Terminal and method for safely utilizing same
A terminal and security technology, which is applied to the safe use method of the terminal and the terminal field, can solve the problems of insecurity, information leakage and misappropriation, etc., and achieve the effect of safe use method and preventing snooping of user information.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
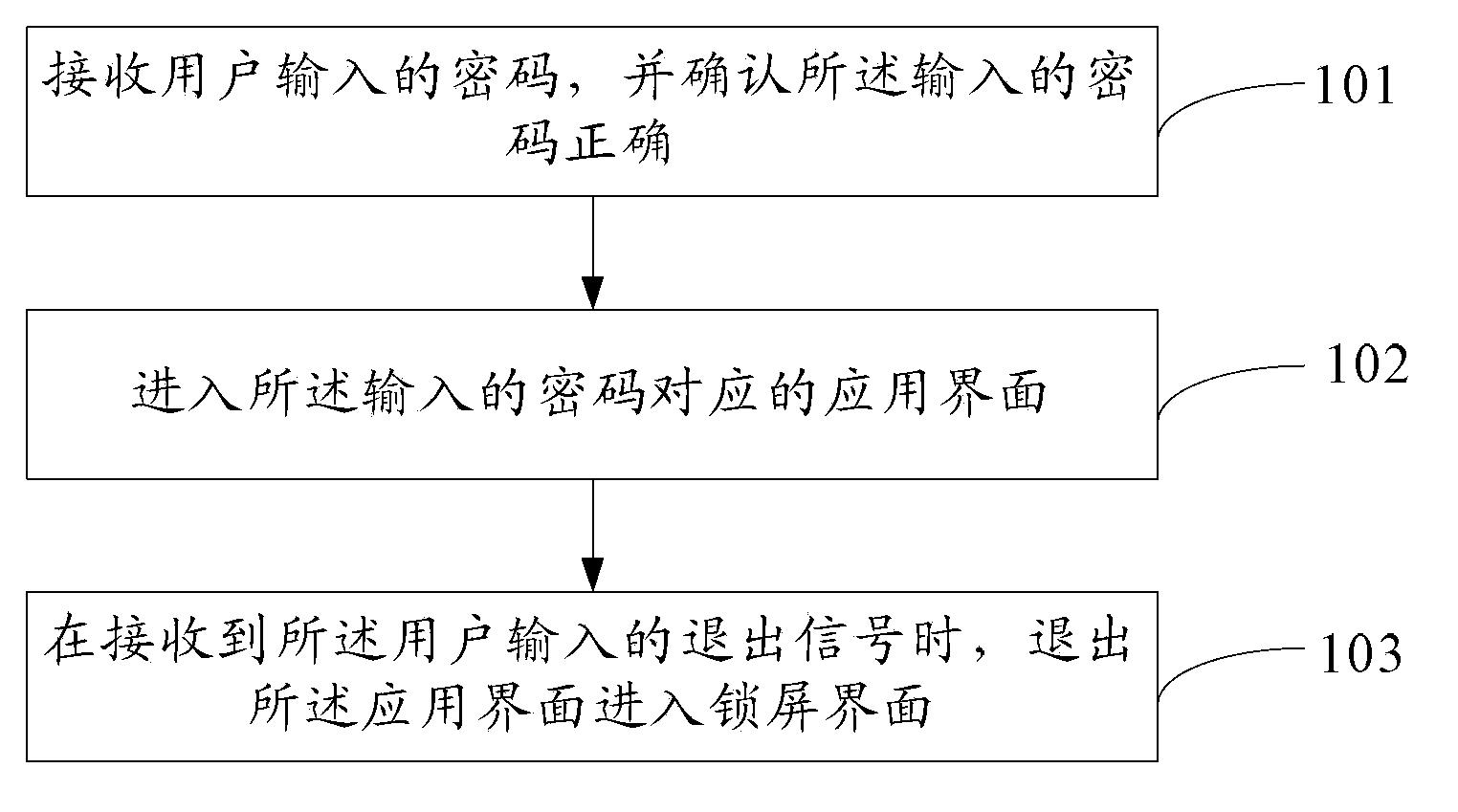
[0022] The embodiment of the present invention provides a method for secure use of a terminal, such as figure 1 As shown, the method includes:
[0023] 101. Receive a password input by a user, and confirm that the input password is correct.
