Control method of mobile terminal, mobile terminal and storage medium
A mobile terminal and control method technology, which is applied in the field of mobile terminal control, mobile terminal and storage media, can solve problems such as cumbersome application management steps of avatars, and achieve the effect of simplifying management steps
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
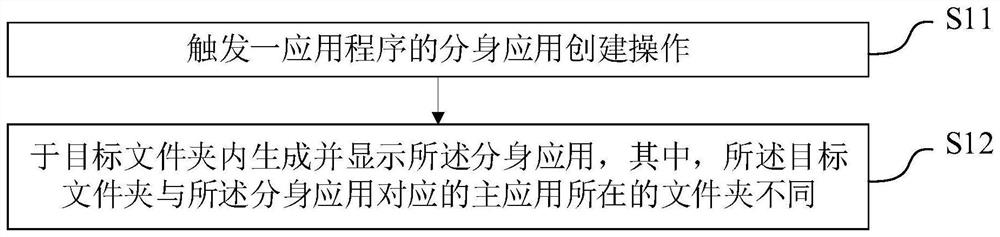
[0084] refer to image 3 , in the first embodiment, the control method of the mobile terminal includes the following steps:
[0085] Step S11, triggering an application creation operation of an application program;
[0086] In step S12, the avatar application is internally generated and displayed. Optionally, the target folder is different from the folder where the main application corresponding to the avatar application is located.
[0087] The above-mentioned control method of the mobile terminal is applied to the mobile terminal.
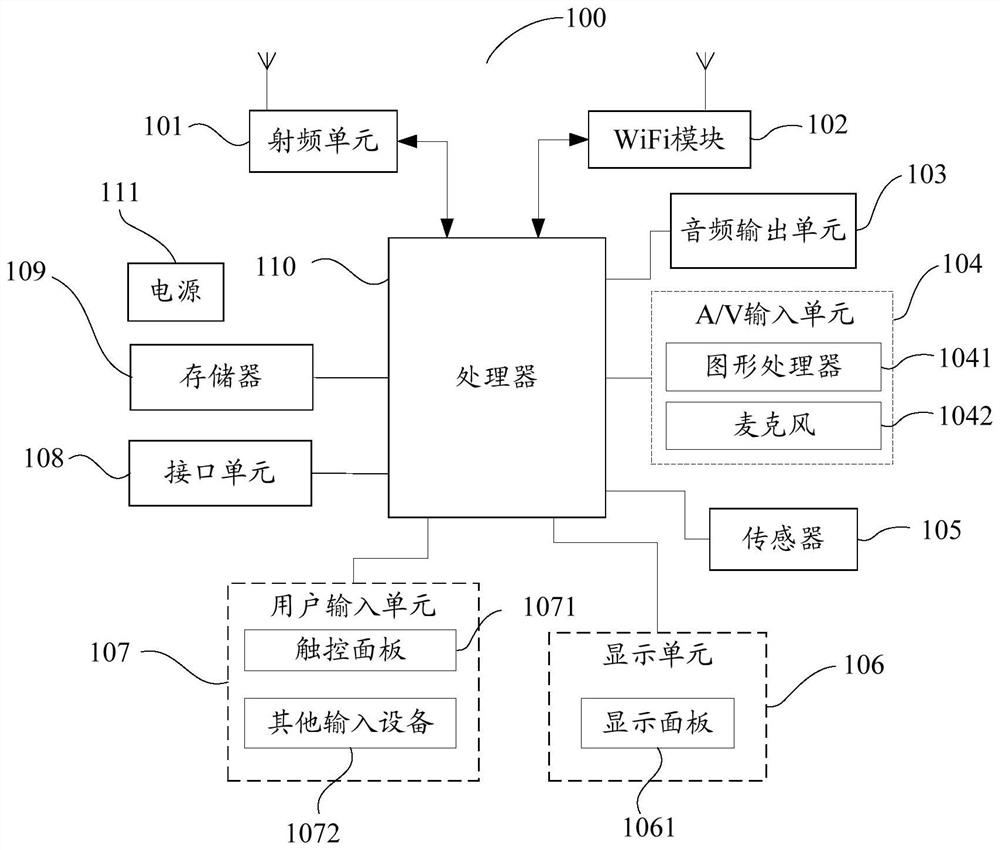
[0088] Exemplarily, the mobile terminal may be a mobile terminal such as a mobile phone, a tablet computer, a notebook computer, an ultrabook and / or a game console. The mobile terminal may be an intelligent mobile terminal that implements a response function based on systems such as an Android system, an ios system, and / or a Windows system. The mobile terminal is also provided with an application program loading function, so that the mobile te...
example 1
[0118] Example 1, when receiving a control operation of long-pressing a blank space on the desktop, the output can be as follows Figure 4 The nine-square pattern drawing page shown. for user authentication. When the received pattern is the preset pattern, it is determined that the authentication information is legal.
example 2
[0119] Example 2, when a preset control action is received, a prompt message may be output to prompt the user to input a fingerprint. When the fingerprint input by the user is a preset fingerprint, it is determined that the identity verification information is legal.
[0120] It should be noted that, in this example, the verification information may be set to be the same as the screen unlocking data. Or set to be independent of screen unlock data.
[0121] Optionally, when the mobile terminal also includes avatar applications created in other ways, the avatar applications located in other locations other than the target folder can be moved to the target through drag and drop or other control methods. inside the folder.
[0122] Optionally, the display settings of the new message corresponding to the avatar application include at least one of the following:
[0123] Selectively enable or disable the function of displaying the new message in the foreground when the cloned app...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More