Alarm information verification method and device, equipment and storage medium
A technology of alarm information and verification methods, applied in the computer field, can solve problems such as increasing the system false alarm rate, increasing the workload of manual review and judgment, and reducing the efficiency of system screening
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
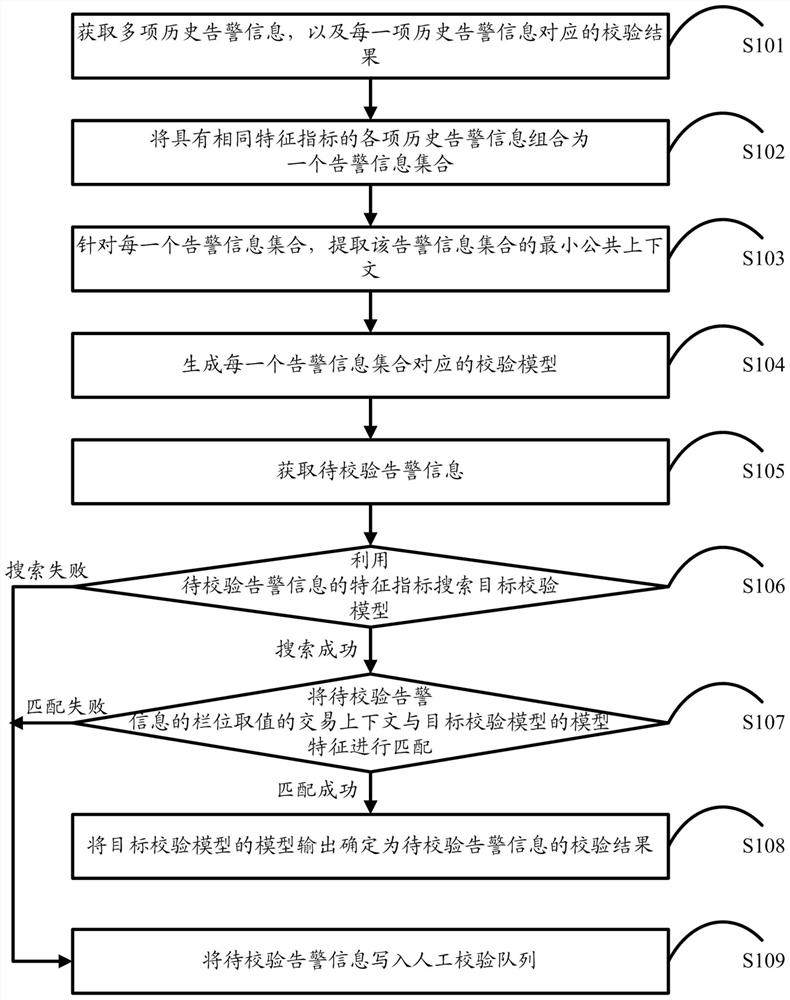
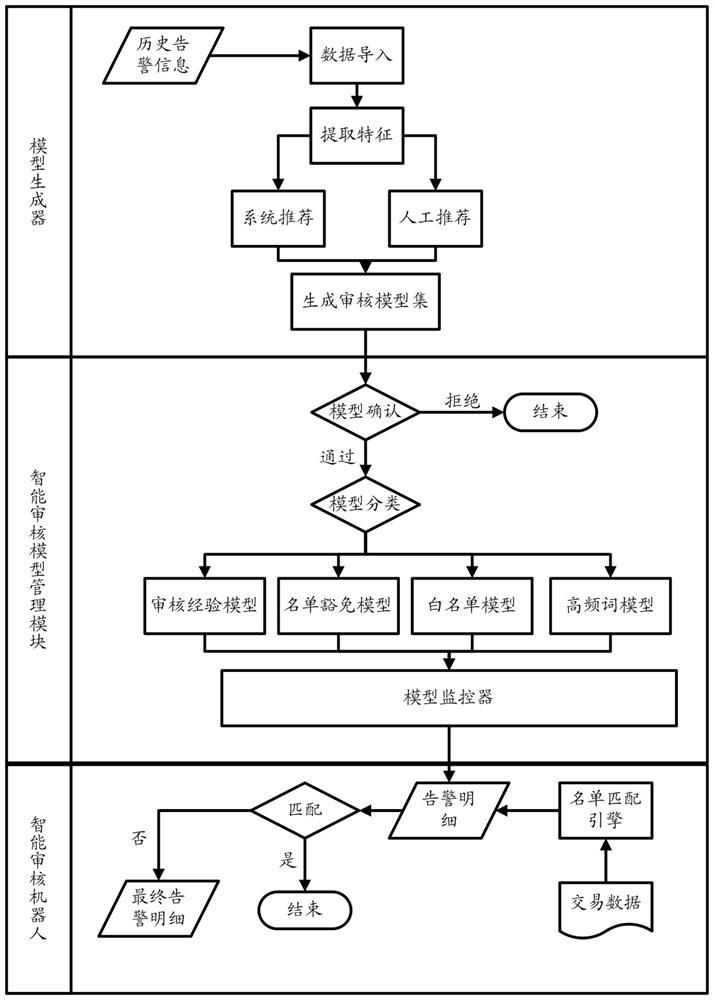
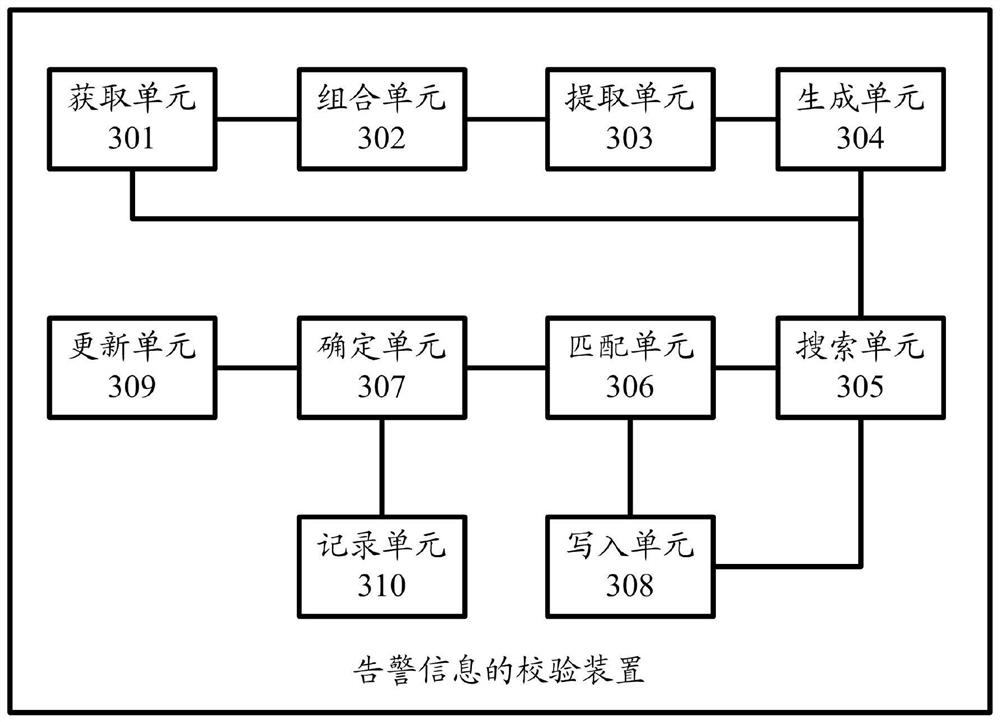
[0050] The technical solutions in the embodiments of the present invention will be clearly and completely described below with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only a part of the embodiments of the present invention, rather than all the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative efforts shall fall within the protection scope of the present invention.
[0051] Financial institutions need to carry out list monitoring on customers and transactions, so that when a transaction is detected that may involve a preset control list, it can take corresponding control measures for the transaction.
[0052] In order to prevent the risk of system leakage and effectively identify aliases and name changes in the list, the common practice in the industry is to perform fuzzy matching on customers and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More