Encryption method, decryption method, device and equipment based on encryption proxy gateway
A proxy gateway and encryption method technology, applied in the direction of secure communication devices, computer security devices, network connections, etc., can solve the problems of large development workload, low version update efficiency, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
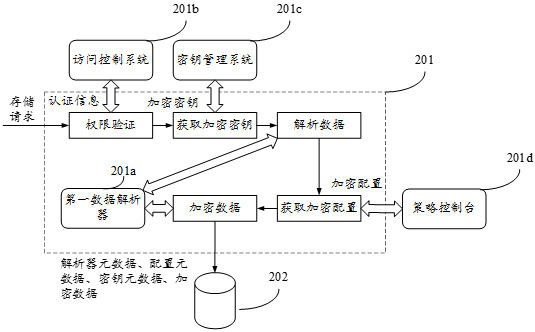
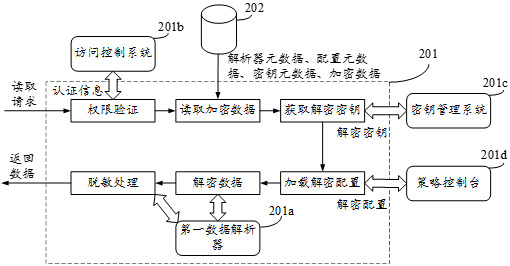
[0095] In order to make the purpose, technical solution and advantages of the present application clearer, the implementation manners of the present application will be further described in detail below in conjunction with the accompanying drawings.
[0096] In order to facilitate the understanding of the methods provided in the embodiments of the present application, terms involved in the embodiments of the present application are firstly introduced.
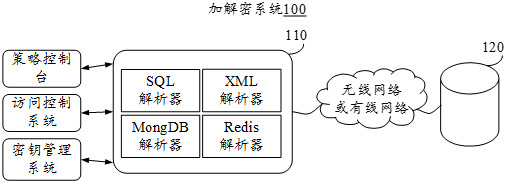
[0097] Cloud computing (Cloud Computing) is a computing model that distributes computing tasks on a resource pool composed of a large number of computers, enabling various application systems to obtain computing power, storage space, and information services as needed. The network that provides resources is called a "cloud". From the user's point of view, the resources in the "cloud" can be infinitely expanded, and can be obtained at any time, used on demand, expanded at any time, and paid according to use. The encryption prox...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More