Credibility authorization method, system, credibility security management center and server
A security management and server technology, applied in the field of systems, trusted authorization methods, trusted security management centers and servers, can solve problems such as illegal access and achieve the effect of avoiding illegal access
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
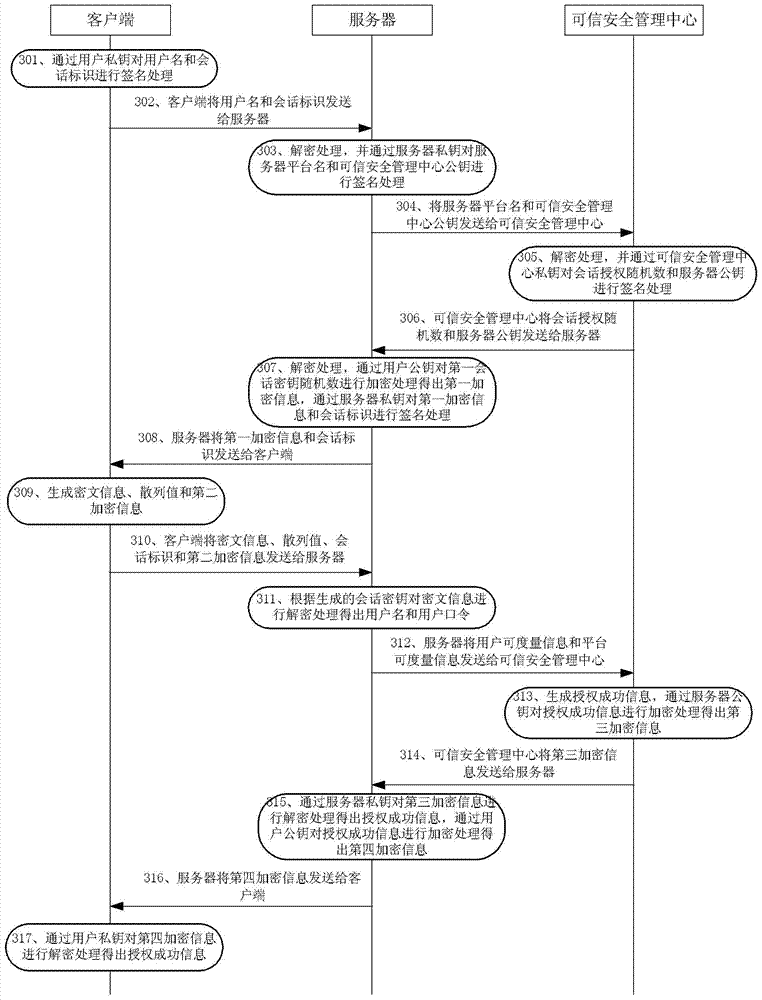
[0060] In order for those skilled in the art to better understand the technical solution of the present invention, the trusted authorization method, system, trusted security management center and server provided by the present invention will be described in detail below with reference to the accompanying drawings.
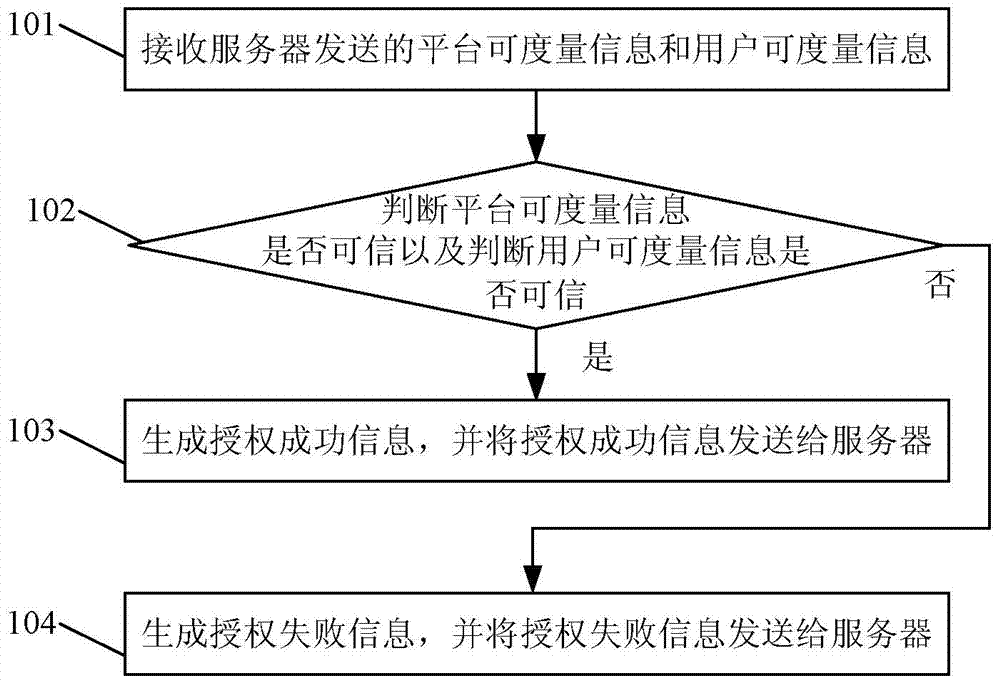
[0061] figure 1 The flow chart of the trusted authorization method provided by Embodiment 1 of the present invention, such as figure 1 As shown, the method includes:
[0062] Step 101, receiving platform measurable information and user measurable information sent by a server.
[0063] Each step in this embodiment may be executed by a trusted security management center. In this step, specifically, the platform measurable information includes hash information and measurable logs, and the user measurable information includes user names and passwords.
[0064] Step 102: Judging whether the measurable information of the platform is credible and whether the measurable...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More