Method for detecting and resisting differential fault attack
A differential fault attack and differential fault technology, applied in the field of information security, can solve problems such as invalid infection prevention schemes, and achieve the effect of small amount of calculation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
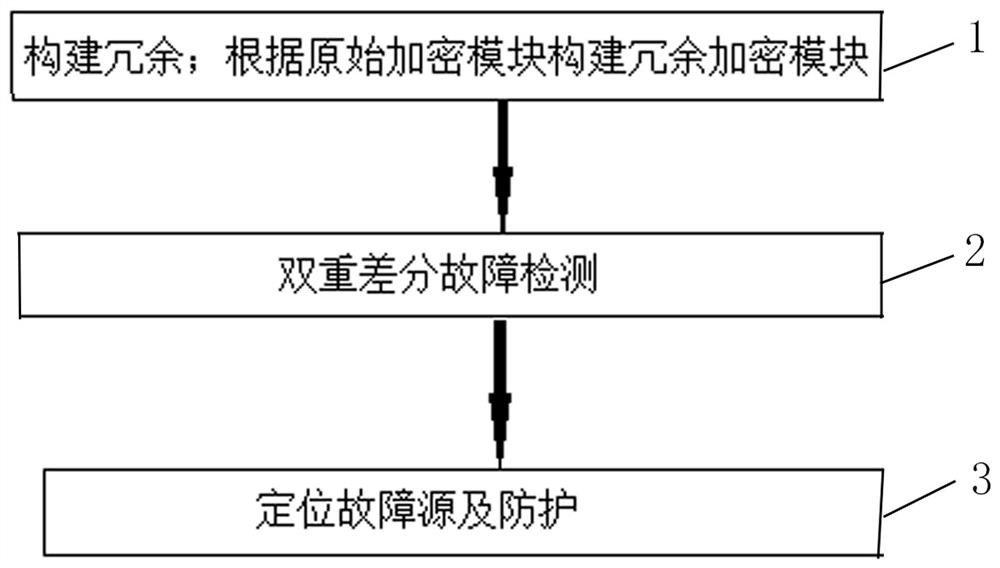
[0055] refer to figure 1 , the present invention is a method for detecting and defending against differential fault attacks, the method includes three parts:
[0056] (1) build redundancy; build a redundant encryption module according to the original encryption module;
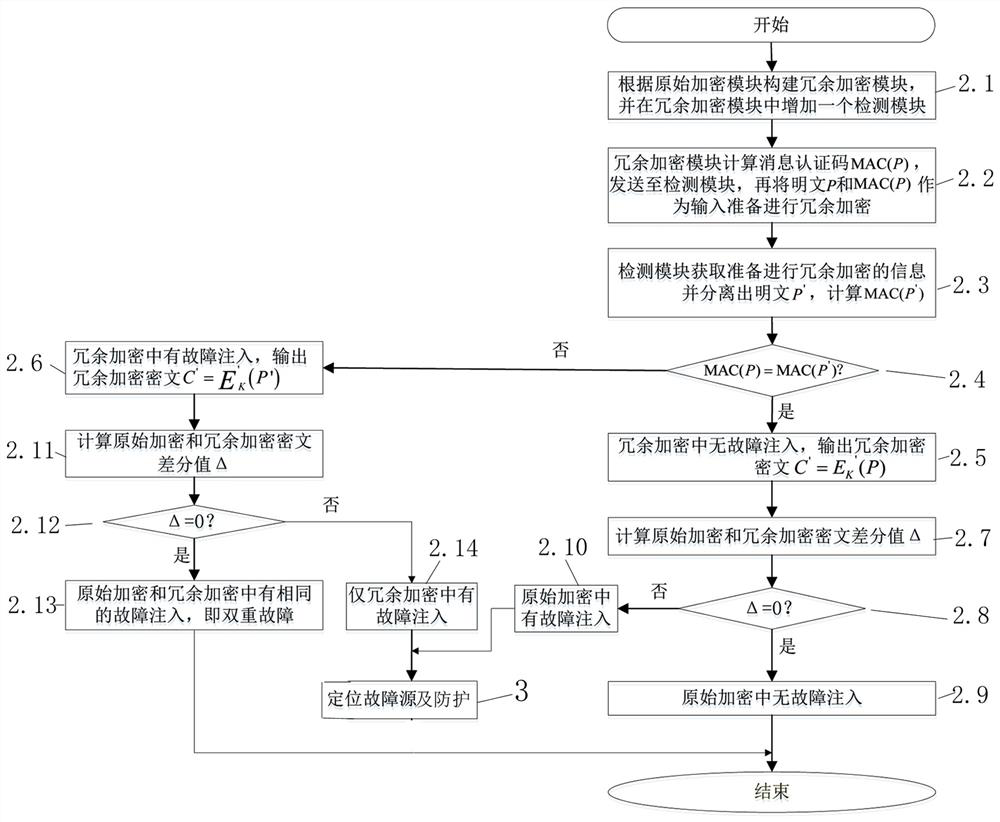
[0057] (2) Double differential fault detection;