[0024] When the user wants to enter a certain application interface in the terminal, he needs to input a corresponding password into the terminal, and after receiving the password input by the user, the terminal needs to judge whether the input password is correct.
[0025] 102. Enter an application interface corresponding to the entered password.
[0026] After the terminal confirms that the input password is correct, a corresponding application interface will be displayed on the display screen of the terminal, and the user can operate and run the corresponding application.
[0027] 103. When an exit signal input by the user is received, exit the application interface and enter a lock screen interface.
[0028] After the terminal ente...
Embodiment 2
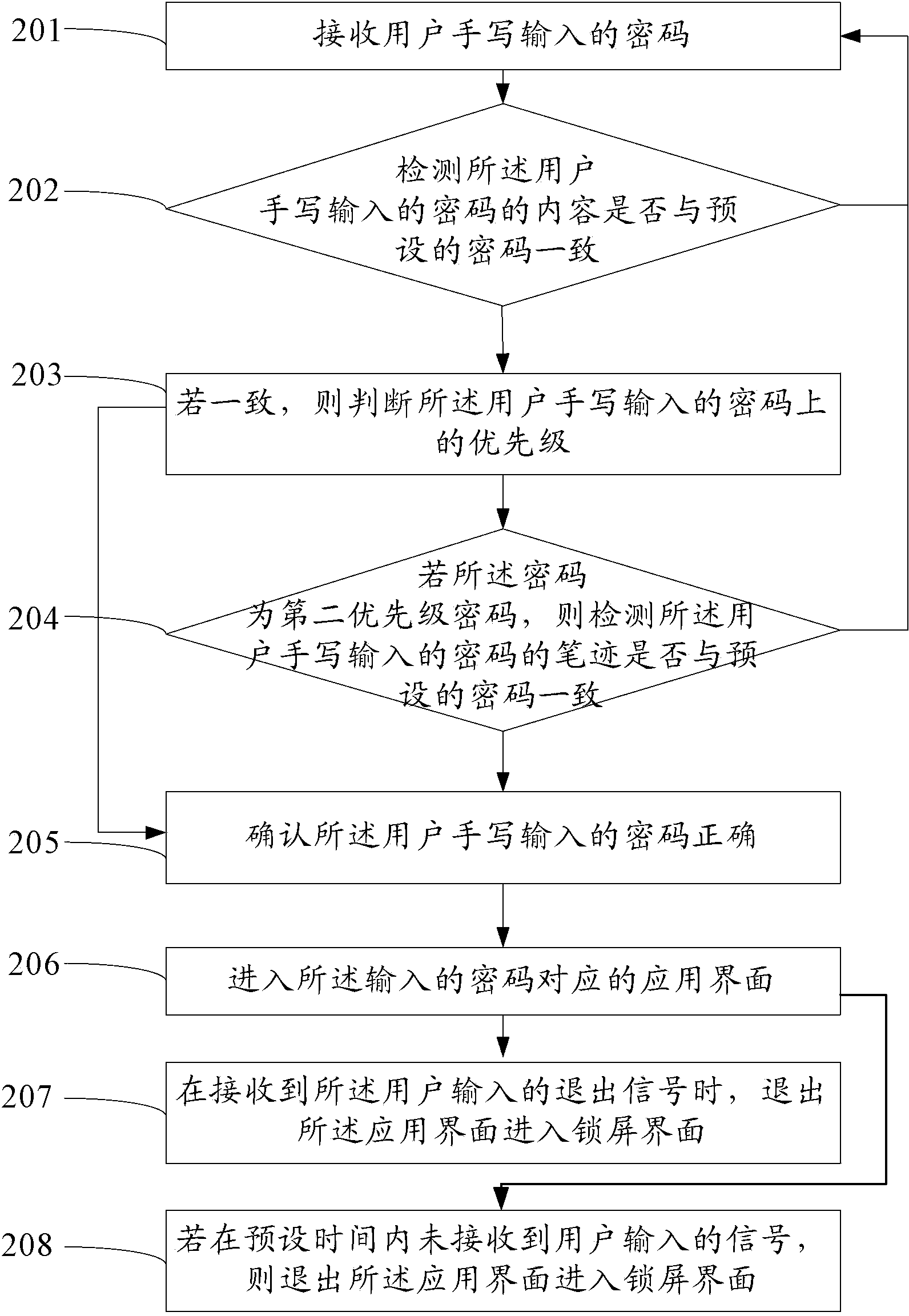
[0031] The current terminal unlocking methods are mainly 9 grids, digital passwords, and picture unlocking. Everyone is using these unlocking methods. The homogeneity is serious and the security is not strong. It is not convenient to open one of the applications. Although Now there are also apps that can be opened directly by pressing a button or swiping somewhere on the lock screen interface. However, due to the limitation of the display screen area of the terminal, there are very few apps that can be directly unlocked and accessed.
