Attack detection method and device, electronic equipment and storage medium
An attack detection and storage device technology, applied in the field of network security, can solve the problems of wide attack range and low attack threshold in the terminal configuration structure function solution, and achieve the effect of reducing system resource overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
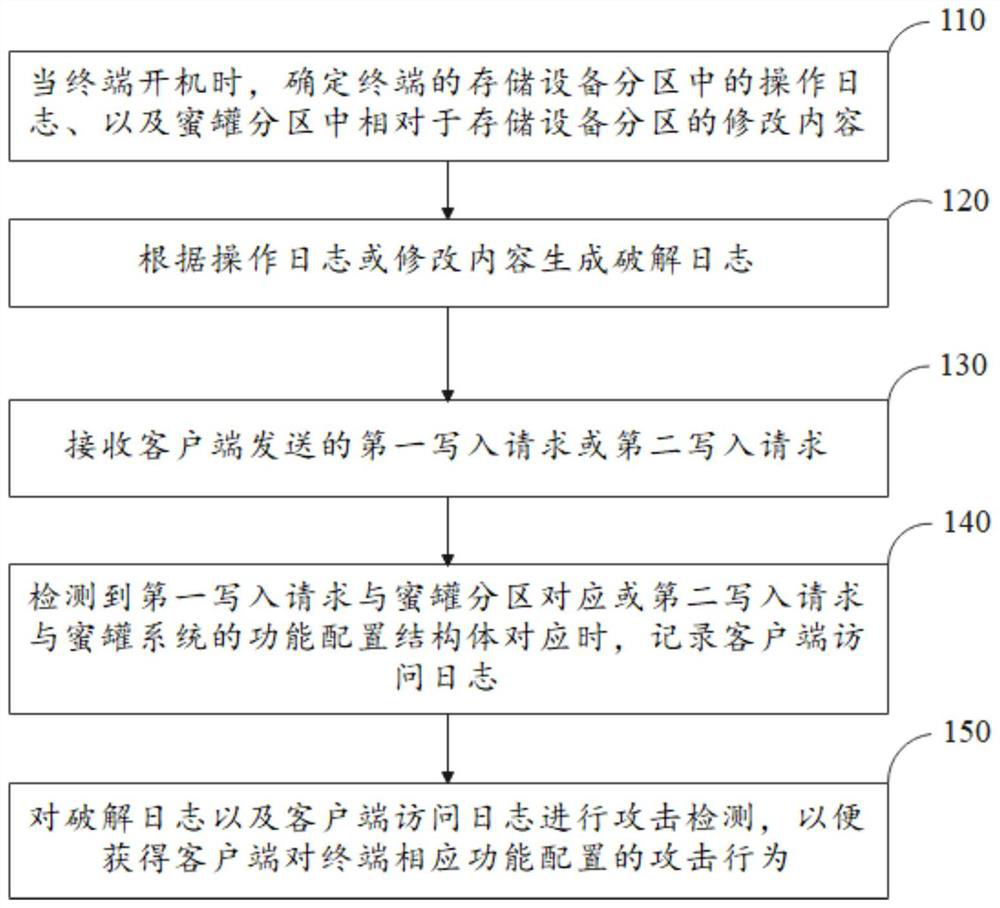
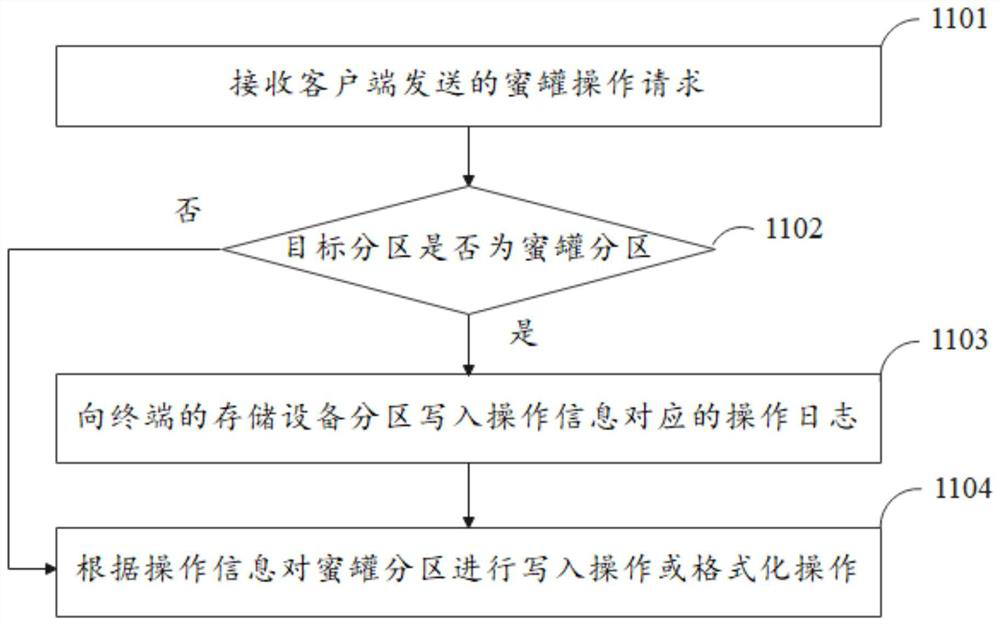
[0066] The following will clearly and completely describe the technical solutions in the embodiments of the application with reference to the drawings in the embodiments of the application. Apparently, the described embodiments are only some of the embodiments of the application, not all of them. Based on the embodiments in this application, all other embodiments obtained by those skilled in the art without making creative efforts belong to the scope of protection of this application.
