Ldos attack detection and mitigation method based on fgd-fm in sdn
An attack detection and algorithm technology, which is applied in digital transmission systems, secure communication devices, electrical components, etc., can solve the problems of inability to detect and mitigate LDoS attacks, and achieve LDoS attack mitigation, good real-time performance, low false alarm rate and leakage The effect of rate of return
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
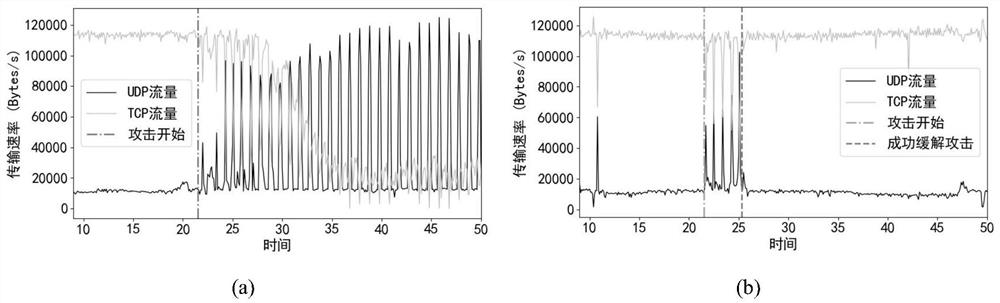
[0026] The LDoS attack detection and mitigation method based on FGD-FM in SDN is mainly divided into the following steps: data collection, attack detection and attack mitigation.
[0027] 1. Data collection. Fixed sampling time Time CW and the sampling interval Δt, the API of the control plane is called periodically based on the sampling interval within the sampling time to obtain the traffic sequence of the switch.
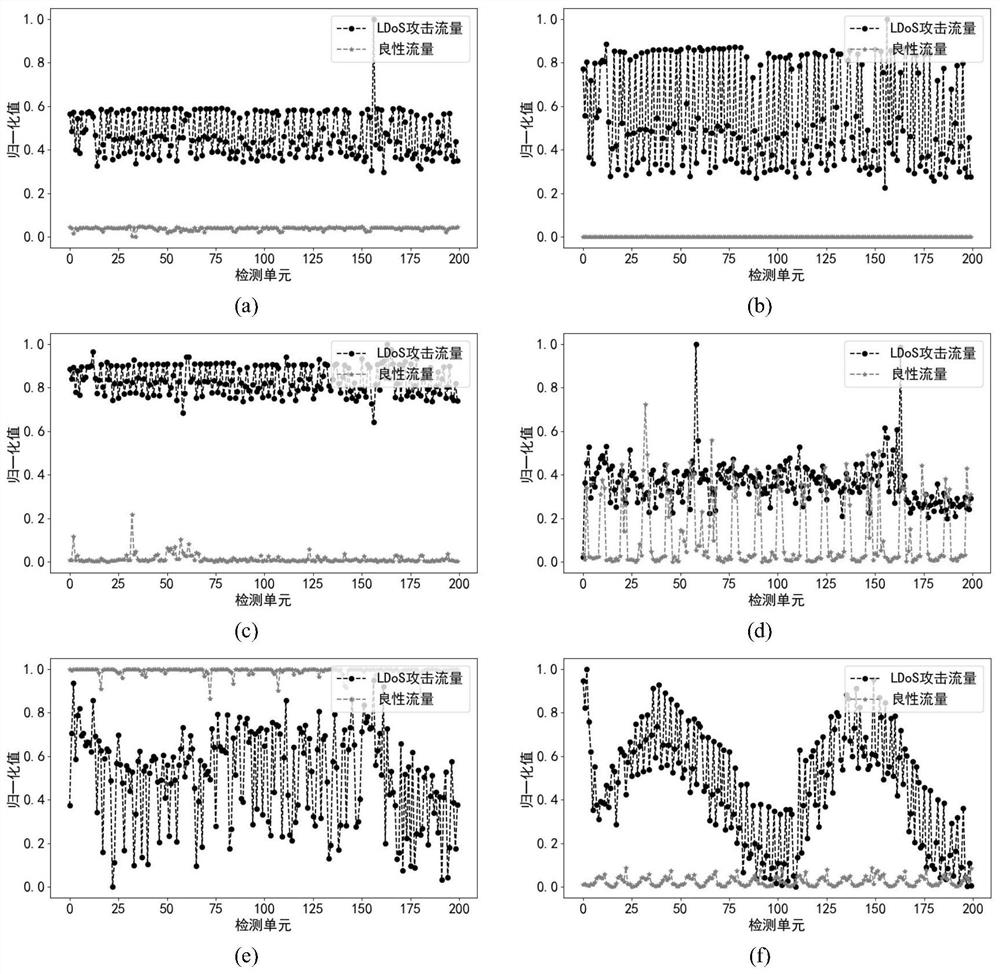
[0028] 2. Attack detection. Using the FGD method to implement fine-grained detection of LDoS attacks, the steps are as follows:
[0029] Step 2.1: Use the Needleman-Wunsch algorithm to collect the UDP (User Datagram Protocol, User Datagram Protocol) traffic sequence A=a 1 ,a 2 ,...,a n Each benchmark comparison vector B=b in the benchmark comparison matrix 1 ,b 2 ,...,b m Perform sequence comparison, and the period corresponding to the vector with the largest similarity score is the period Time of the LDoS attack DU .
[0030] (1) Define the similarity ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com