Cross-domain name single sign on and off method and system as well as corresponding equipment
A single-sign-on and single-point technology, applied in the field of network applications, can solve problems such as low efficiency, redundancy, and unsafe transmission of user information back and forth, and achieve the effect of improving login efficiency and efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
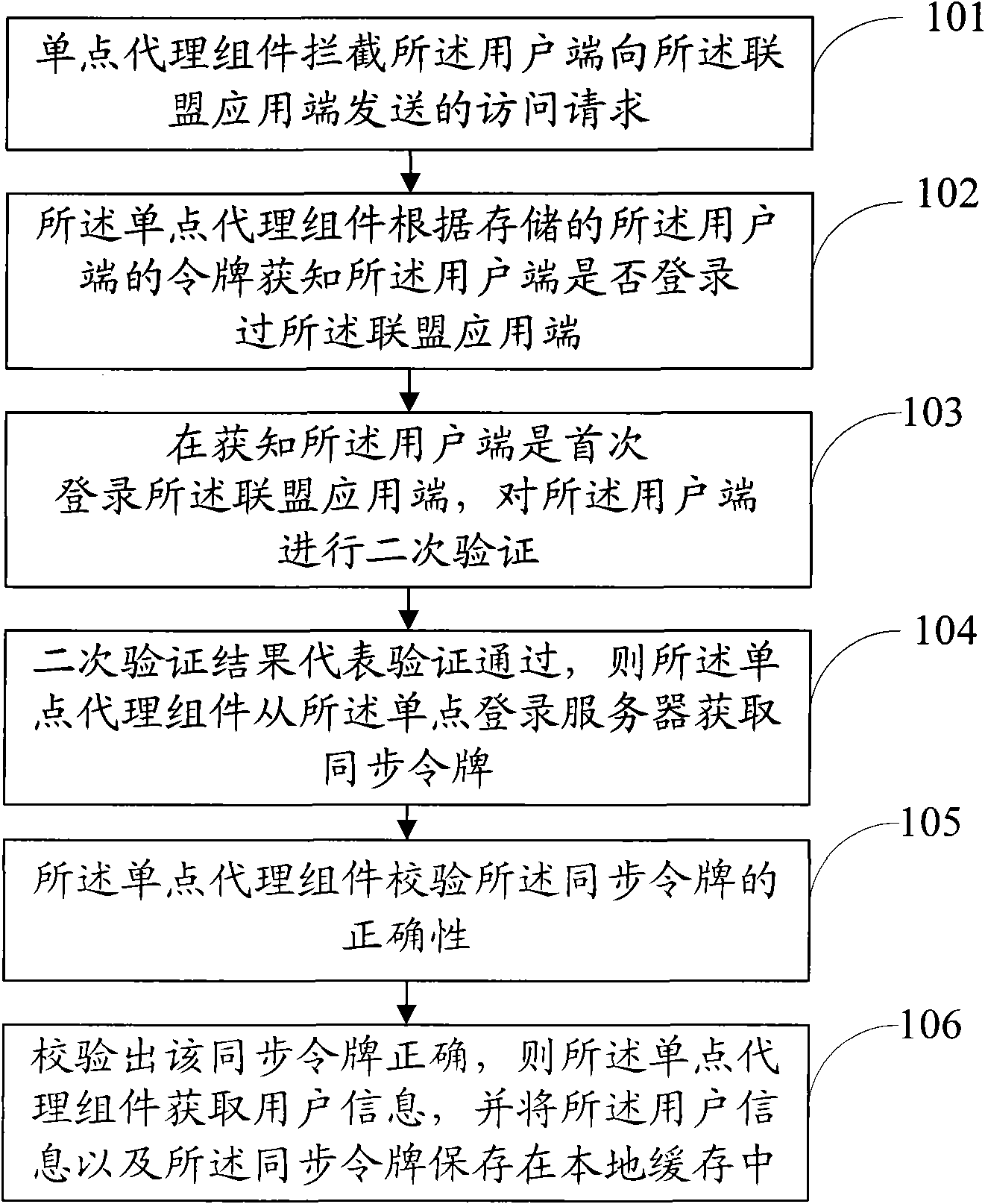
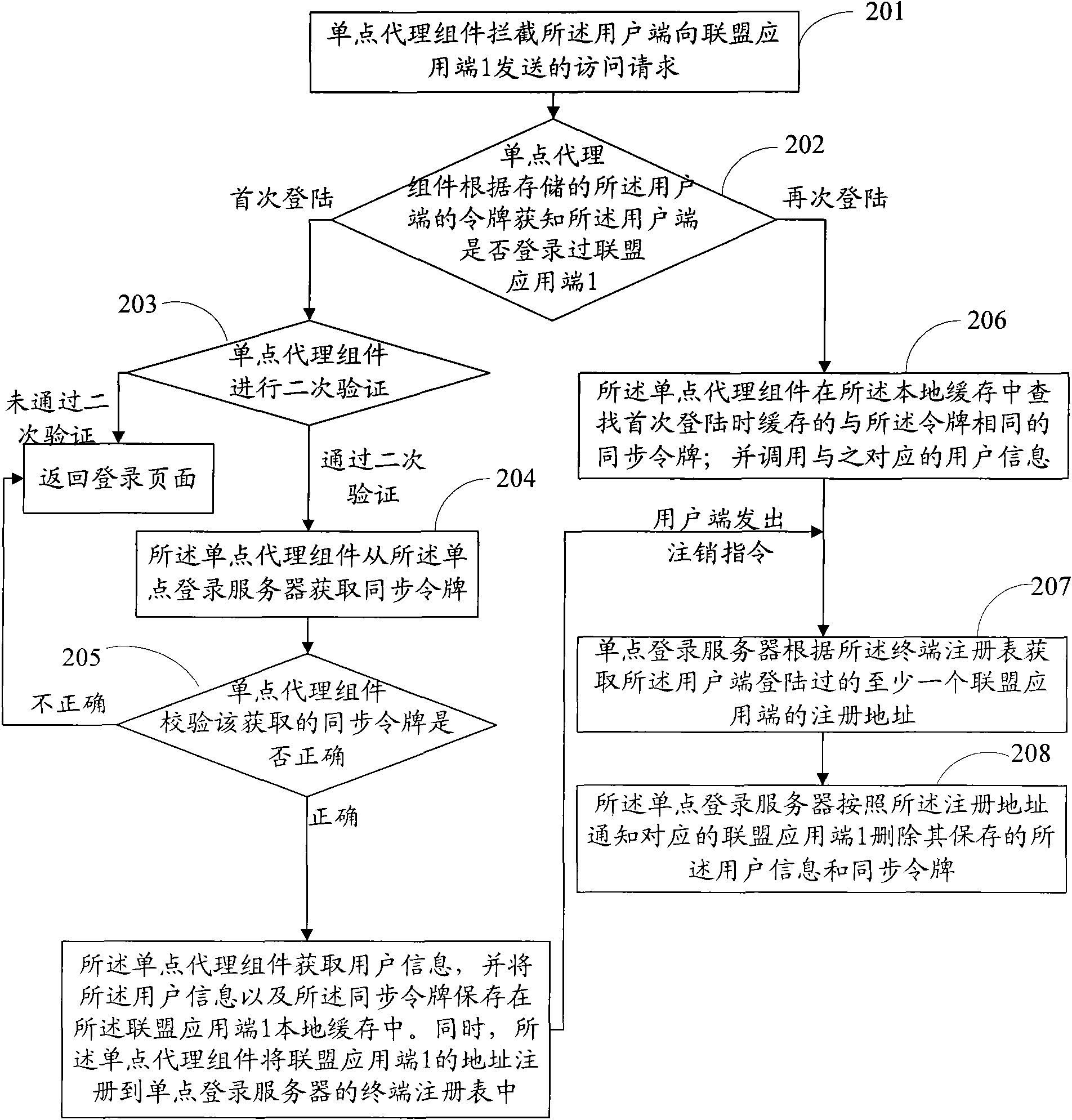
[0048] This embodiment specifically provides a cross-domain name single sign-on and logout method, such as figure 2 As shown, the method includes:
[0049] In step 201, the client normally logs in through the SSO server. After successful login, the SSO server stores the token distributed to the client in the cookie of the browser. The client sends an access request to the federated application 1 that wants to access. The single-point proxy component running on the alliance application end 1 intercepts the access request sent by the client end to the alliance application end 1 .
[0050] In step 202, the single point proxy component can know whether the client has logged in the federated application 1 according to the token stored in the cookie. When it is known that the user end has logged in the alliance application end 1 for the first time, step 203 is performed; when it is known that the user end is logged in again after the first login, that is, when the user end has lo...
