Method and device for authority management in operation and maintenance management system based on key
A technology of operation and maintenance management and authority management, applied in the direction of digital data authentication, etc., to achieve the effect of improving security and concealment, improving standardization and privacy, and ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
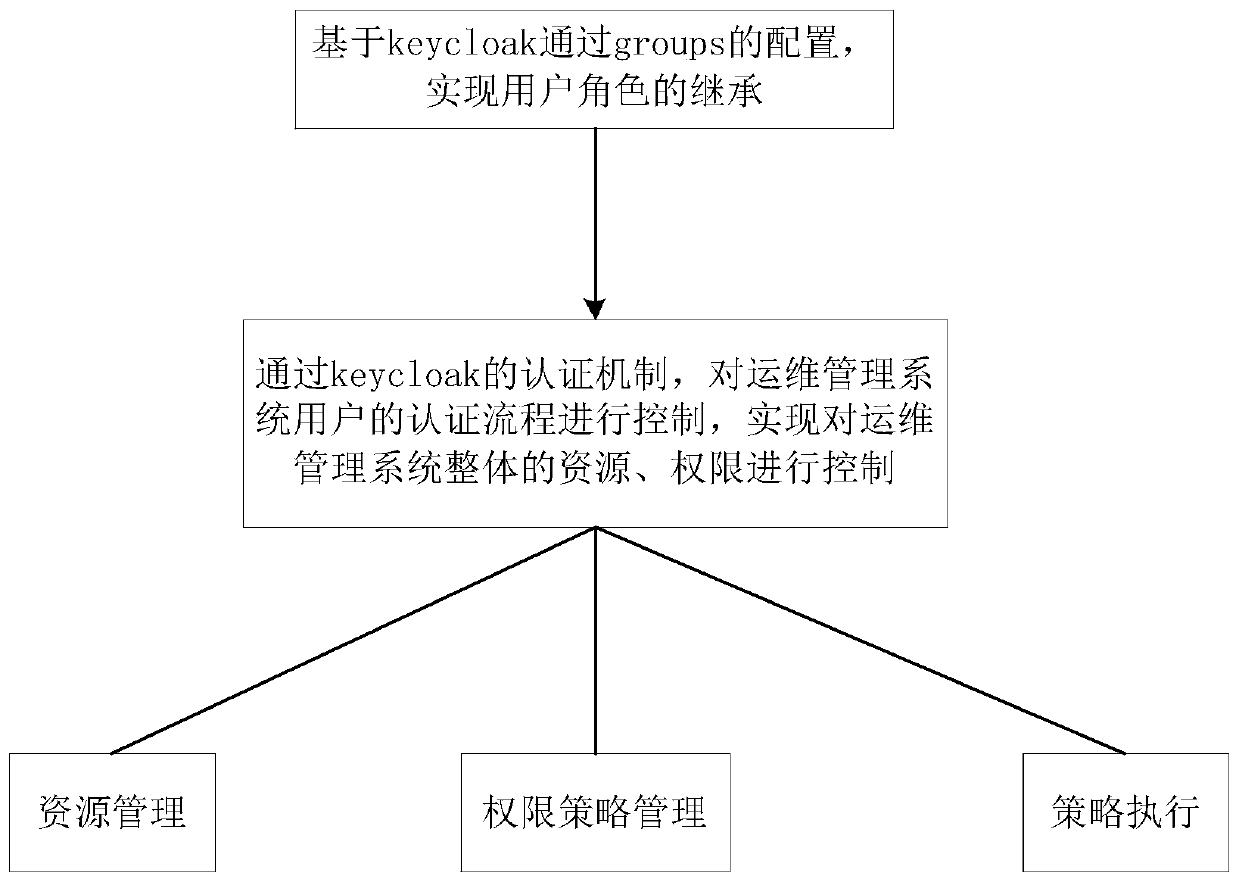
[0050] as attached figure 1 As shown, the method for authority management in the operation and maintenance management system based on keycloak of the present invention, the method steps are as follows:
[0051] S1. Realize the inheritance of user roles through the configuration of groups based on keycloak;
[0052] S2. Through the keycloak authentication mechanism, the authentication process of the operation and maintenance management system user is controlled to realize the overall resource and authority control of the operation and maintenance management system, including:
[0053] S201. Resource management;
[0054] S202. Authority policy management;
[0055] S203. Policy execution.
[0056] In step S1, based on keycloak through the configuration of groups, the specific steps to realize the inheritance of user roles are as follows:
[0057] S101, enter the keycloak management page, and create realms, clients, groups, and user roles in keycloak;
[0058] S102. Configure...
Embodiment 2
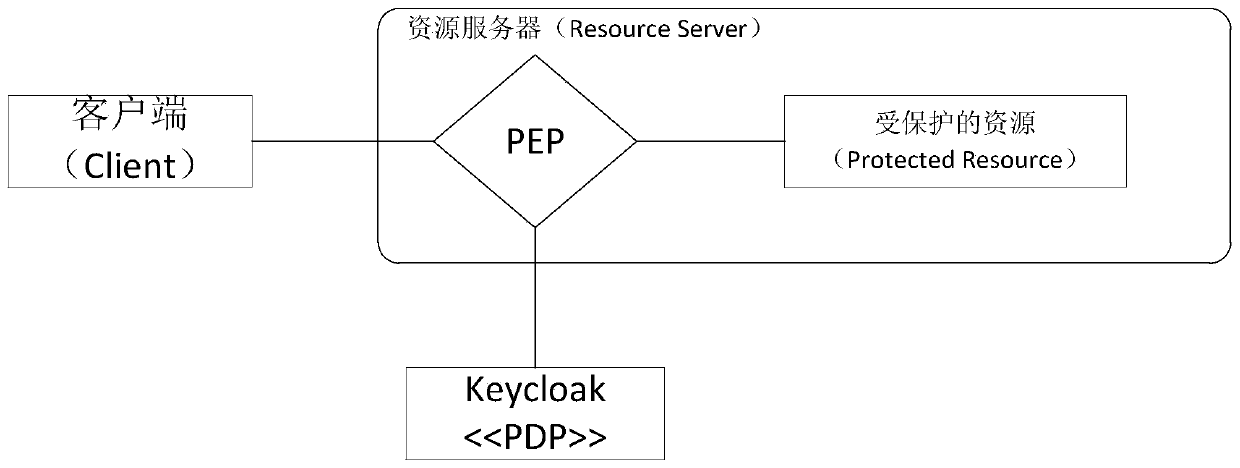
[0073] The device for authority management in the operation and maintenance management system based on keycloak of the present invention includes:
[0074] The user role inheritance unit is used to implement the inheritance of user roles through the configuration of groups based on keycloak;
[0075] The authentication process control unit is used to control the authentication process of the user of the operation and maintenance management system through the authentication mechanism of keycloak, so as to control the overall resources and permissions of the operation and maintenance management system.
[0076] The certification process control unit includes,
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More