User authentication method and device, electronic equipment and computer readable storage medium
A technology for user authentication and authentication equipment, applied in the field of system security, can solve the problem of low security in the user authentication process, and achieve the effect of improving security and ensuring secure transmission
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] Exemplary embodiments of the present invention will be described in more detail below with reference to the accompanying drawings. Although exemplary embodiments of the present invention are shown in the drawings, it should be understood that the invention may be embodied in various forms and should not be limited to the embodiments set forth herein.
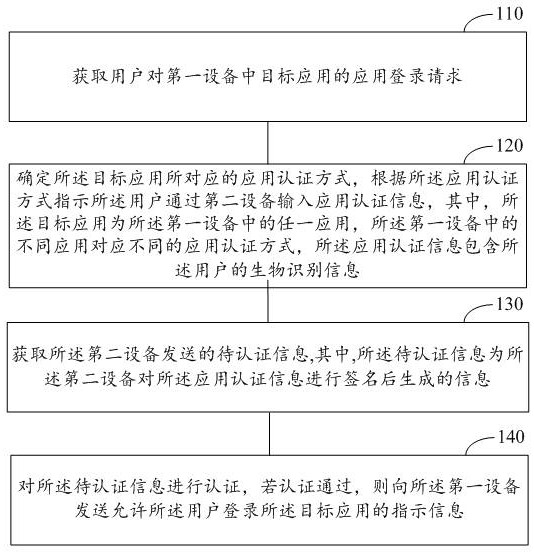
[0044] figure 1 A flow chart of a user authentication method according to an embodiment of the present invention is shown, and the method can be applied to a security authentication server. The memory of the security authentication server is used to store at least one executable instruction, and the executable instruction causes the processor of the security authentication server to execute the operation of the above user authentication method.
[0045] like figure 1 As shown, the method includes the following steps:
[0046] Step 110: Obtain the user's application login request for the target application in the first ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More