[0067] Embodiments of the present application provide an attack detection method, device, electronic equipment, and storage medium.
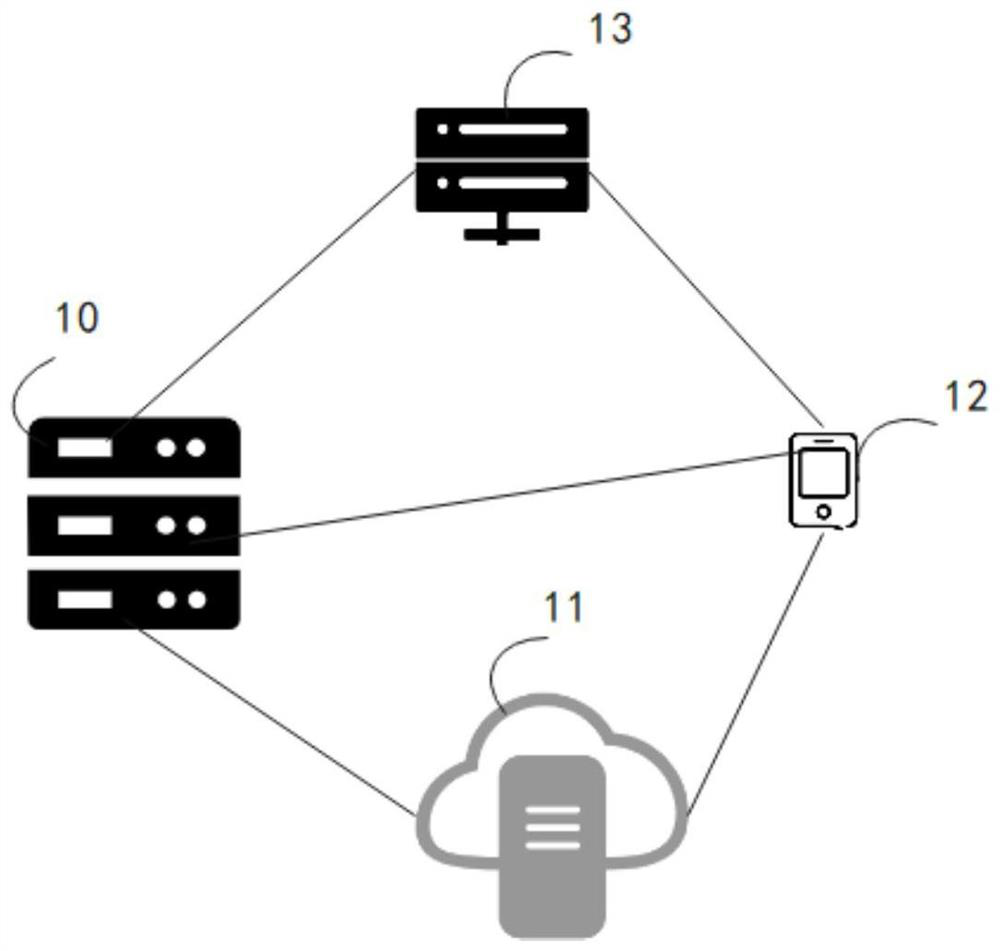
[0068] Wherein, the attack detection device may specifically be integrated in an electronic device, and the electronic device may be a terminal, a server, or other equipment. Wherein, the terminal can be a mobile phone, a tablet computer, a smart bluetooth device, a notebook computer, or a personal computer (Personal Computer, PC) and other devices; the server ca...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More