Method and device for realizing internet lawful interception
A technology of legal monitoring and monitoring management, which is applied in the field of network communication information security, can solve problems such as difficult to be timely and effective, and achieve the effects of reducing security management costs, being easy to implement and deploy, and realizing centralized management
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The preferred embodiments of the present invention will be described in detail below with reference to the accompanying drawings.
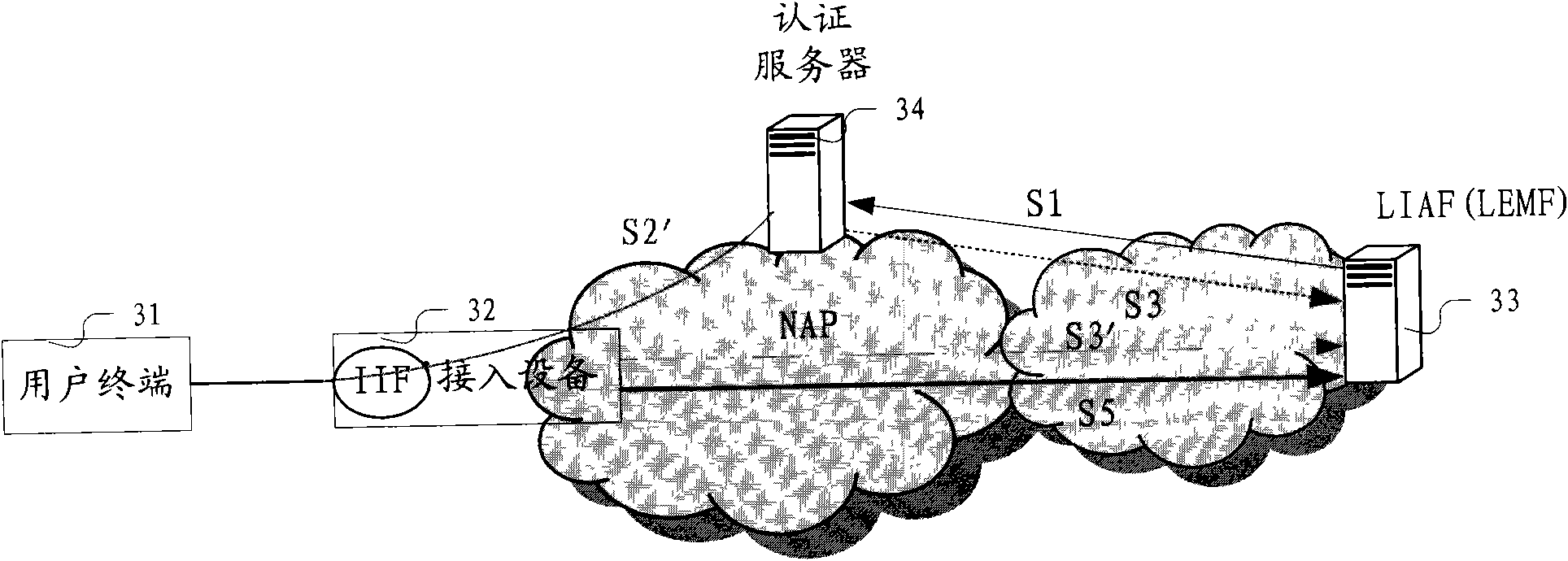
[0030] Figure 3A This is the first structural embodiment of the IP network lawful interception system provided by the present invention. It includes a user terminal 31, a network access device 32, an authentication server 34, and a legal interception facility 33 (specifically, it may include a legal interception management device LIAF and a legal enforcement monitoring device LEMF). Among them, the user terminal 31, as a related device used by the user to communicate, is controlled by the user; the network access device 32 is used to connect the user terminal and the connecting device leading to other networks, which is controlled by the network access provider. (NAP) provides, directly connected to the user terminal, according to the technology and configuration it adopts, through its internal internal interception function (IIF), data c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More