[0058] Based on the message authentication code method, detect whether there is fault injection in the redundant encryption module, and compare it with the original encryption module to detect whether there is fault injection in the original encryption module, and complete the detection of double differential fault attack or differential fault attack;
[0059] (3) Locating the fault source and protection;
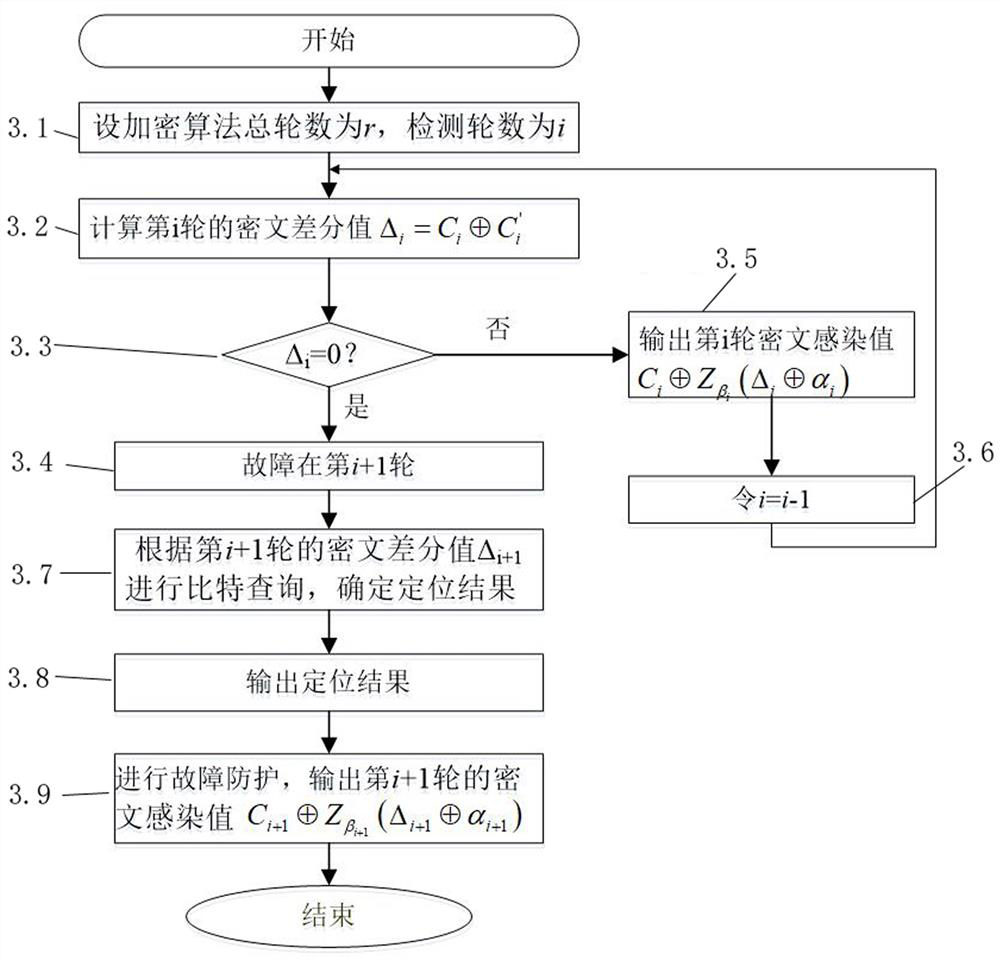
[0060] After determining the existence of differential fault injection, detect each round of ciphertext differential value of the target algorithm based on the ciphertext differential value and the infection function, locate the source of the fault injecte...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More