Access method, system and device based on multiple security protocols and medium
A security protocol and access method technology, applied in the field of computer software, can solve the problems of data leakage, protocol incompatibility, inconvenient network transmission and storage, etc., and achieve the effect of low cost, low consumption, avoiding garbled characters and parsing errors
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] Embodiments of the present invention are described in detail below, and examples of the embodiments are shown in the drawings, wherein the same or similar reference numerals denote the same or similar elements or elements having the same or similar functions throughout. The embodiments described below by referring to the figures are exemplary only for explaining the present invention and should not be construed as limiting the present invention. For the step numbers in the following embodiments, it is only set for the convenience of illustration and description, and the order between the steps is not limited in any way. The execution order of each step in the embodiments can be adapted according to the understanding of those skilled in the art sexual adjustment.
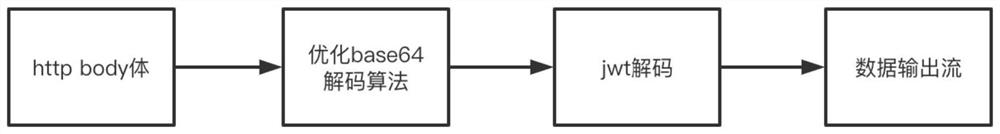
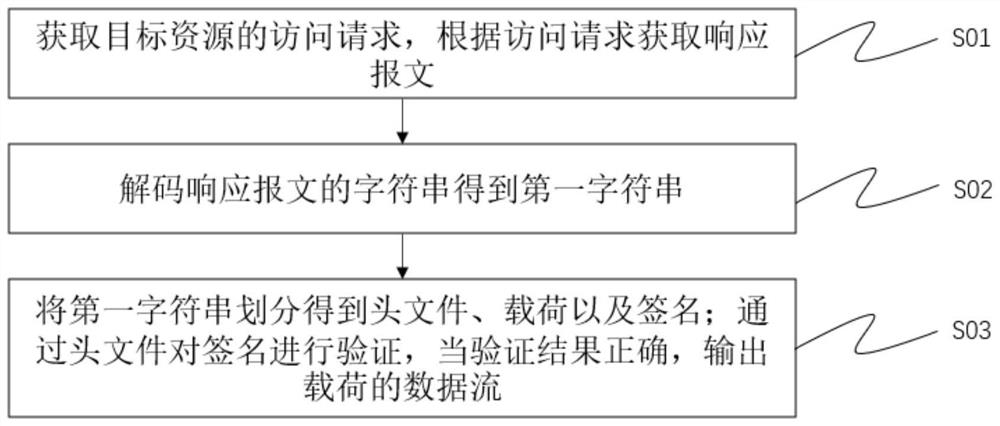
[0036] The core ideas of the technical solutions provided by the embodiments of the present invention, such as figure 1 As shown, based on the optimized base64 encoding and decoding algorithm, single sign-on ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More