Safe data aggregation method
A data aggregation and security technology, applied in the field of secure data aggregation privacy protection, can solve problems such as inability to use, and achieve the effect of security advantages and resource consumption advantages
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
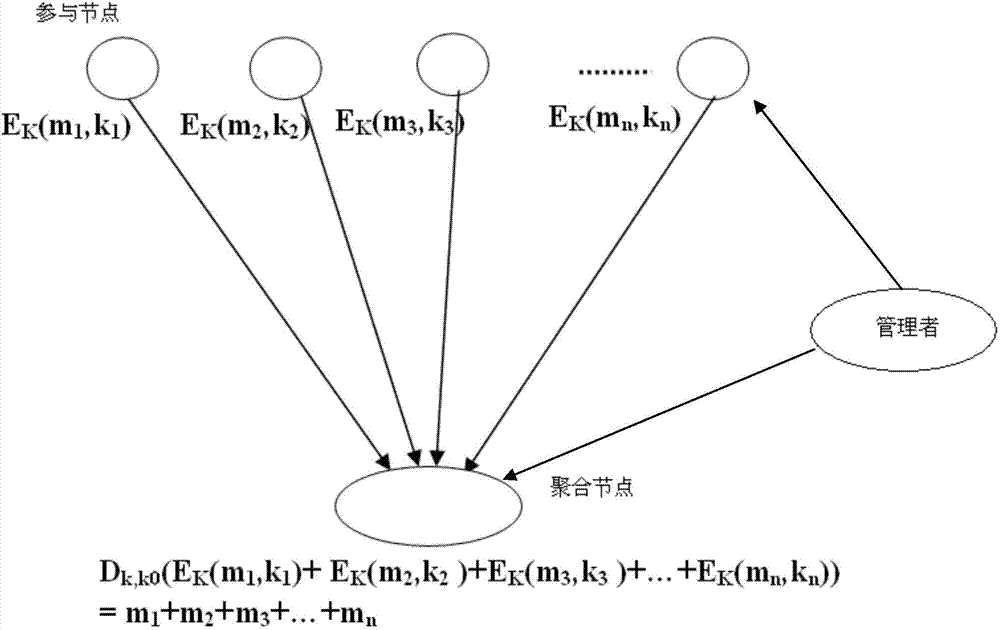
[0023] Such as figure 1 As shown, the security data aggregation model based on the present invention includes an aggregation node and multiple participating nodes, and the participating nodes send data to the aggregation node to implement aggregation.
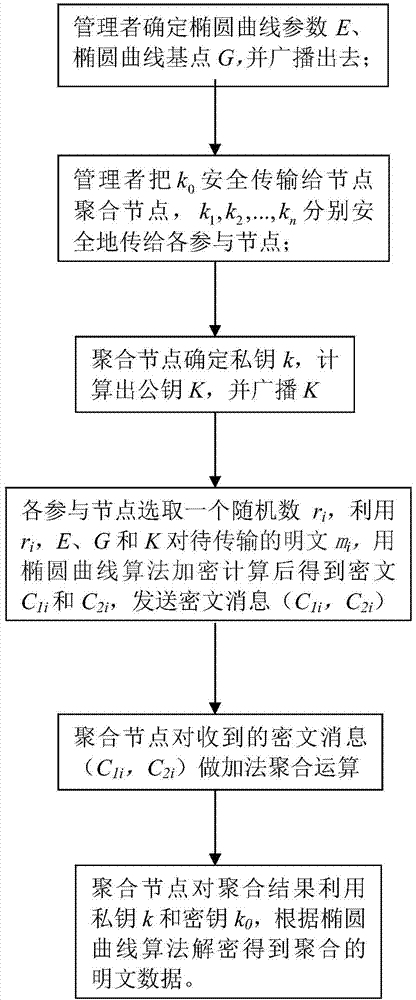
[0024] Such as figure 2 As shown, the aggregation process is:
[0025] The administrator determines the relevant parameters of the elliptic curve E and the base point G, and broadcasts the parameters and G of the elliptic curve. The aggregation node generates the private key k, calculates the public key K according to the formula K=kG and the base point G, and broadcasts K.
[0026] The manager also generates a set of keys k 0 ,k 1 ,k 2 ,...,k n , and make k 0 =k 1 +k 2 +...+k n , put k 0 Securely transmitted to the aggregation node, k 1 ,k 2 ,...,k n Securely transmit to each participating node respectively.
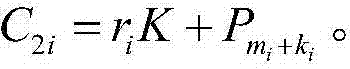
[0027] Participating nodes use public key K and key k respectively 1 ,k 2 ,...,k n Encrypt plaintex...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com