Code virtualization encryption method, terminal and storage medium
An encryption method and storage medium technology, applied in the field of code virtualization encryption method, terminal and storage medium, can solve problems such as memory DUMP
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0031] In order to make the object, technical solution and advantages of the present invention more clear and definite, the present invention will be further described in detail below with reference to the accompanying drawings and examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
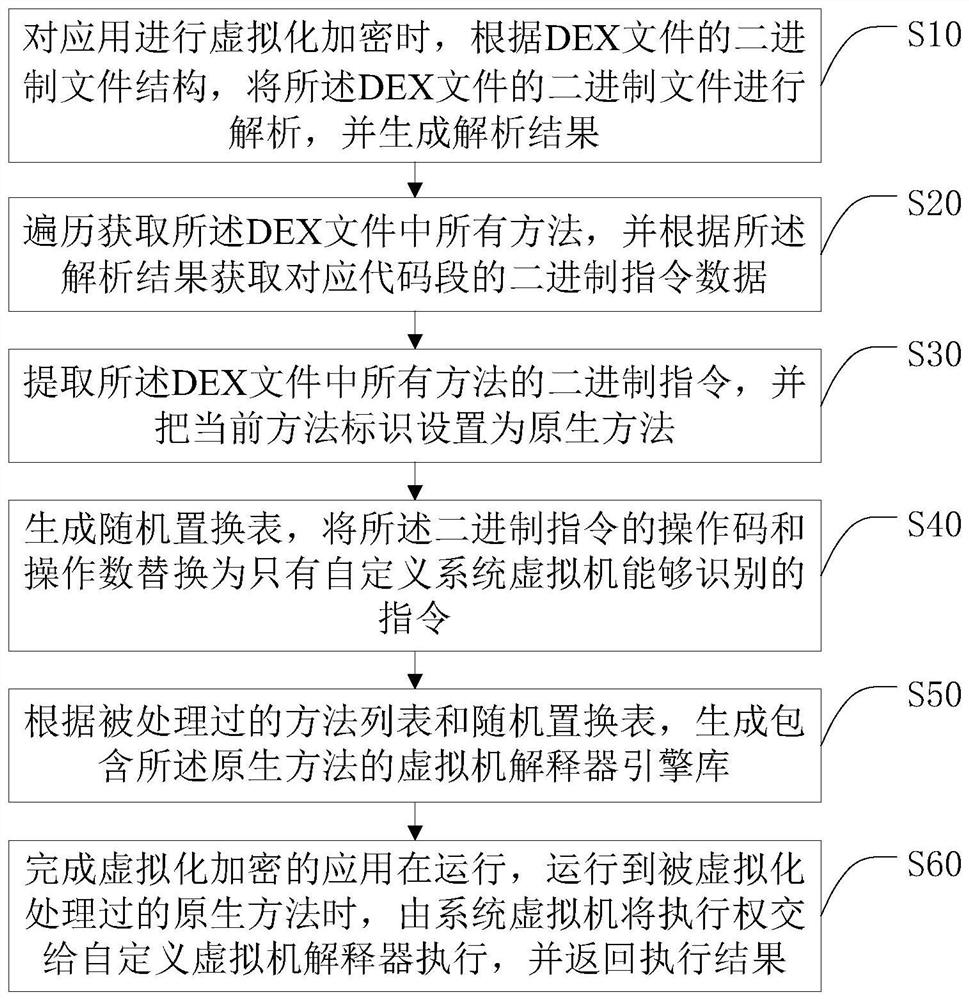
[0032] The code virtualization encryption method described in the preferred embodiment of the present invention, such as figure 1 As shown, the code virtualization encryption method includes the following steps:
[0033] Step S10 , when virtualizing and encrypting the application, analyze the binary file of the DEX file according to the binary file structure of the DEX file, and generate an analysis result.
