Method for realizing session sharing and asynchronous-to-synchronous conversion by Redis
An asynchronous, user-terminal technology applied in the computer field to prevent data theft and protect login security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
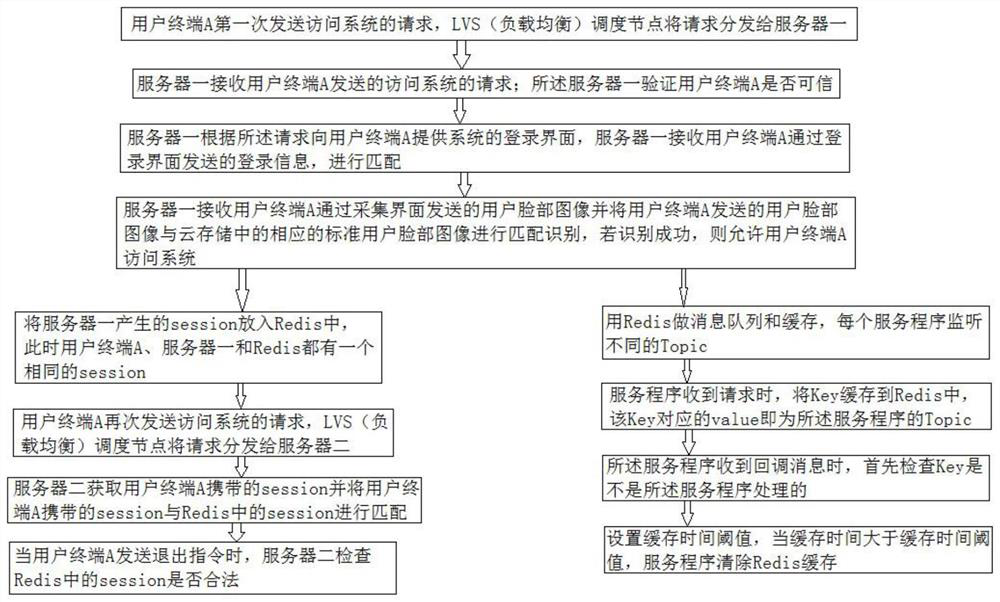
[0051] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
[0052] Such as figure 1 As shown, Redis implements session sharing and asynchronous to synchronous methods, including the following steps:
[0053] Step 1: User terminal A sends a request to access the system for the first time, and the LVS (load balancing) scheduling node distributes the request to server 1;
[0054] Step 2: Server 1 receives the request for accessing the system sent by user terminal A; said server 1 verifies whether user terminal A is credible, ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More