Access control method for operation system and implementation platform thereof
An operating system and access control technology, applied in program control devices, platform integrity maintenance, instruments, etc., can solve the problem that access control modules are difficult to implement in multiple systems, and achieve the effect of convenient and safe configuration
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
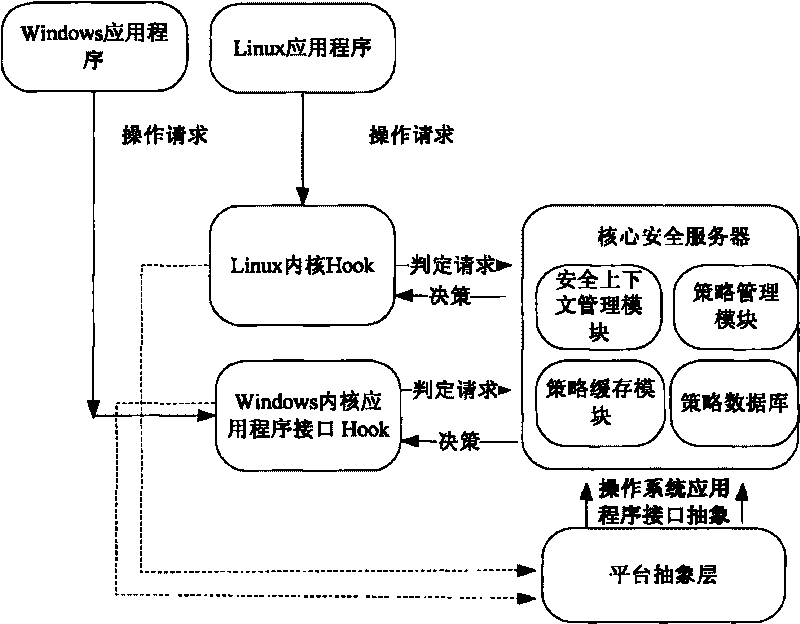
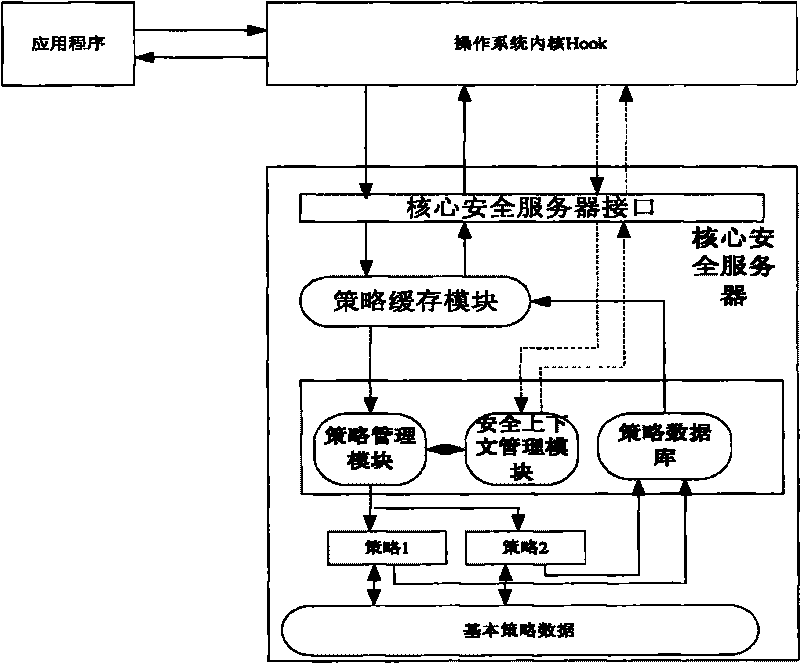
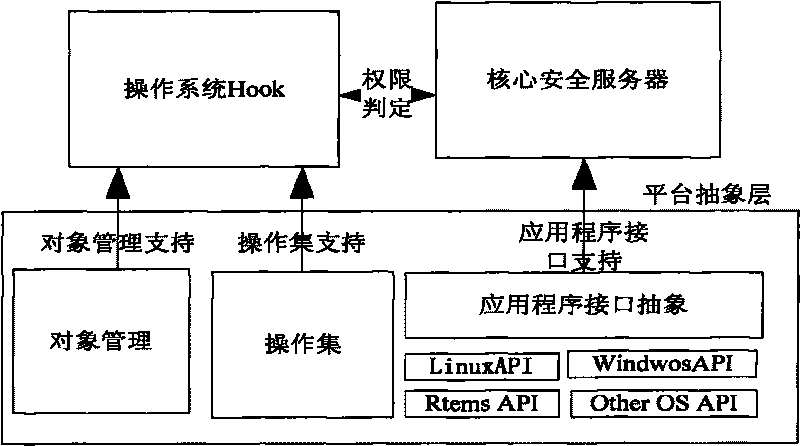
Method used
Image
Examples
Embodiment 1
[0022] In access control, the subject generally represents the initiator of the action, and the object represents the recipient of the action. For a computer, the subject generally refers to a process, while the object generally refers to resources such as processes, files or Sockets.
[0023] For "security label" or "security context", the concept is the label of the security model, which is the basis for the security model to judge the authority. In the present invention, "security context" (context) is used for description. Each security model has its own security context. For the subject and object in the operating system, its security context is the collection of security contexts of each security model loaded in the system. For example, in a system implementing the BLP and BIBA model, the BLP level of process A is 1, and the BIBA level is 5, then the security context of process A is the set {1, 5} of BLP and BIBA security contexts.
[0024] For a security model, the ba...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More