Associated equipment and method for internal network security management
A security management and internal network technology, applied in the field of internal network security management related equipment, can solve problems such as increasing administrator burden, increasing operational complexity, and unable to prevent information leakage, to prevent network resource abuse and ensure integrity.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
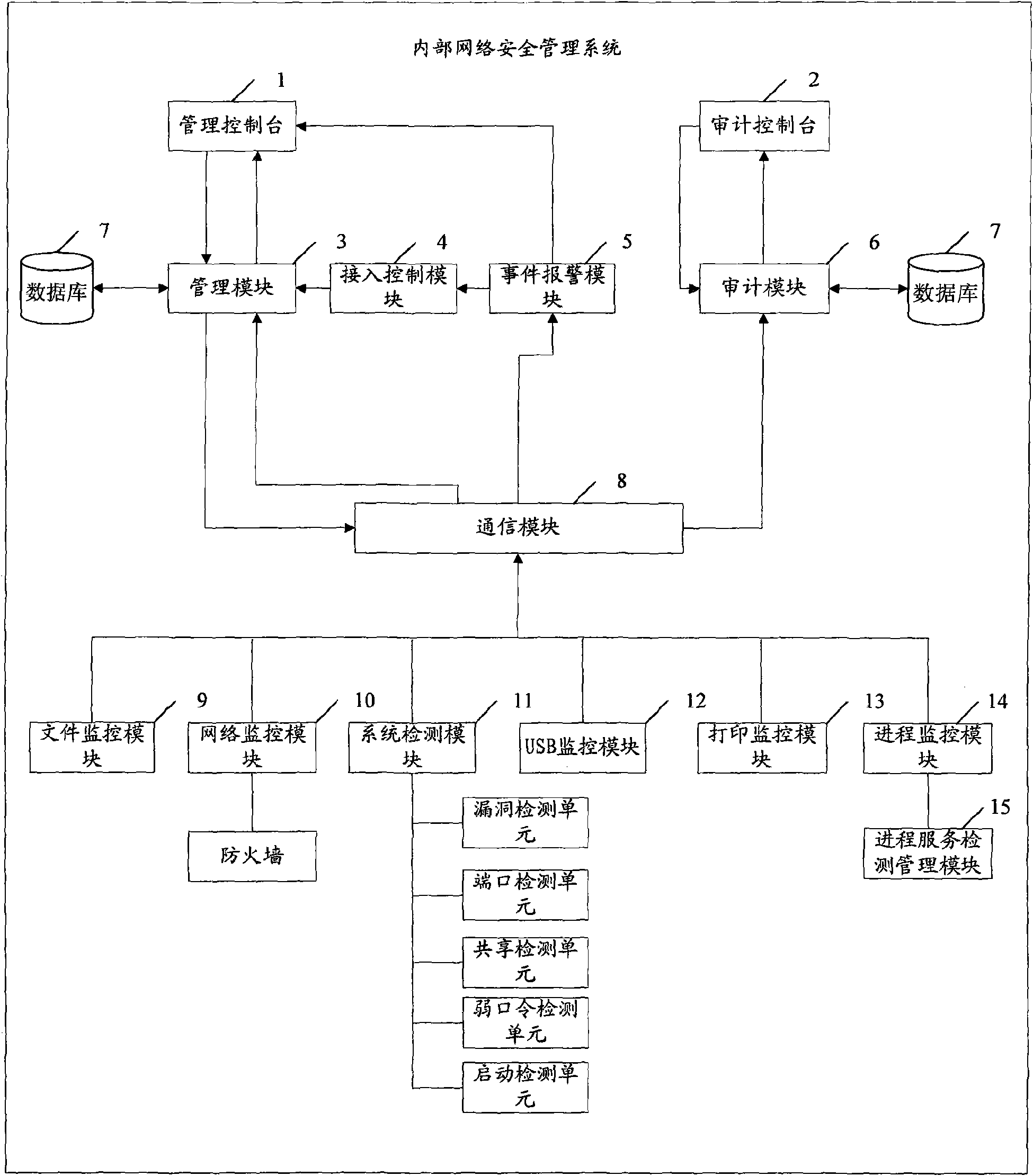
[0026] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
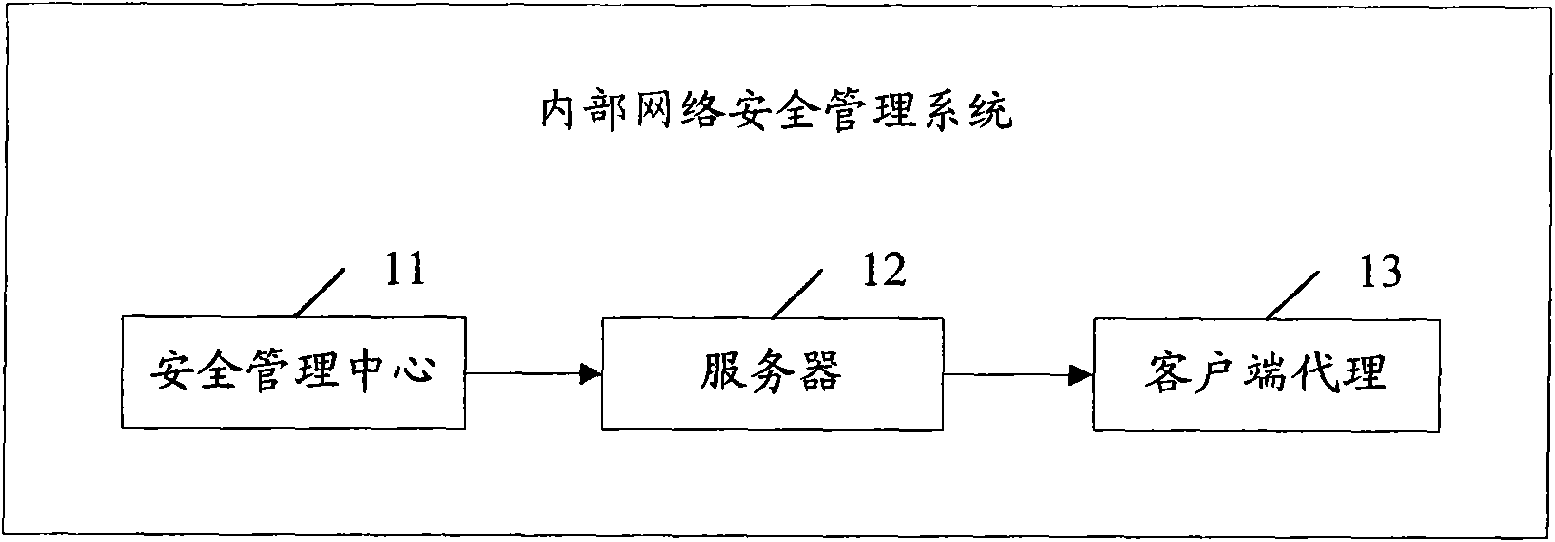
