Method, device and system for key agreement
A key agreement and equipment technology, applied in transmission systems, security devices, electrical components, etc., can solve problems such as complex encrypted communication processes
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] The embodiment of the present invention provides a key agreement method and a key agreement device for realizing the method. In order to better understand the technical solutions of the present invention, the embodiments provided by the present invention will be described in detail below in conjunction with the accompanying drawings.
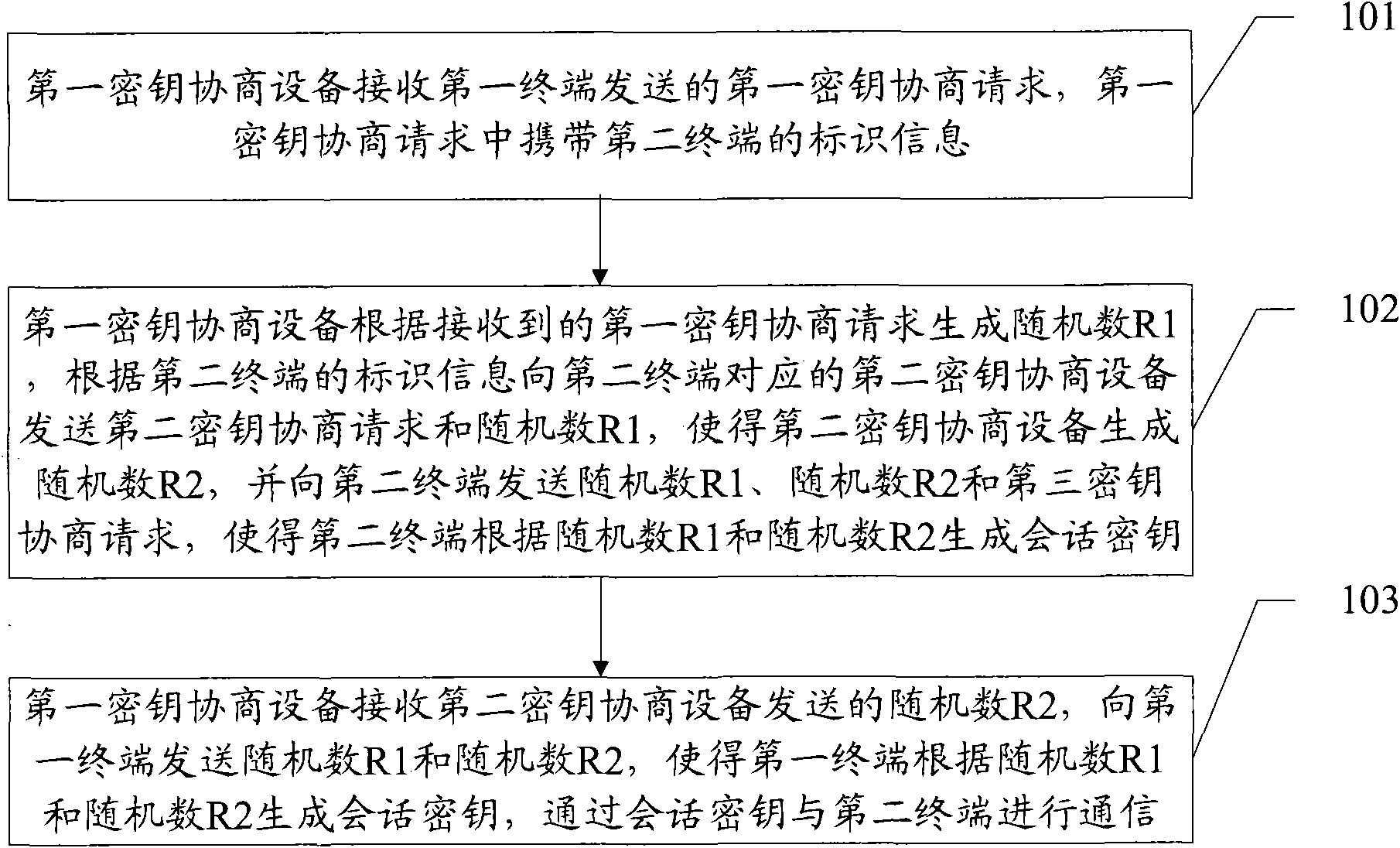
[0023] see figure 1 , figure 1 It is a flow chart of the first embodiment of the key agreement method provided by the present invention.
[0024] Step 101, the first key agreement device receives a first key agreement request sent by a first terminal, where the first key agreement request carries identification information of a second terminal.
[0025] Step 102, the first key agreement device generates a random number R1 according to the received first key agreement request, and sends a second key agreement request to the second key agreement device corresponding to the second terminal according to the identification information of the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More