Method and system for secure sharing of data between first region and second region
An inter-regional and regional technology, applied in the computer field, can solve problems such as lack of control over data usage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
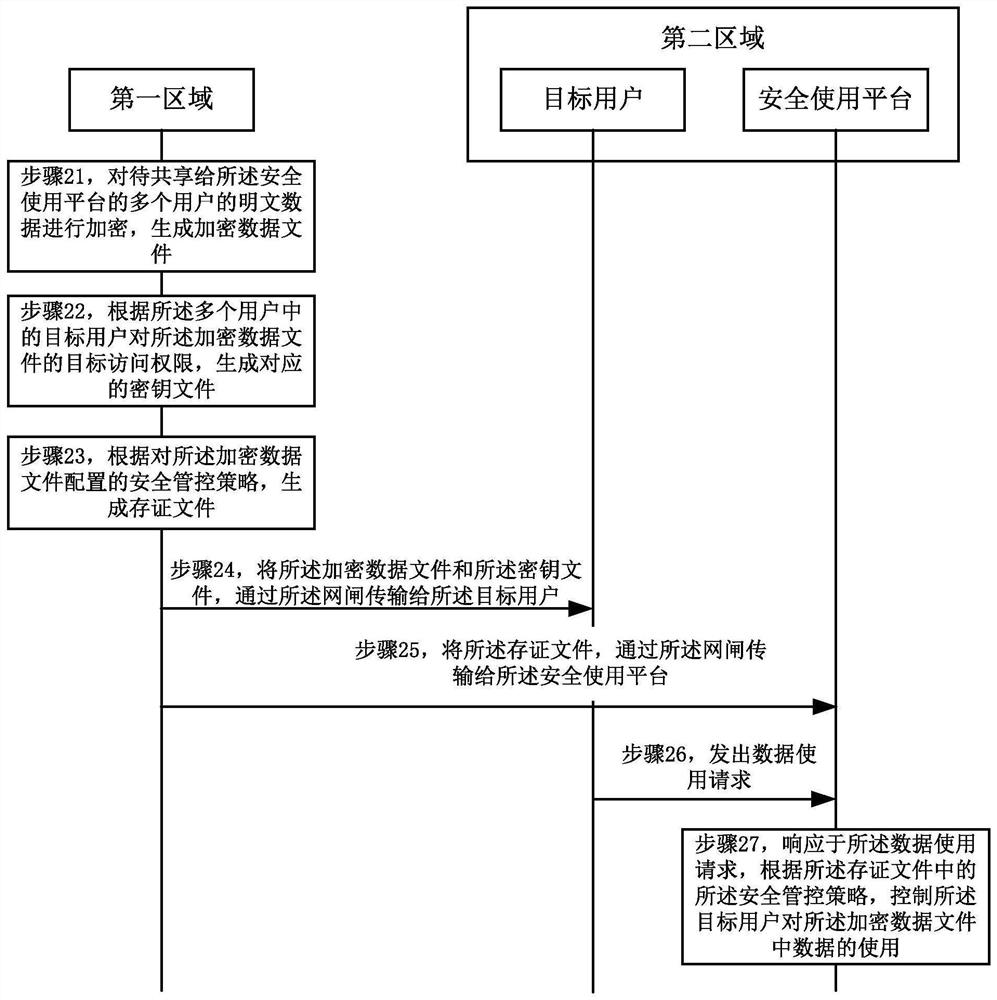
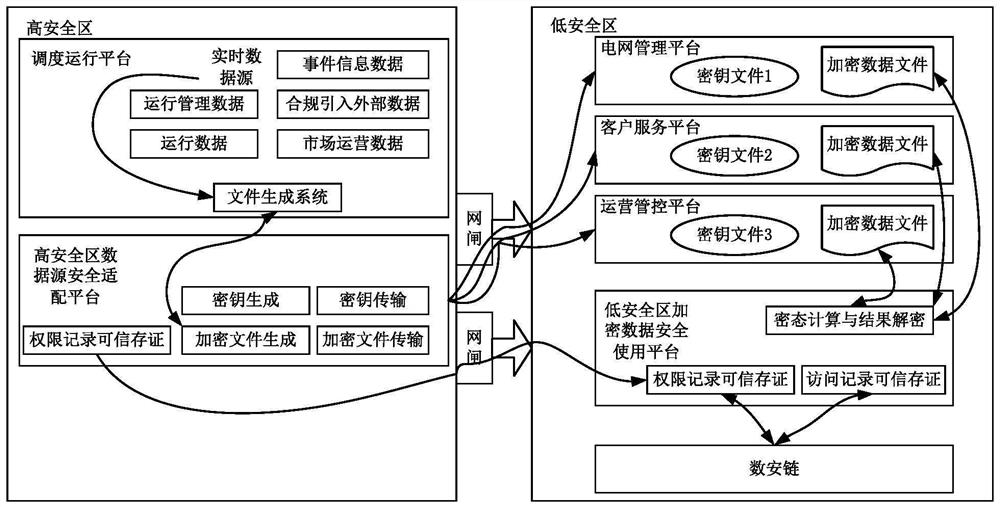
[0082] The solutions provided in this specification will be described below in conjunction with the accompanying drawings.
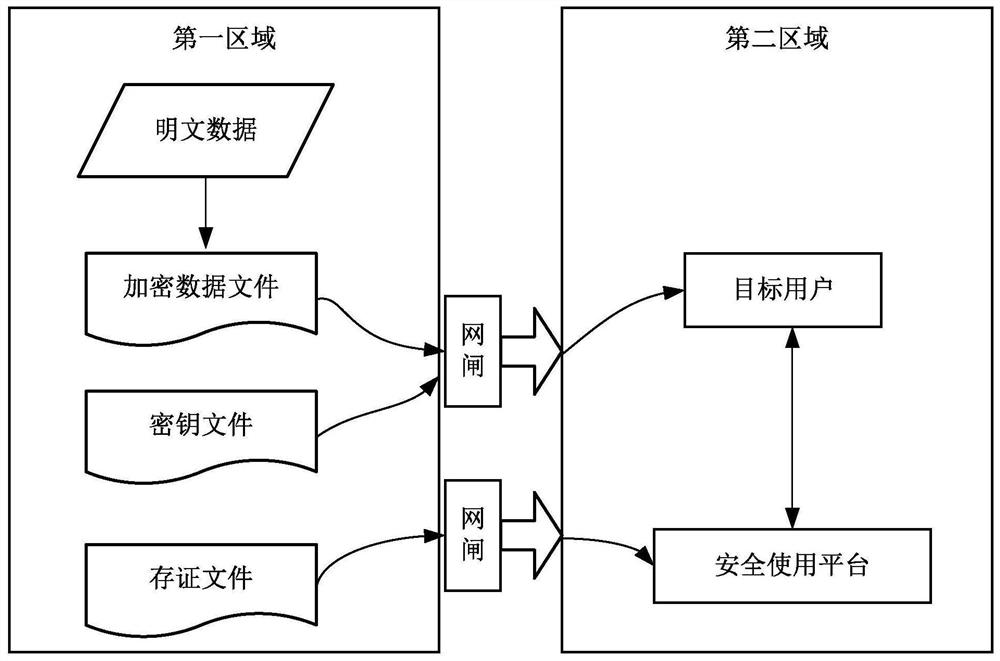
[0083] figure 1 It is a schematic diagram of an implementation scenario of an embodiment disclosed in this specification. This implementation scenario involves data security sharing between the first area and the second area, that is to say, both data sharing and data security need to be considered. refer to figure 1 , physical isolation is adopted between the first area and the second area, and a gatekeeper is set; the second area is set with a safe use platform. Among them, the gatekeeper is an information security device that uses a solid-state switch with multiple control functions to read and write media and connects two independent host systems. Since the two independent host systems are isolated by the gatekeeper, there is no physical connection, logical connection and information transmission protocol for communication between the systems, and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More