A trusted and secure access method for aerospace information network roaming
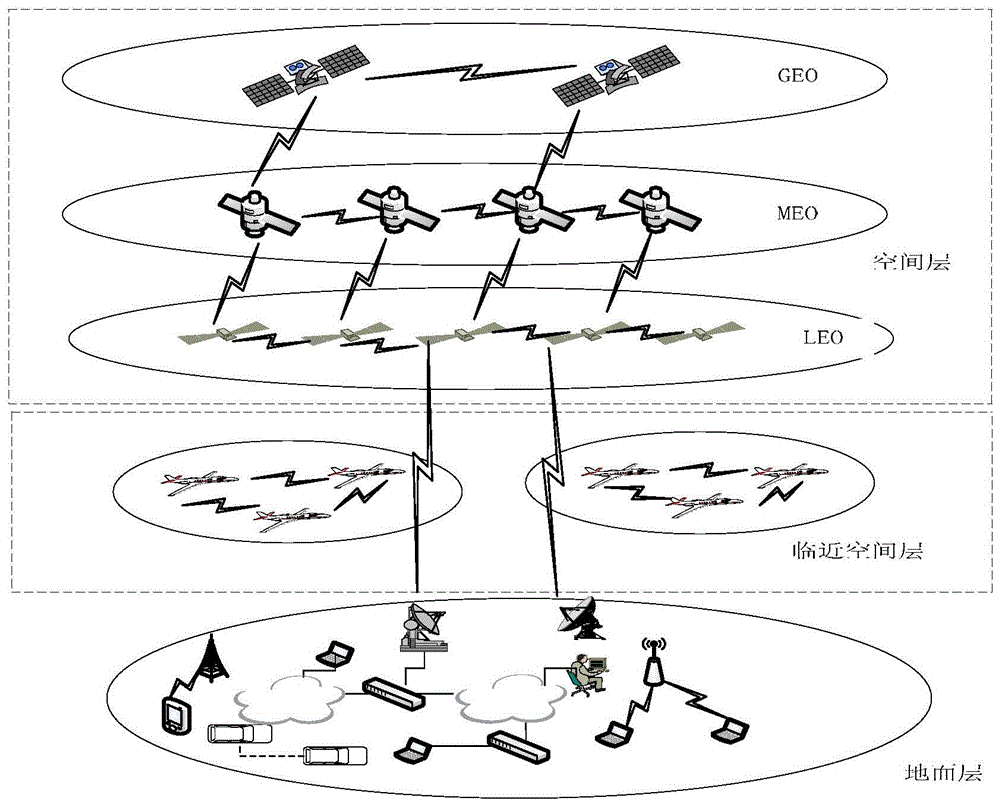
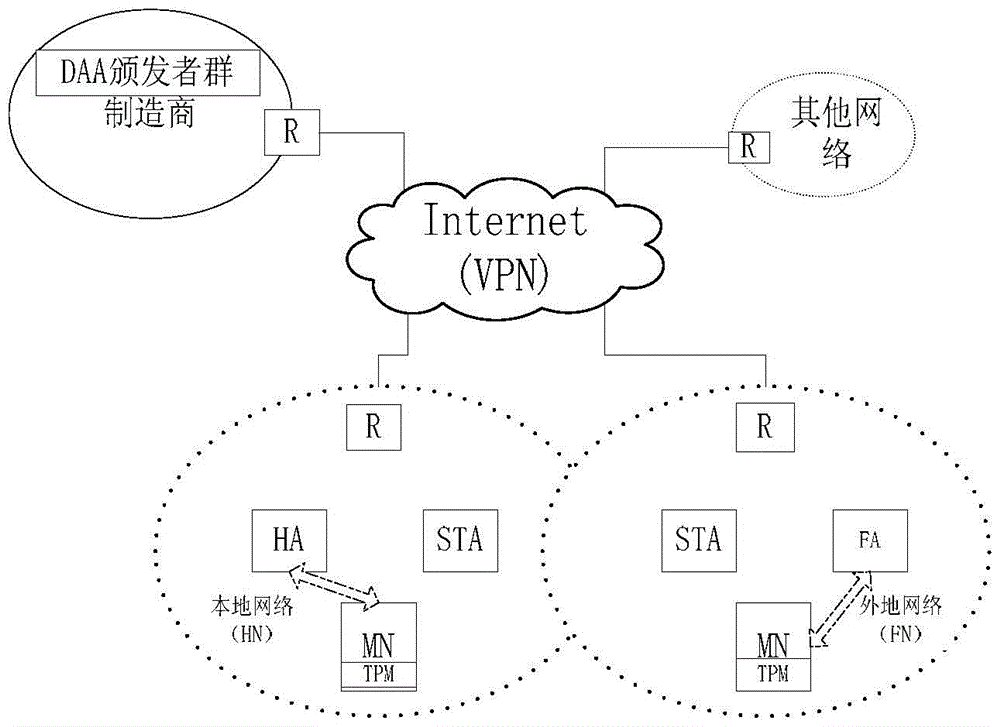
An aerospace information network and secure access technology, applied in the field of secure access, can solve problems such as inability to measure terminal integrity and credibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
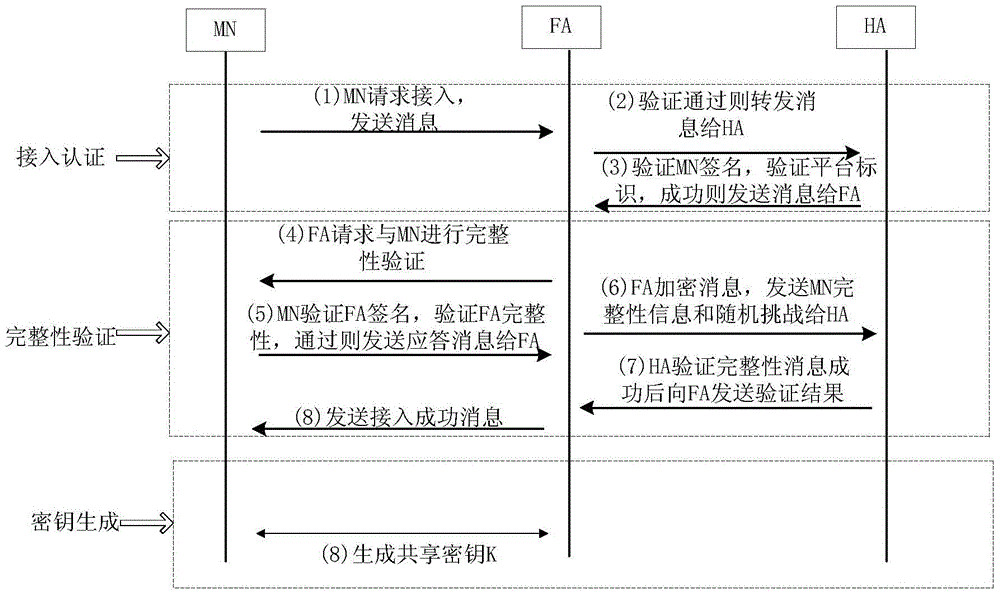
[0053] The implementation manner of the trusted security access method will be described in detail below with reference to the accompanying drawings.
[0054] Description of the main cryptography knowledge, trusted computing technology and security assumptions used in this method:
[0055] 1. Bilinear pairing: let G 1 , G 2 They are respectively the additive cyclic group and the multiplicative cyclic group whose prime number is q in the elliptic curve, and P is the group G 1 the generator of G , and G 1 The discrete logarithm problem on is intractable. Then the bilinear map e:G between two groups 1 ×G 1 →G 2 satisfy the following properties.
[0056] (1) Bilinearity: e(aP,bQ)=e(P,Q) ab , for all P,Q∈G 1 ;a, b∈Z are all established;
[0057] (2) Non-degenerate: there is P, Q∈G 1 , making e(P,Q)≠1;
[0058] (3) Computability: For P, Q∈G1 , there exist efficient algorithms to compute e(P,Q).
[0059] 2. PCR is the value of some registers in the TPM chip that represen...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More