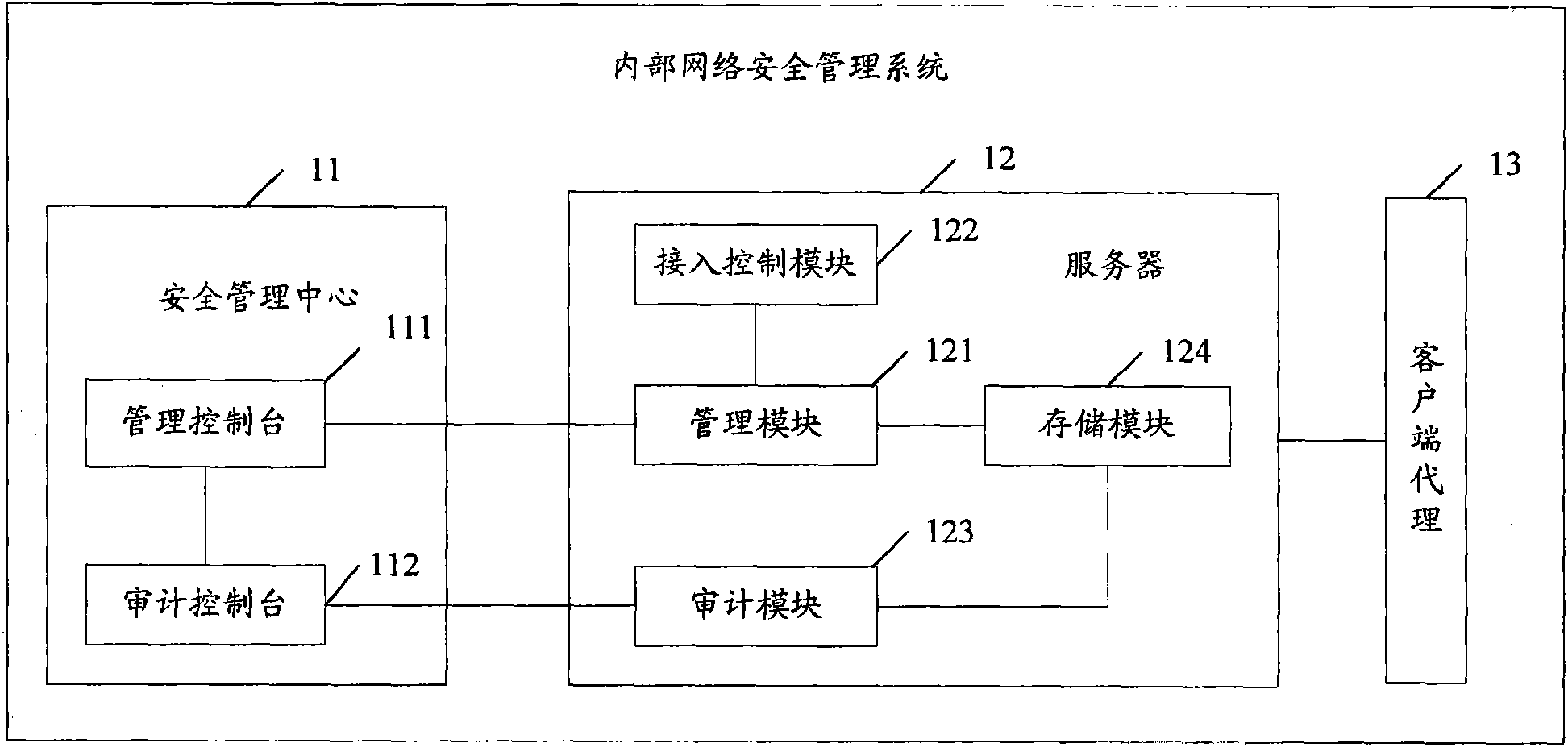
[0027] Embodiments of the present invention provide related equipment and methods for internal network security management, which are based on the assumption that internal network equipment is untrustworthy and insecure, not only protecting internal network computers from external hidden dangers, but also Active prevention of internal network computers breaks through the traditional idea that the network security model is based on the assumption that internal networ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More