A key detection method, device and electronic equipment
A detection method and key technology, applied in the computer field, can solve the problems of high detection risk and low recognition accuracy, and achieve the effects of avoiding data leakage, improving security, and improving accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
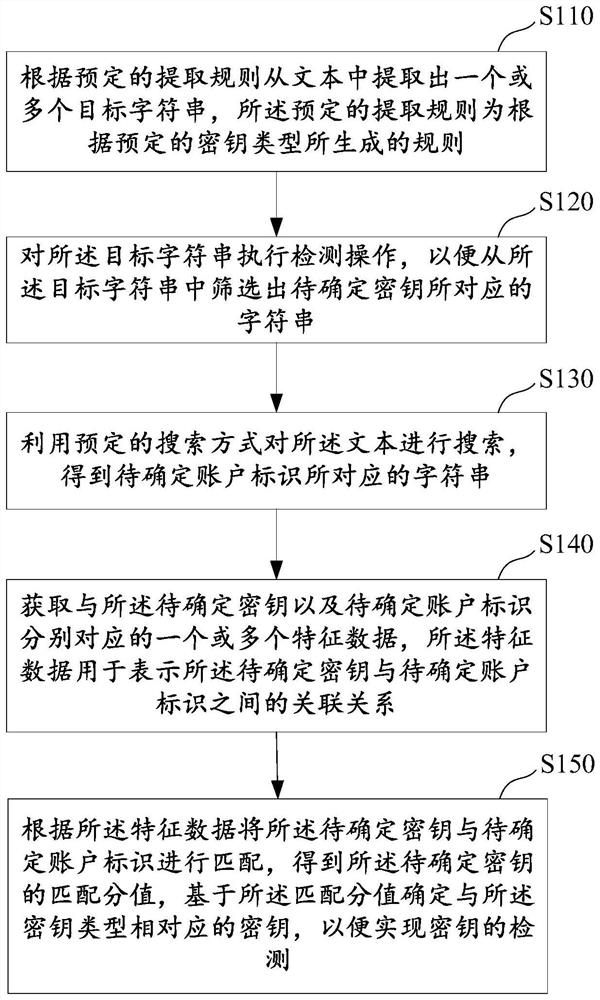
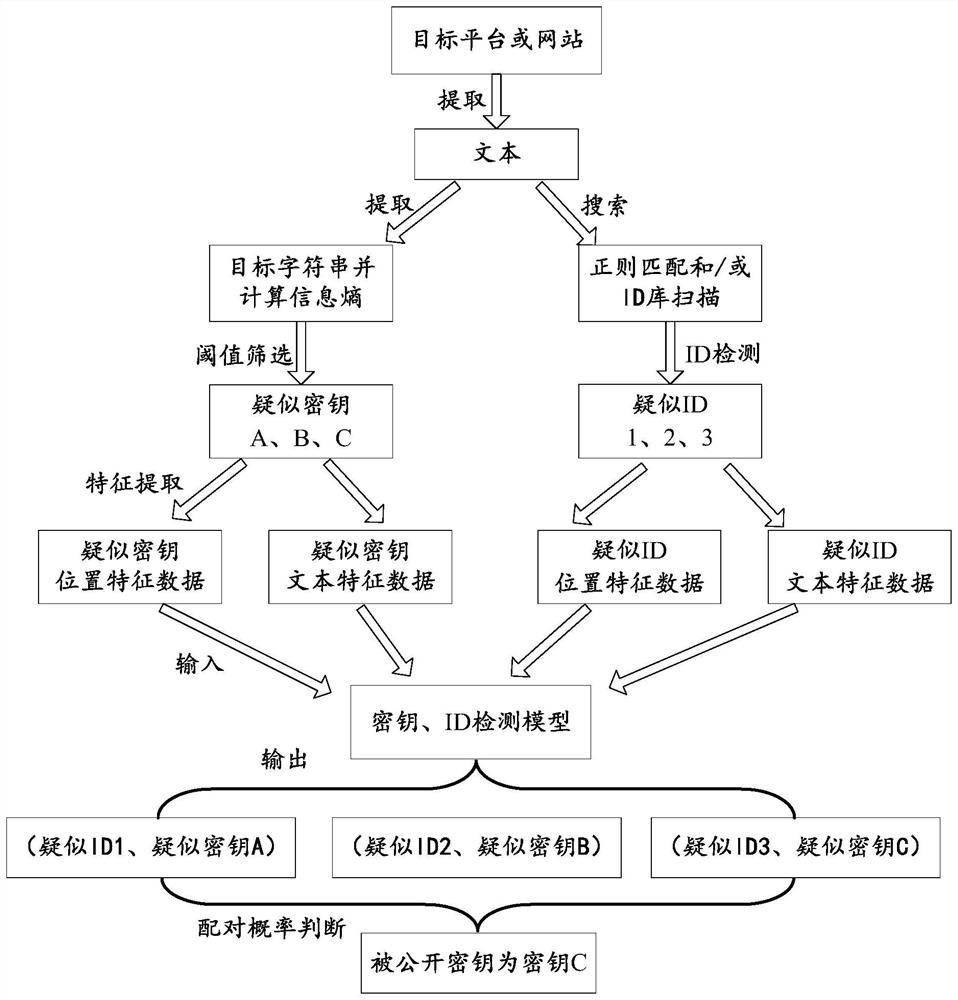
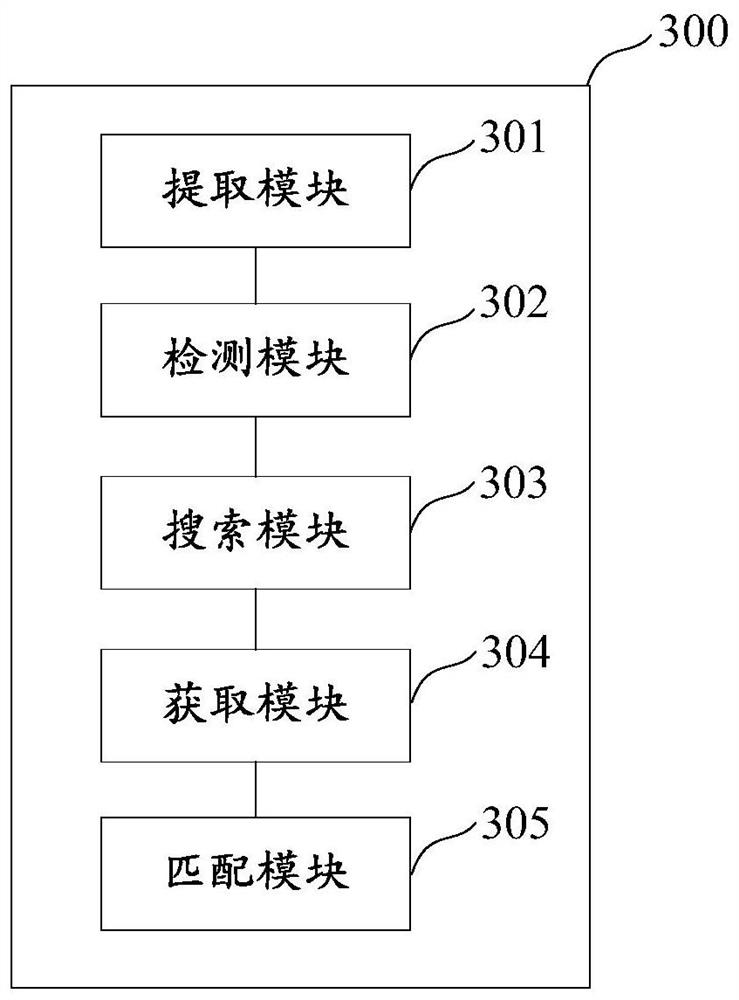
[0026] In order to make those skilled in the art better understand the technical solutions in this specification, the technical solutions in the embodiments of this specification will be clearly and completely described below with reference to the accompanying drawings in the embodiments of this specification. Obviously, the described The embodiments are only a part of the embodiments of the present application, but not all of the embodiments. Based on the embodiments of the present specification, all other embodiments obtained by persons of ordinary skill in the art without creative efforts shall fall within the protection scope of the present application.
[0027] With the rapid development of Internet technology, service applications and platforms based on Internet technology are also changing with each passing day, but Internet security has always been one of the most concerned topics for users, so the research on Internet security has never stopped. In order to ensure the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More