Embodiment 2
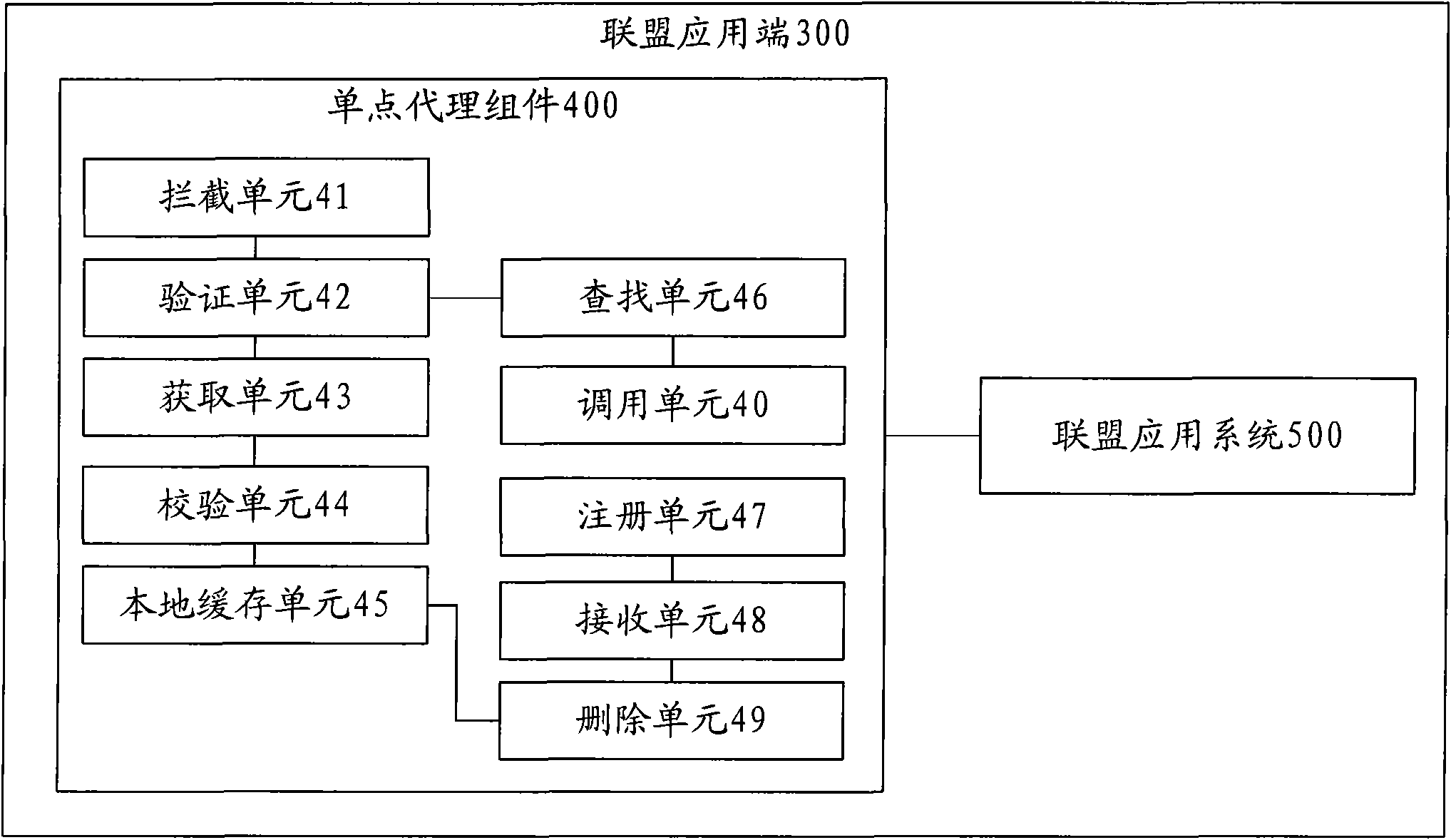
[0070] This embodiment provides an alliance application terminal 300, which can be used as the alliance application terminal 1 in Embodiment 1. The alliance application terminal 300, such as image 3 As shown, it includes: a single point agent component 400 and an alliance application system 500, wherein,
[0071] The single point proxy component 400 includes: an interception unit 41 , a verification unit 42 , an acquisition unit 43 , a verification unit 44 , and a local cache unit 45 .
[0072] The interception unit 41 is used to intercept the access request sent by the client to the alliance application system; the verification unit 42 is used to intercept the access request after the interception unit 41, when the client logs in to the alliance application for the first time, Carry out secondary verification to described user terminal; Obtaining unit 43, if the secondary verification result of verification unit 42 represents that described user terminal has logged in descr...
Embodiment 3
[0082] This embodiment specifically provides a cross-domain name single sign-on and logout system, such as Figure 4 As shown, it includes: a client terminal 61 , a single sign-on server 62 , a single point proxy component 63 and a federated application terminal 64 including the single point proxy component 63 .
[0083] Wherein, the single-point agent component 63 is used for intercepting the access request sent by the client terminal 61 to the alliance application terminal 64, when the client terminal 61 logs in to the alliance application terminal 64 for the first time, to the User terminal 61 carries out secondary verification; If the result of secondary verification represents that described user terminal 61 has logged in described alliance application end 64, then described SPO agent component 63 obtains synchronous token from SSO server 62, and checks Whether the synchronization token is correct; if the verification result represents that the synchronization token is co...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More