Protection method and system of executable file
A technology for executing files and software protection devices, applied in the direction of digital data protection, etc., can solve problems such as poor analysis resistance, and achieve the effect of improving security and increasing difficulty
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] Specific embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
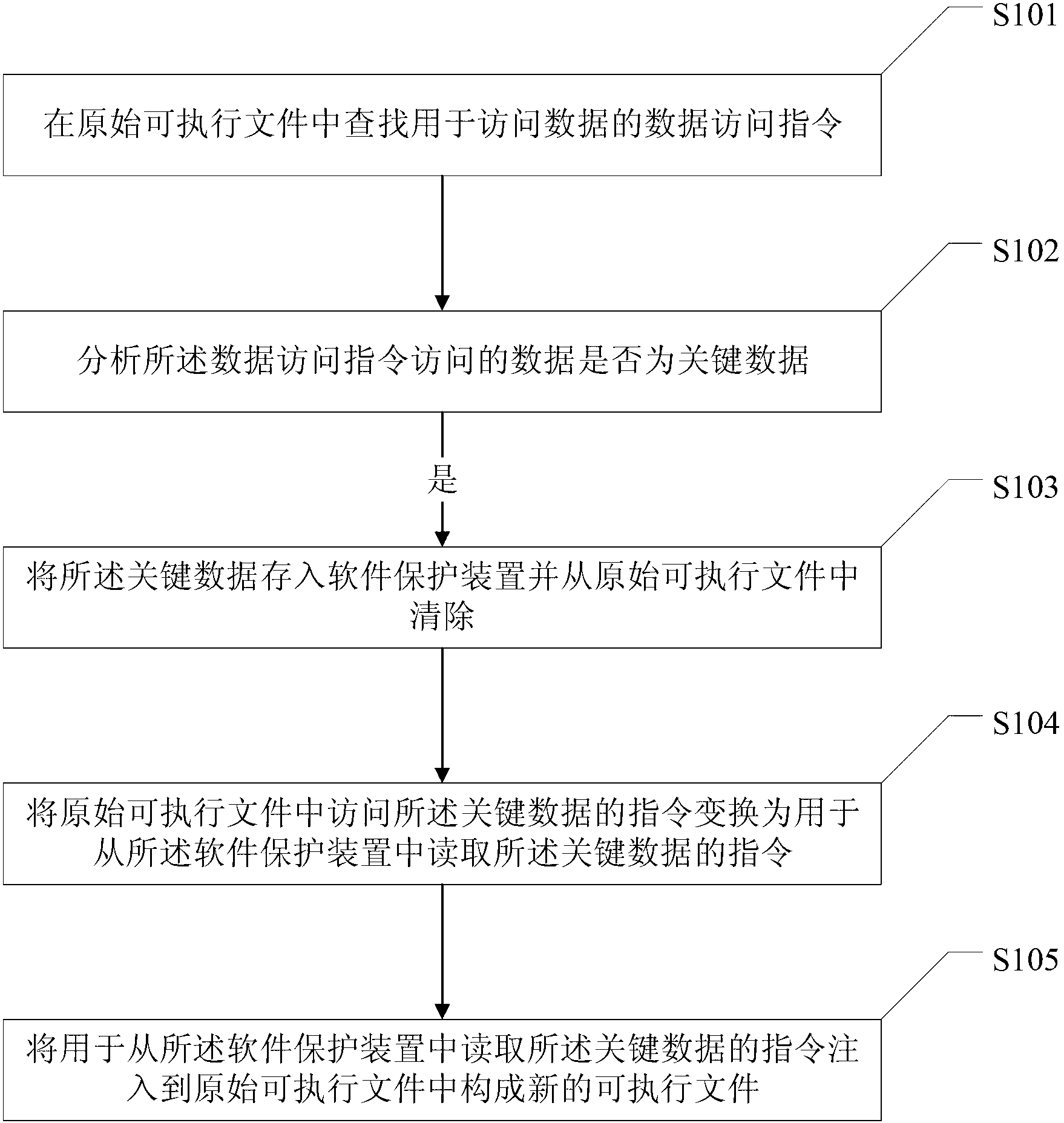
[0024] figure 1 It is a schematic flowchart of the executable file protection method of the present invention. Such as figure 1 As shown, the protection method of the executable file of the present invention comprises the following steps:
[0025] S101: Find a data access instruction for accessing data in the original executable file;
[0026] S102: Analyze whether the data accessed by the data access instruction is key data, if so, execute step S103;
[0027] S103: storing the key data in a software protection device and clearing it from the original executable file;
[0028] S104: Transform the instruction for accessing the key data in the original executable file into an instruction for reading the key data from the software protection device;
[0029] S105: Inject an instruction for reading the key data from the software protection de...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More