Login verification method and system
A technology for login verification and user terminal, applied in the field of information security, can solve problems such as easy to forget passwords, and achieve the effect of improving security and convenience and ensuring security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0041] In order to have a clearer understanding of the technical features, purposes and effects of the present invention, the specific implementation manners of the present invention will be described in detail below with reference to the accompanying drawings. It should be understood that the following descriptions are only specific illustrations of the embodiments of the present invention, and should not limit the protection scope of the present invention.
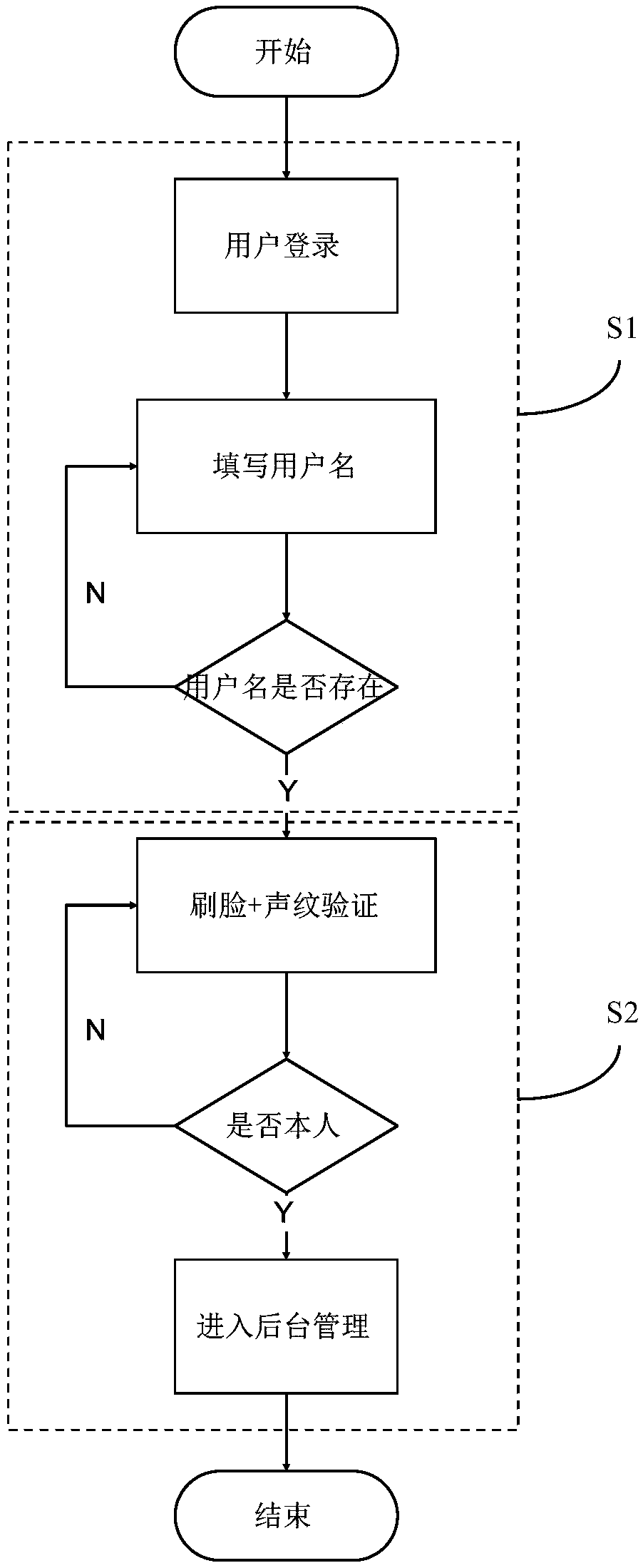
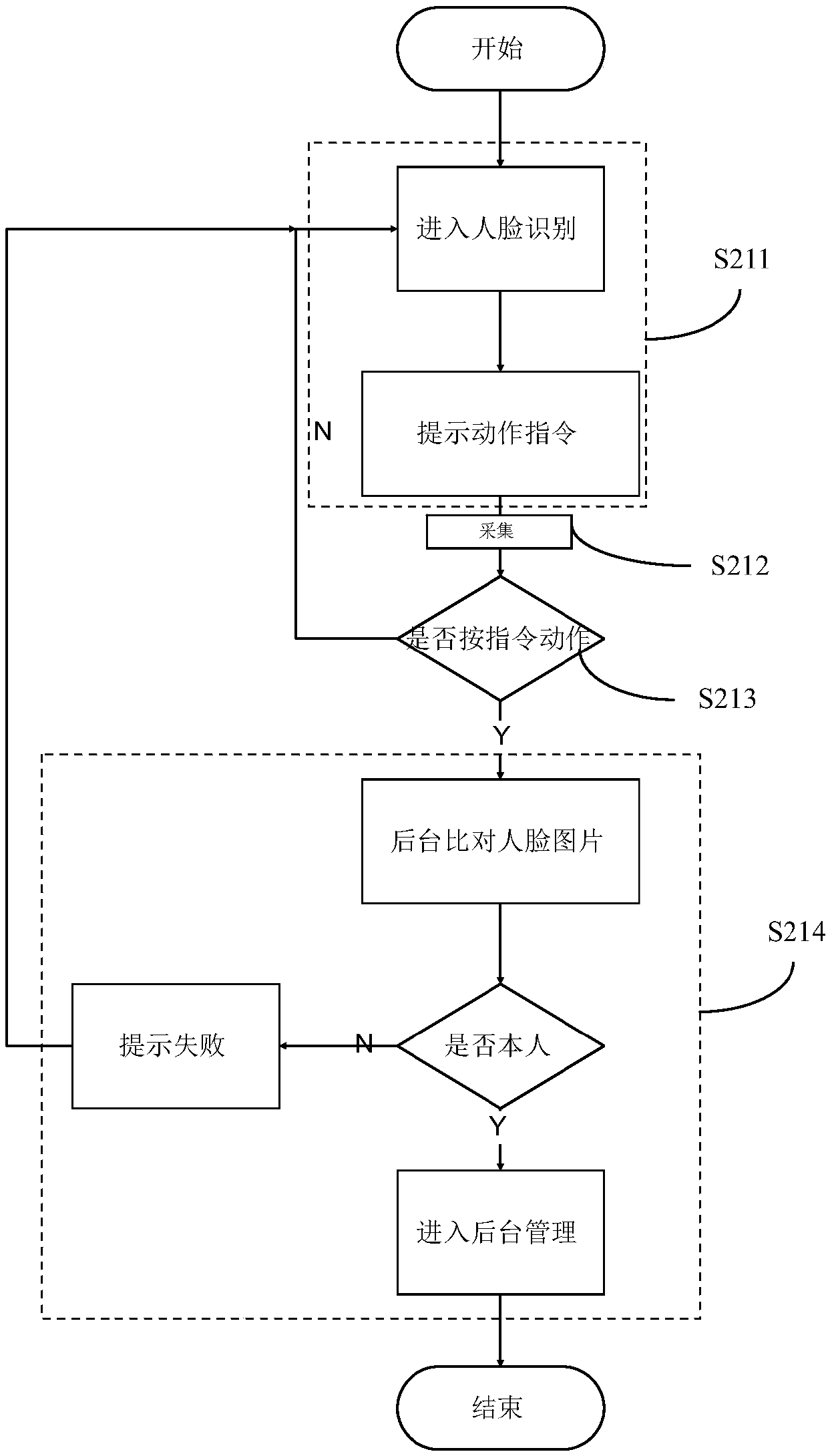
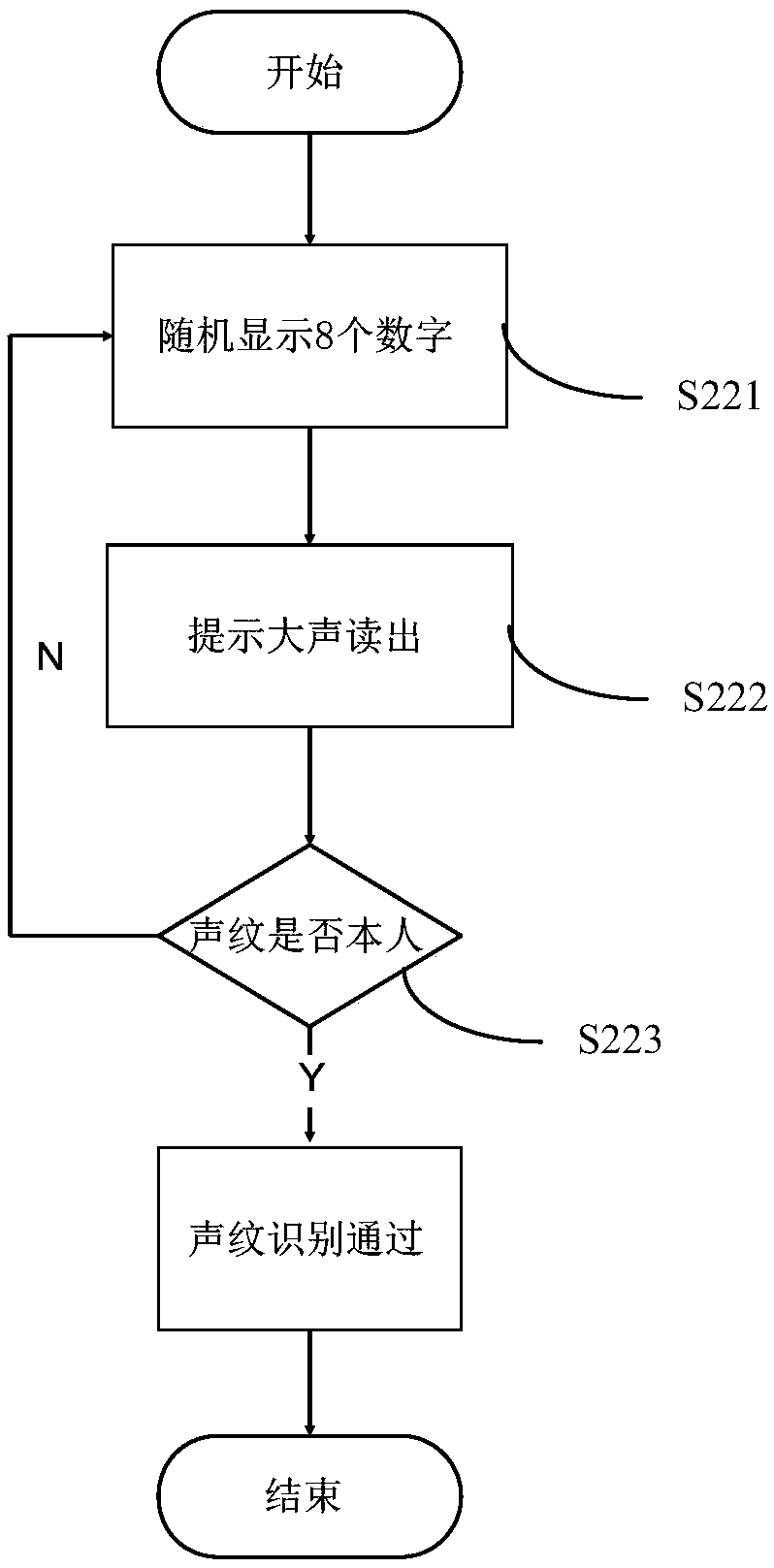
[0042] see figure 1 , figure 1 A flow chart of a login verification method provided by an embodiment of the present invention, the method includes steps S1-S2:
[0043] S1. Input the user account through the client terminal, and verify whether the user account exists through the background server, and if it exists, enter step S2; the step S1 includes steps S11-S12:
[0044] S11. Open a login interface in the user terminal to prompt the user to input a user account; for example, the user opens the login page and first i...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap