A processing method for ike negotiation exception
A processing method and abnormal technology, applied in the field of communication, can solve problems such as excessive occupation of network resources and system memory resources
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] The specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. The following examples are used to illustrate the present invention, but are not intended to limit the scope of the present invention.
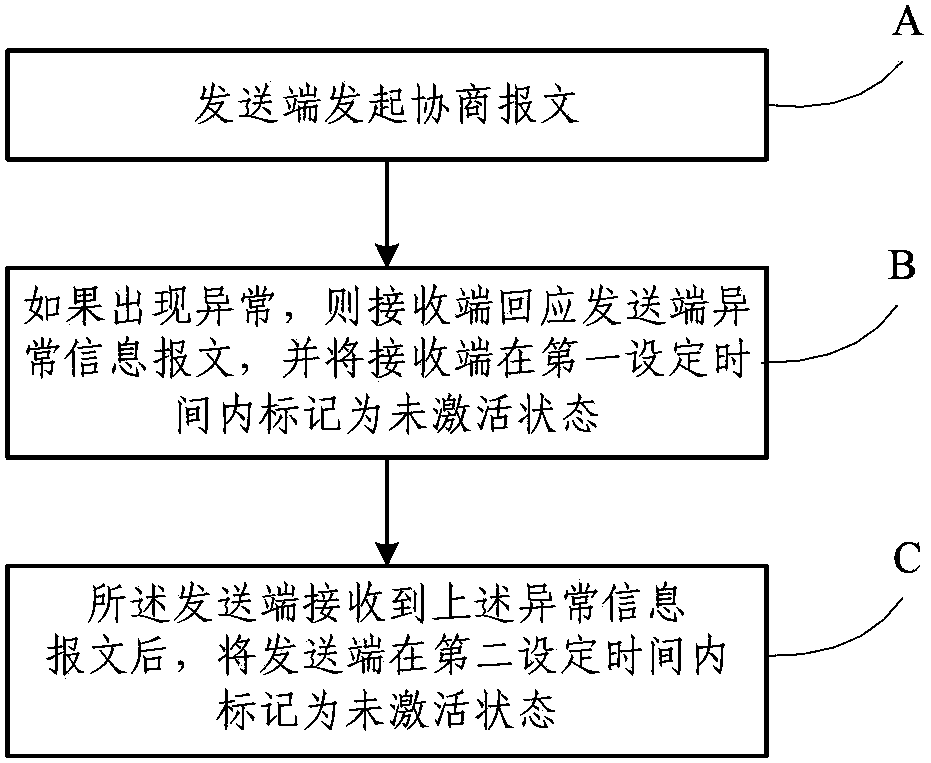
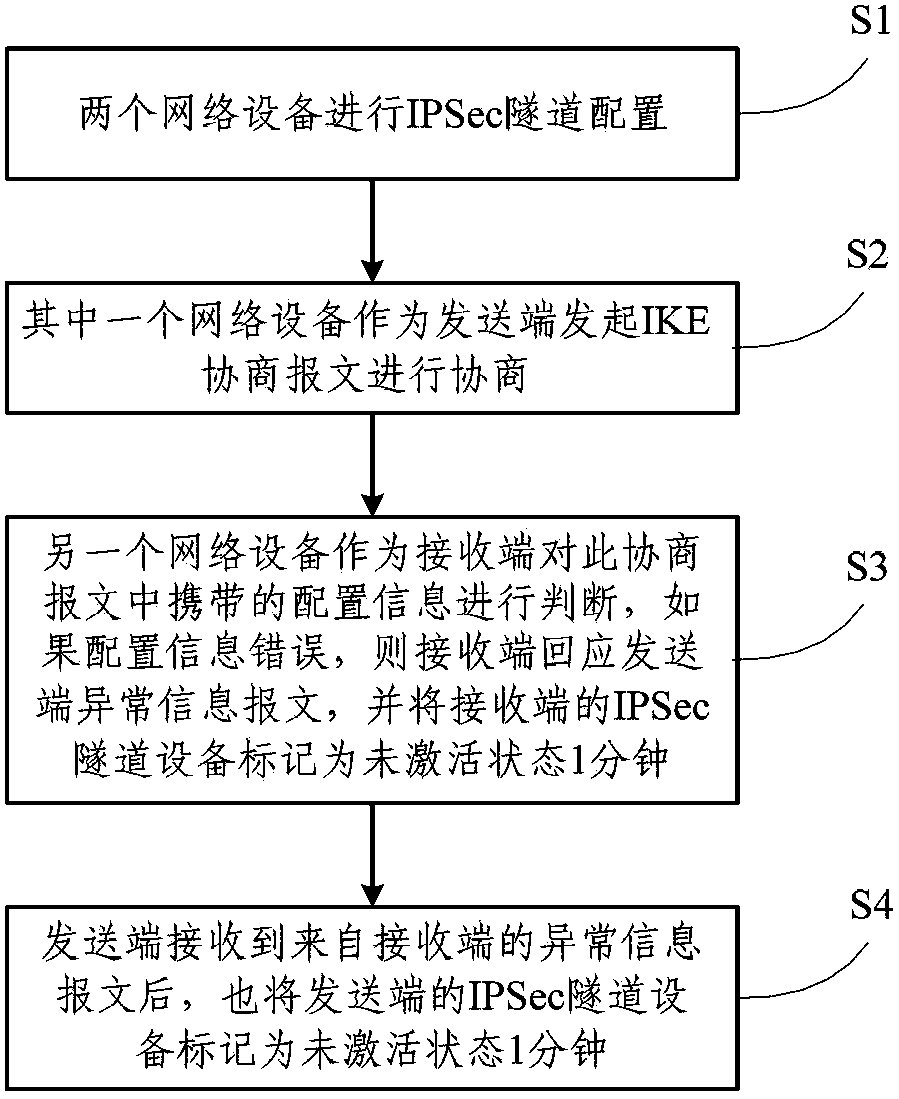
[0024] figure 1 It is a flow chart of the inventive method, comprising the following steps:
[0025] A. The sender initiates a negotiation message;
[0026] B. If there is an exception, the receiving end will respond to the sending end with an abnormal information message, and mark the receiving end as inactive within the first set time;
[0027] C. After receiving the abnormal information message, the sending end marks the sending end as inactive within a second set time.
[0028] Wherein, the negotiation message in the step A carries configuration information, and the configuration information includes an encryption key and a negotiation policy.
[0029] Further, the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More