Safety protection capability detection system, method, device, equipment and medium
A security protection capability and security protection technology, applied in the field of network security, can solve problems such as the inability to test the effect of security protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
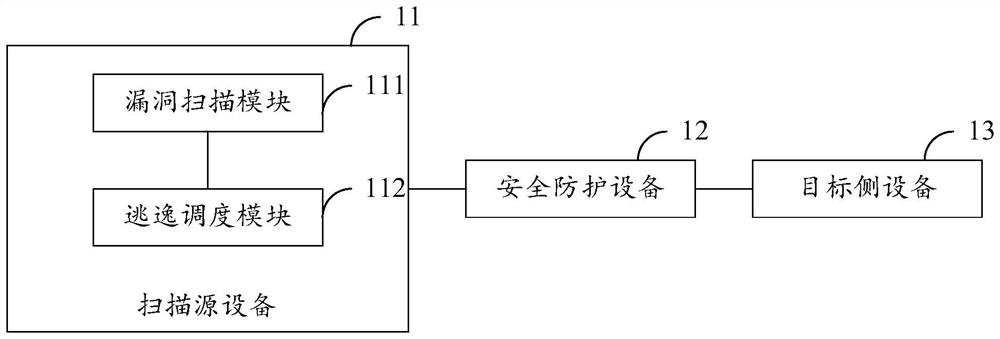
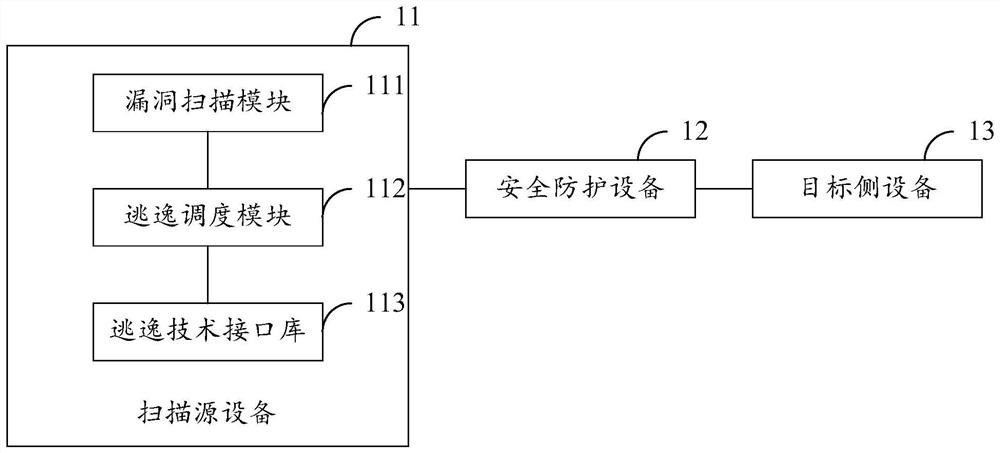
[0066] figure 1 A schematic structural diagram of a security protection capability detection system provided by an embodiment of the present invention, the system includes: a scanning source device 11, a security protection device 12, and a target side device 13; the scanning source device 11 includes a vulnerability scanning module 111 and an escape scheduling module 112;
[0067] The vulnerability scanning module 111 is configured to send a vulnerability scanning task to the escape scheduling module 112, wherein the vulnerability scanning task carries vulnerability identification information to be scanned;
[0068] The evasion scheduling module 112 is configured to obtain an evasion technique interface corresponding to the vulnerability to be scanned according to the vulnerability identification information to be scanned, and send the evasion technique interface to the vulnerability scanning module 111;
[0069] The vulnerability scanning module 111 is configured to use the...
Embodiment 2
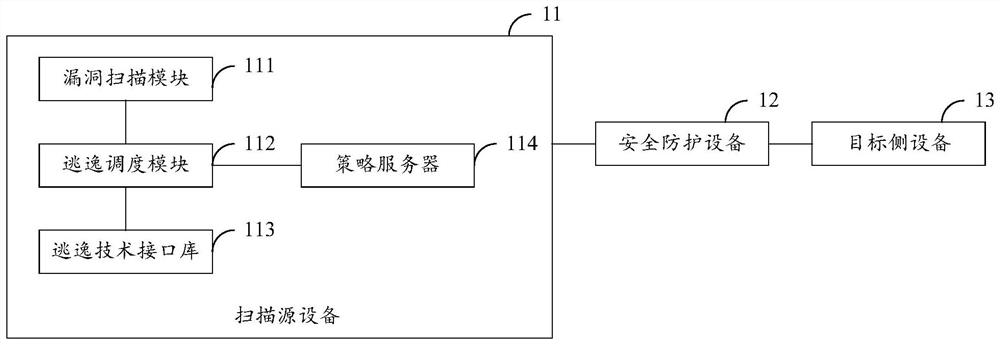
[0077] When detecting the security protection capability of the security protection device, if the vulnerability to be scanned supports self-negotiation of the evasion technique, the solution of the foregoing embodiment may be used to detect the security protection capability of the security protection device. However, for vulnerabilities that do not support self-negotiation of evasion techniques, evasion strategy negotiation is required. After the negotiation is completed, the security protection capability of the security protection device can be tested. Therefore, for vulnerabilities that do not support self-negotiation of evasion techniques, in order to detect the security protection capabilities of security protection equipment, on the basis of the above-mentioned embodiments, in the embodiments of the present invention, as follows image 3 As shown, the scan source device also includes a policy server 114;
[0078] The escape scheduling module 112 is further configured t...
Embodiment 3
[0087] In order to measure the protective effect of the safety protection equipment more directly, on the basis of the above-mentioned embodiments, in the embodiment of the present invention, such as Figure 5 As shown, the target side device 13 includes an asset target library 133;
[0088]The vulnerability scanning module 111 is further configured to send a vulnerability scanning task to the escape scheduling module 112, wherein the vulnerability scanning task carries the identification information of the vulnerability to be scanned in the asset target library 133;
[0089] The evasion scheduling module 112 is configured to obtain an evasion technique interface corresponding to the vulnerability to be scanned according to the vulnerability identification information to be scanned, and send the evasion technique interface to the vulnerability scanning module 111;
[0090] The vulnerability scanning module 111 is configured to use the evasion technique interface to transmit th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com