[0032] However, in the secure use method of the terminal provided in the embodiment of the present invention, the password input mode set by the terminal is handwriting input. When the user wants to enter a certain application interface in the terminal, he manually inputs the corresponding password on the lock screen interface of the terminal, and the terminal confirms whether the input password is correct after receiving the password input by ...
Embodiment 3
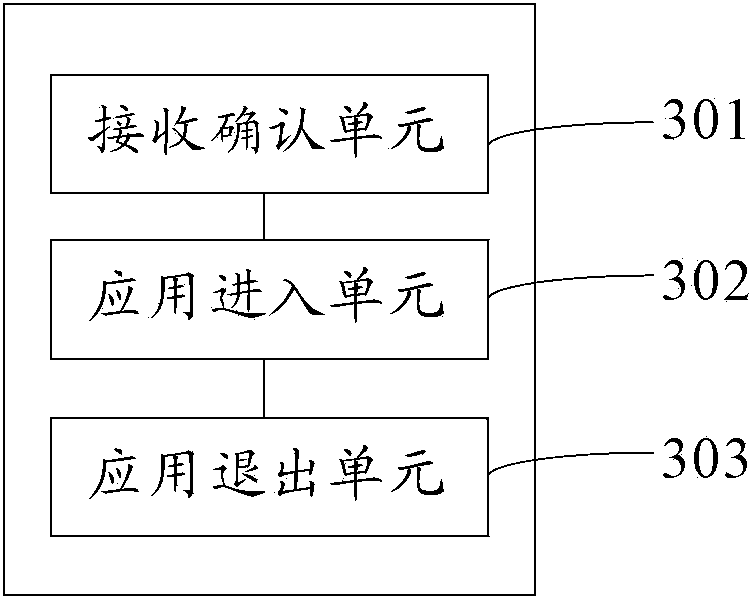
[0057] The embodiment of the present invention also provides a terminal, such as image 3 As shown, the terminal includes: a reception confirmation unit 301 , an application entry unit 302 and an application exit unit 303 .
[0058] The receiving confirmation unit 301 is configured to receive the password input by the user, and confirm that the input password is correct.
[0059] Optionally, the password input mode set by the terminal is handwriting input. The receiving confirmation unit 301 is specifically configured to receive the password input by the user by handwriting, and confirm that the content of the password input by the user is correct; or, receive the password input by the user by handwriting, and confirm the content and handwriting of the password input by the user correct.
[0060] The application entry unit 302 is configured to enter the application interface corresponding to the input password after the confirmation unit confirms that the input password is c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More