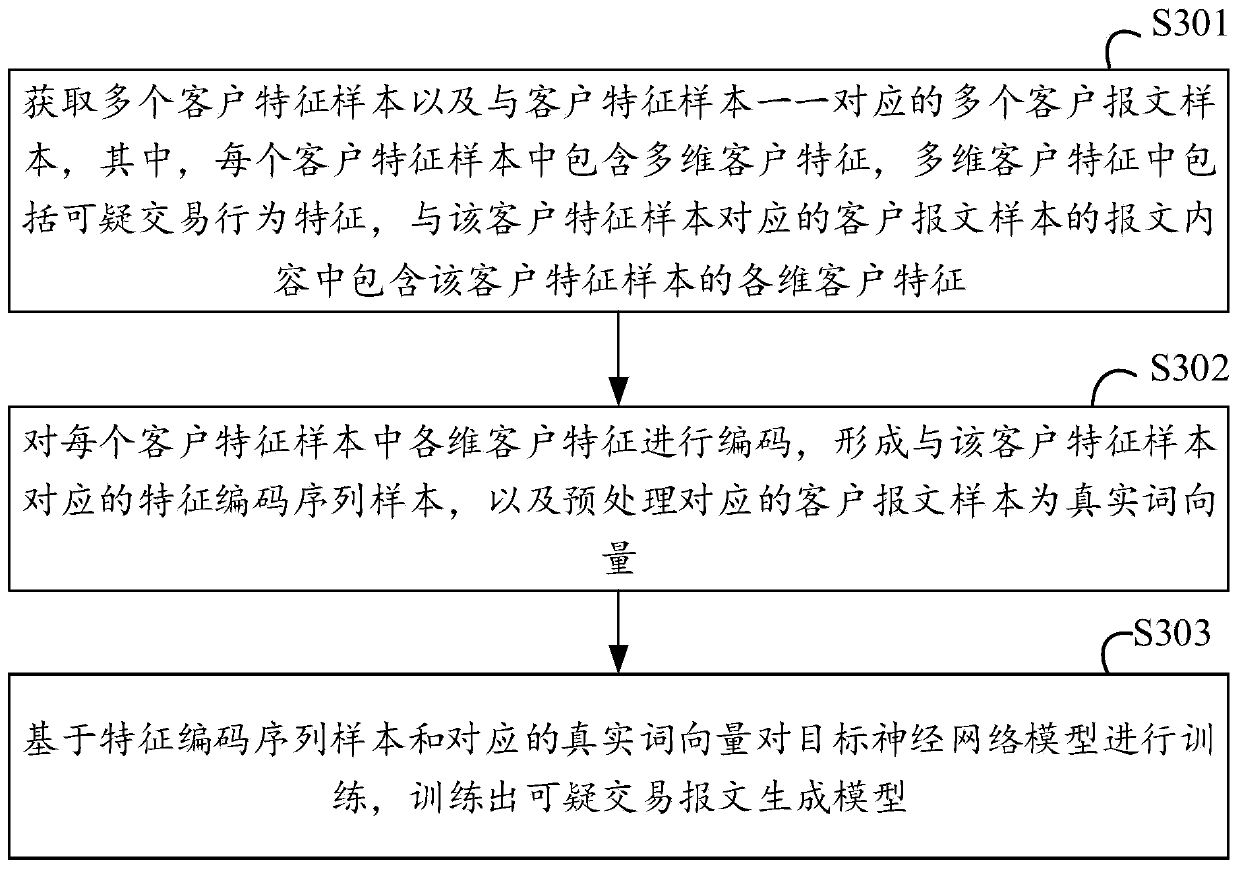
[0016] In order to better understand the above technical solutions, the technical solutions of the embodiments of this specification will be described in detail below through the drawings and specific examples. It should be understood that the embodiments of this specification and the specific features in the embodiments are the technical solutions of the embodiments of this specification. It is a detailed description, rather than a limitation to the technical solutions of this specification. In the case of no conflict, the embodiments of this specification and the technical features in the embodiments can be combined with each other.
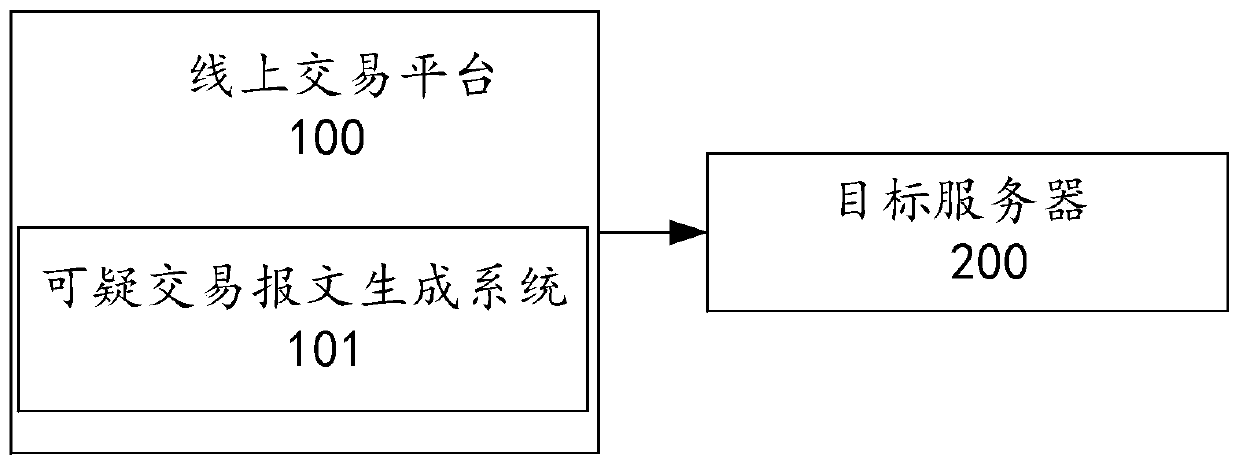
[0017] See figure 1 , is a schematic diagram of a scenario of a method for generating a suspicious transaction message in an embodiment of this specification. Online trading platform 100. For example, third-party payment platforms and online shopping platforms. The suspicious transaction message generation system 101 is configured to generate...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More