Android application detection and analysis method, electronic device and storage medium
A local and instructional technology, applied in the field of computer security, can solve problems such as user privacy leakage, user property loss, and program crashes
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
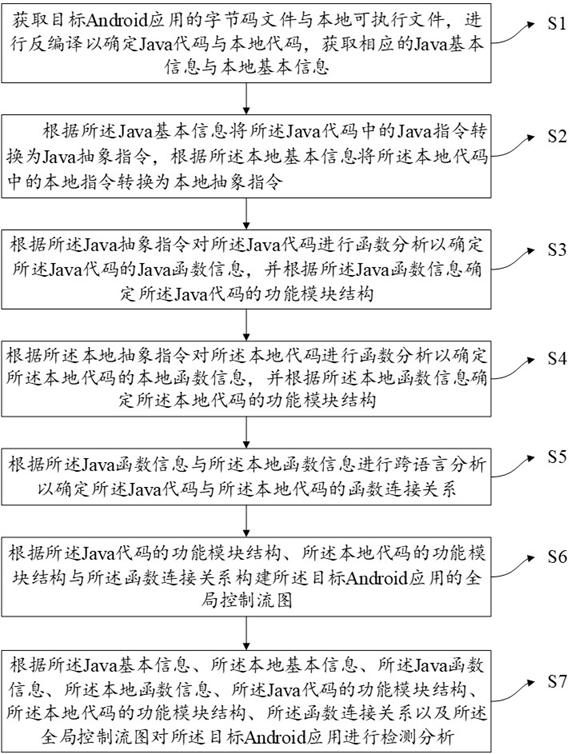
Method used
Image
Examples
Embodiment Construction
[0023] In order to make the objects, technical solutions, and advantages of the present disclosure, the present disclosure will be described in detail below with reference to the accompanying drawings.
[0024] It should be noted that the technical terms or scientific terms used in the disclosed embodiments, unless otherwise defined, the technical terms used in the disclosure of which should be understood by those who have general skills in the art of the present disclosure. Similar words to "include" or "include", meaning that the elements or objects of the previously mentioned previously enumerated elements or objects that appear later in the word, without excluding other elements or objects. Similar words such as "Connect" or "Connect" are not limited to physical or mechanical connections, but may include electrical connections, whether direct or indirect. "On", "lower", "left", "right", etc., only to indicate the relative positional relationship, and the relative positional re...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More