IP security tunnel establishment method, device and network equipment
A security tunnel and establishment method technology, applied in the field of IP security tunnel establishment, can solve problems such as encryption failure and information leakage, and achieve the effect of multi-network security protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention more clear, the embodiments of the present invention will be further described in detail below in conjunction with the embodiments and the accompanying drawings. Here, the exemplary embodiments and descriptions of the present invention are used to explain the present invention, but not to limit the present invention.
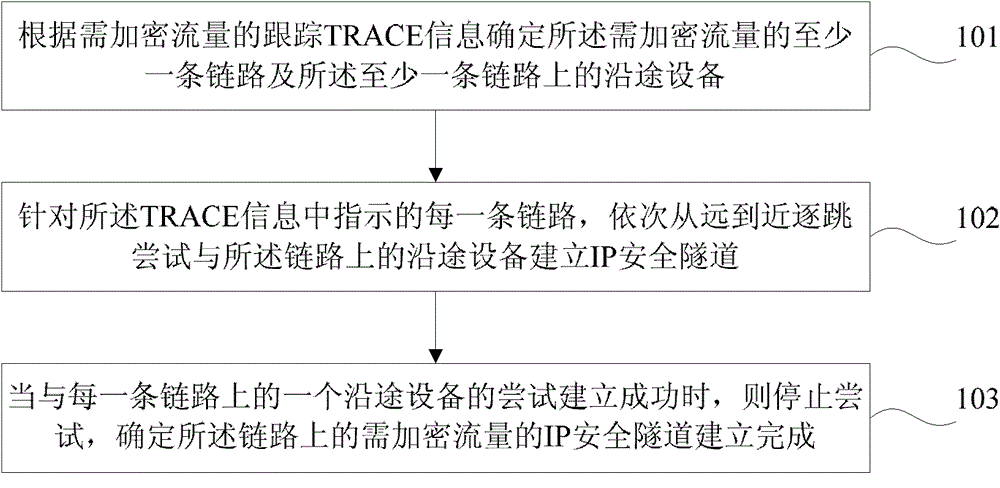
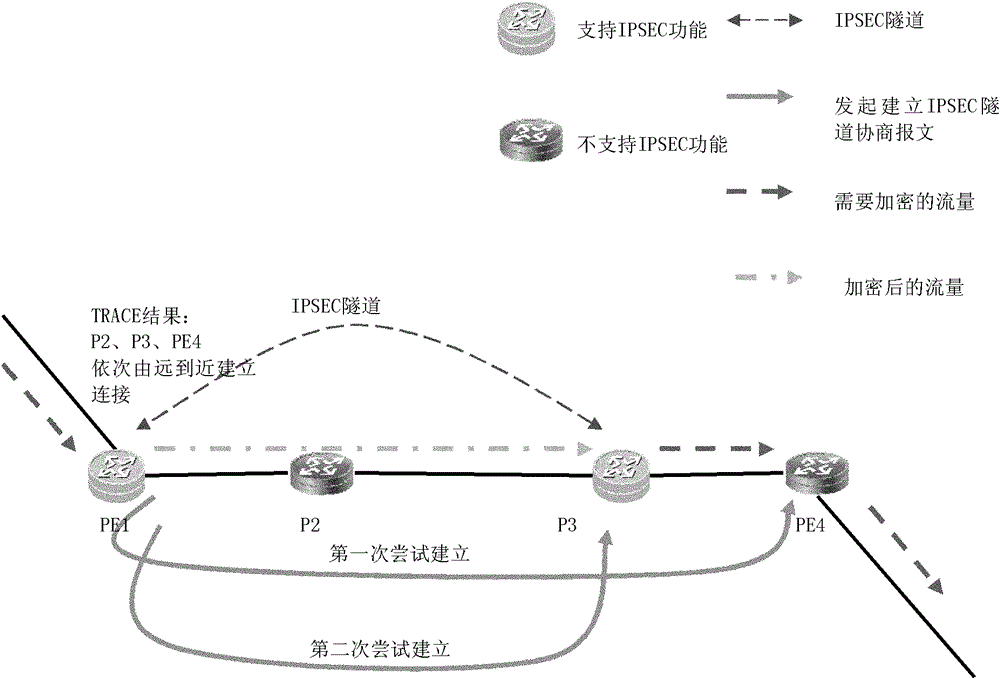
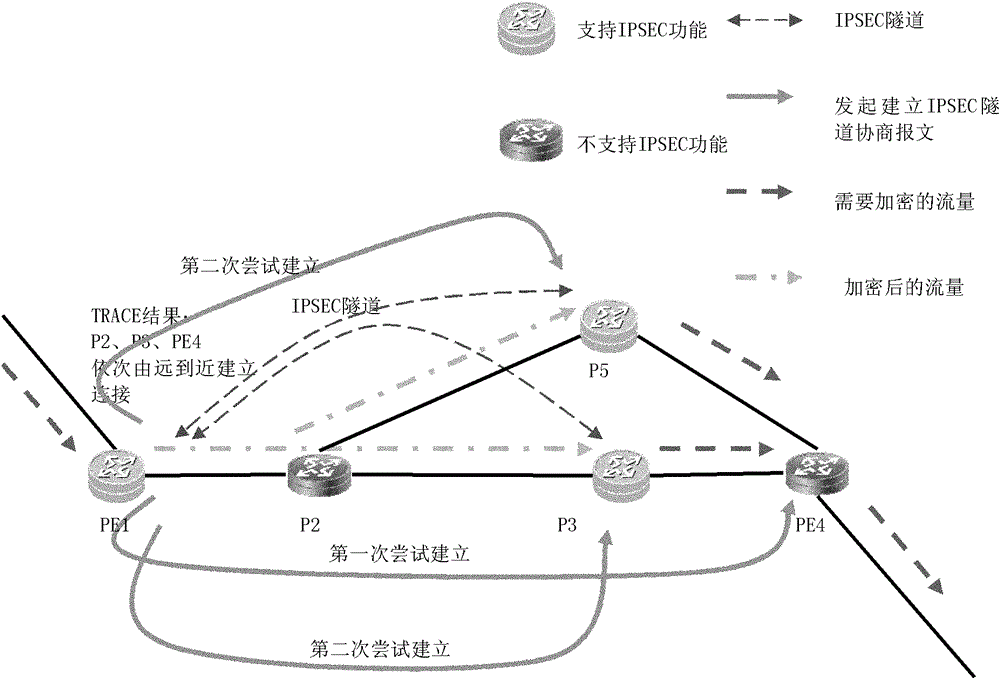
[0023] figure 1 For a flowchart of a method for establishing an IP security tunnel provided by an embodiment of the present invention, please refer to figure 1 , the method includes:
[0024] Step 101: Determine at least one link of the traffic to be encrypted and the devices on the at least one link according to the tracking TRACE information of the traffic to be encrypted;
[0025] Among them, the TRACE information is the tracking information. Since the information is transmitted from one end to the other end through many transmission media and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More