A lightweight RFID two-way authentication method against desynchronization
A two-way authentication, lightweight technology, applied in key distribution, can solve problems such as desynchronization attacks, achieve the effect of small computing overhead, increase tolerance, and improve privacy and security attributes
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
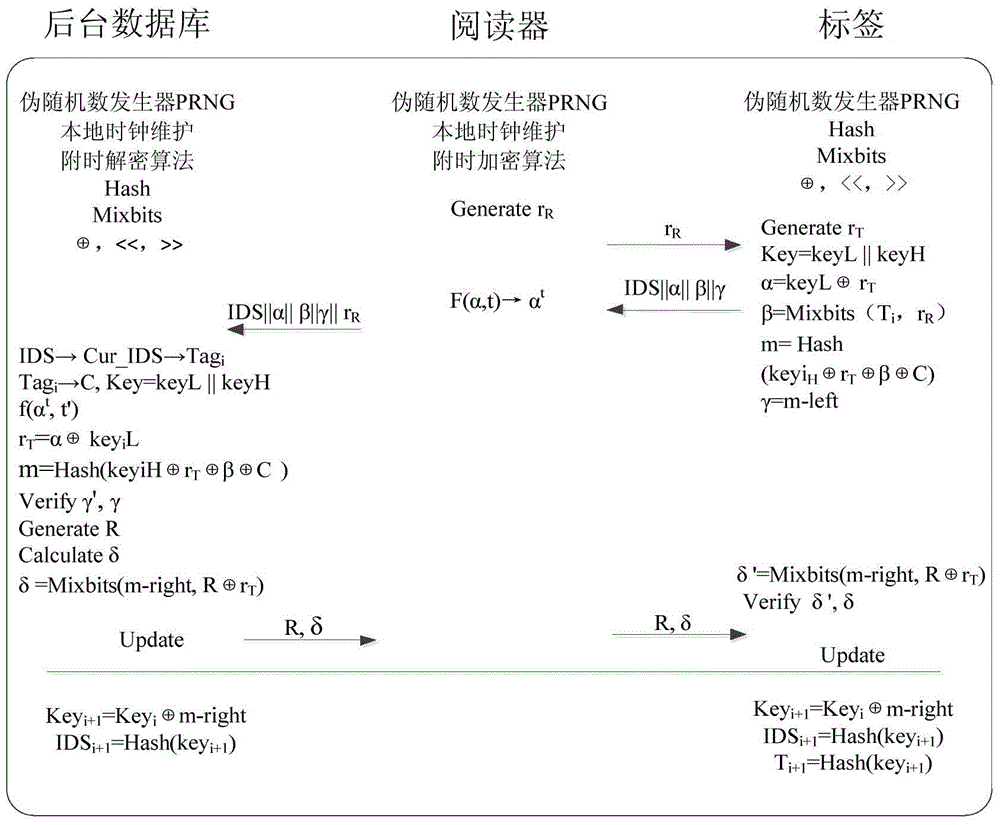
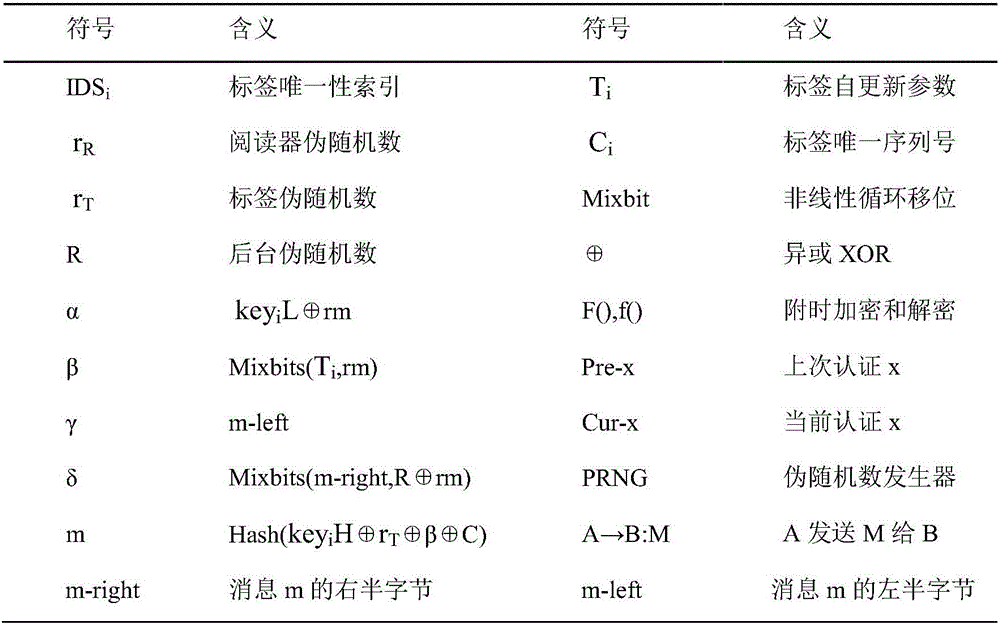
[0018] (1) Implementation steps
[0019] The protocol includes three stages of initialization, authentication, and update. The specific interaction process between the background-reader and the tag in the protocol is described as follows:
[0020] 1. Initialization phase
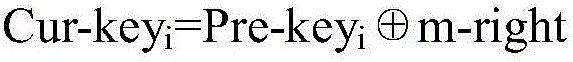
[0021] The RFID system generates a unique serial number C for each tag Tag i , self-updating parameter T i , and share the key group with the database (key i L, key i h). The tag party saves its unique search name and key group, and the storage unit is (IDS, keyL, keyH, T i , C); background database storage directory (Pre-IDS i , Pre-key i ;Cur-IDS i , Cur-key i ; C), where the Cur key unit of the database (Cur-IDS i , Cur-key i ) is the same as (IDS, key) for tags. The reader side and the background database each maintain a local clock t.
[0022] 2. Authentication stage
[0023] 2.1) Step 1Reader→Tag(Challenge Message): r R
[0024] The reader generates a random number r R And sent to the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More