Vulnerability detection method and device for web application program and computer readable storage medium
An application and vulnerability detection technology, applied in the computer field, can solve the problems of low comprehensiveness and low accuracy of vulnerability detection, and achieve the effect of improving the comprehensiveness and accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
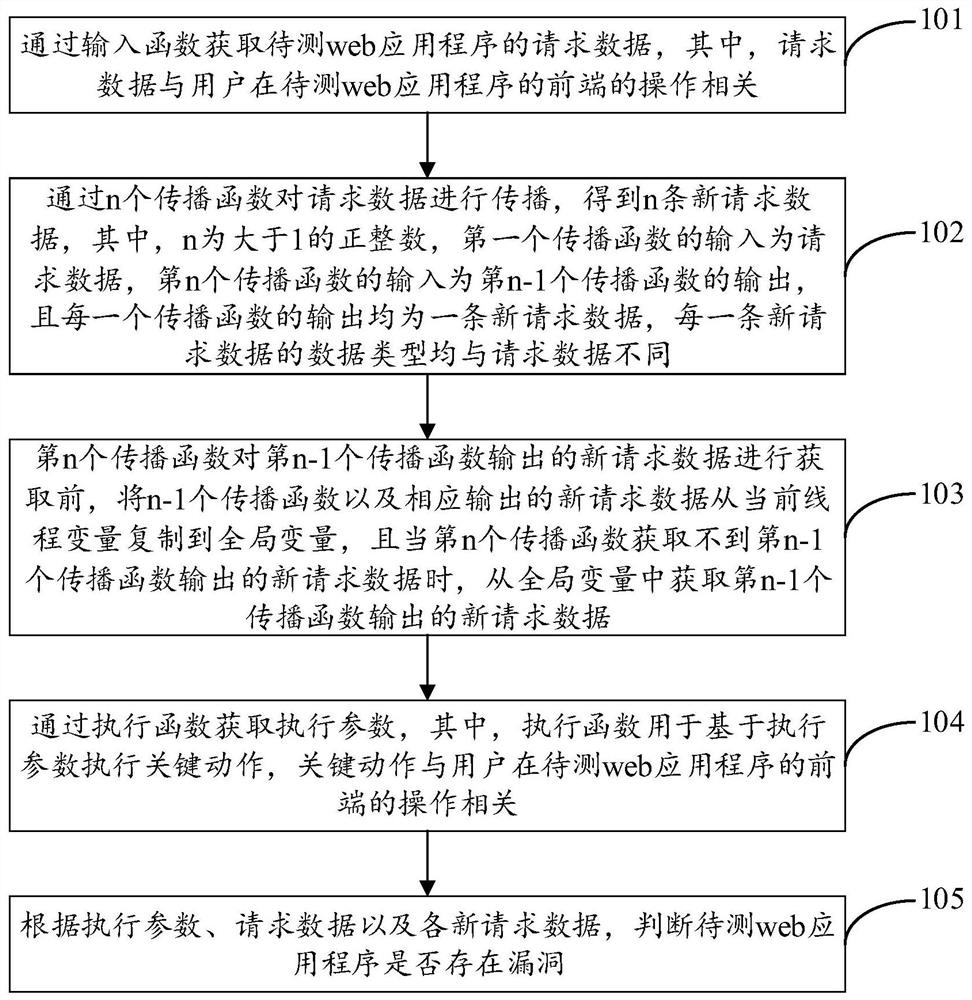
Method used
Image
Examples
Embodiment Construction
[0019] In order to make the objects, technical solutions, and advantages of the present invention, the present invention will be described in conjunction with the embodiments of the present invention and the corresponding drawings, wherein the same or similar reference numerals are identical to the same. Or similar components or components having the same or similar functions. It should be understood that various embodiments of the invention described below are intended to be utilized to illustrate the invention, that is, the present invention, that is, according to various embodiments of the present invention, one of ordinary skill in the art is not creative. All other embodiments obtained under labor will belong to the scope of the invention. Further, the technical features according to each embodiment of the present invention described below may be combined with each other as long as there is no conflict between each other.
[0020] In the related art, since the stain data and ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More