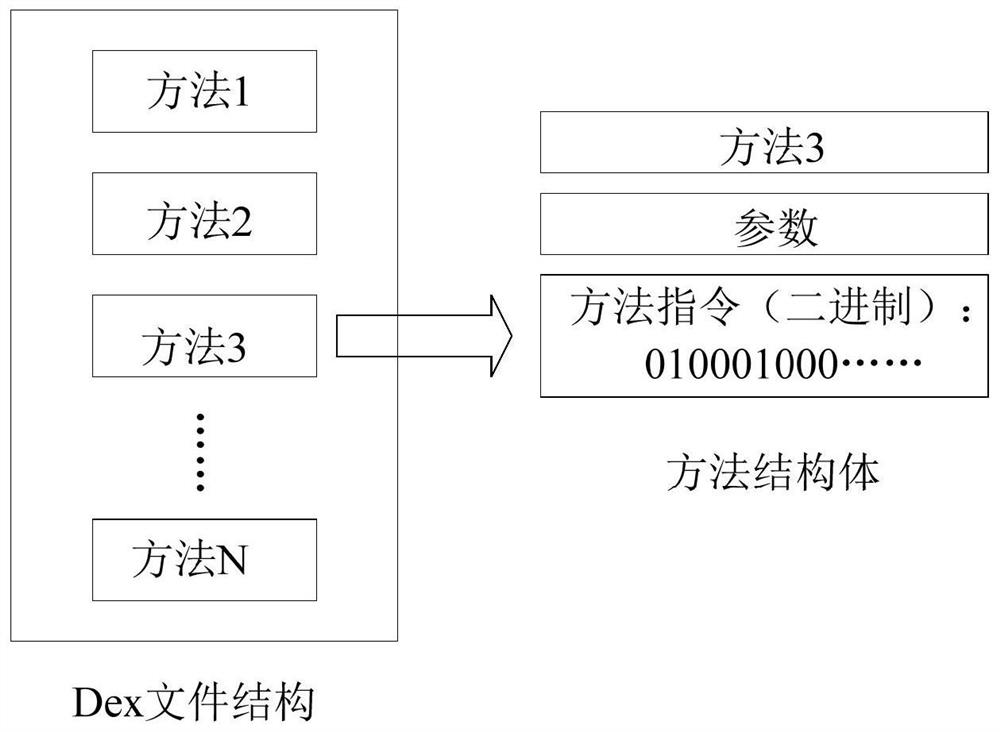
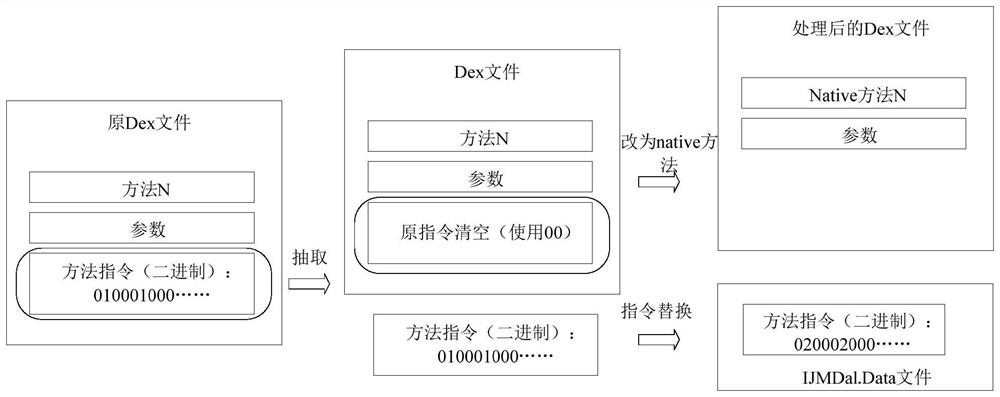
[0034] Specifically, when the application is virtualized and encrypted, the binary file of the DEX file is analyzed according to the binary file structure of the DEX file (the DEX ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More