Same-account incredible terminal login method and system based on credible terminal
A terminal and trusted technology, applied in the computer field, can solve problems such as reduced security and achieve the effect of improving security performance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] In order to make the purpose, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below with reference to the accompanying drawings and examples.
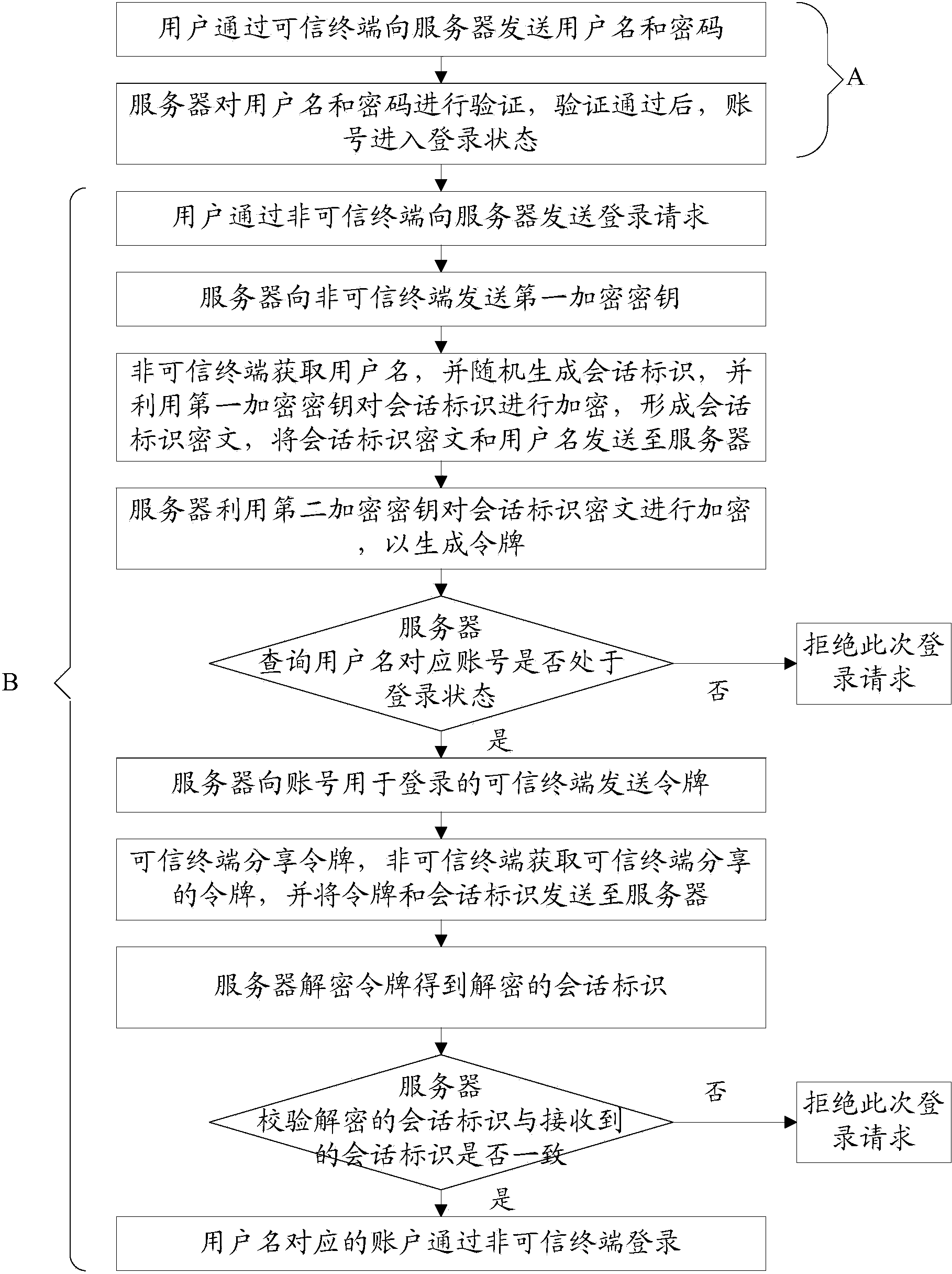
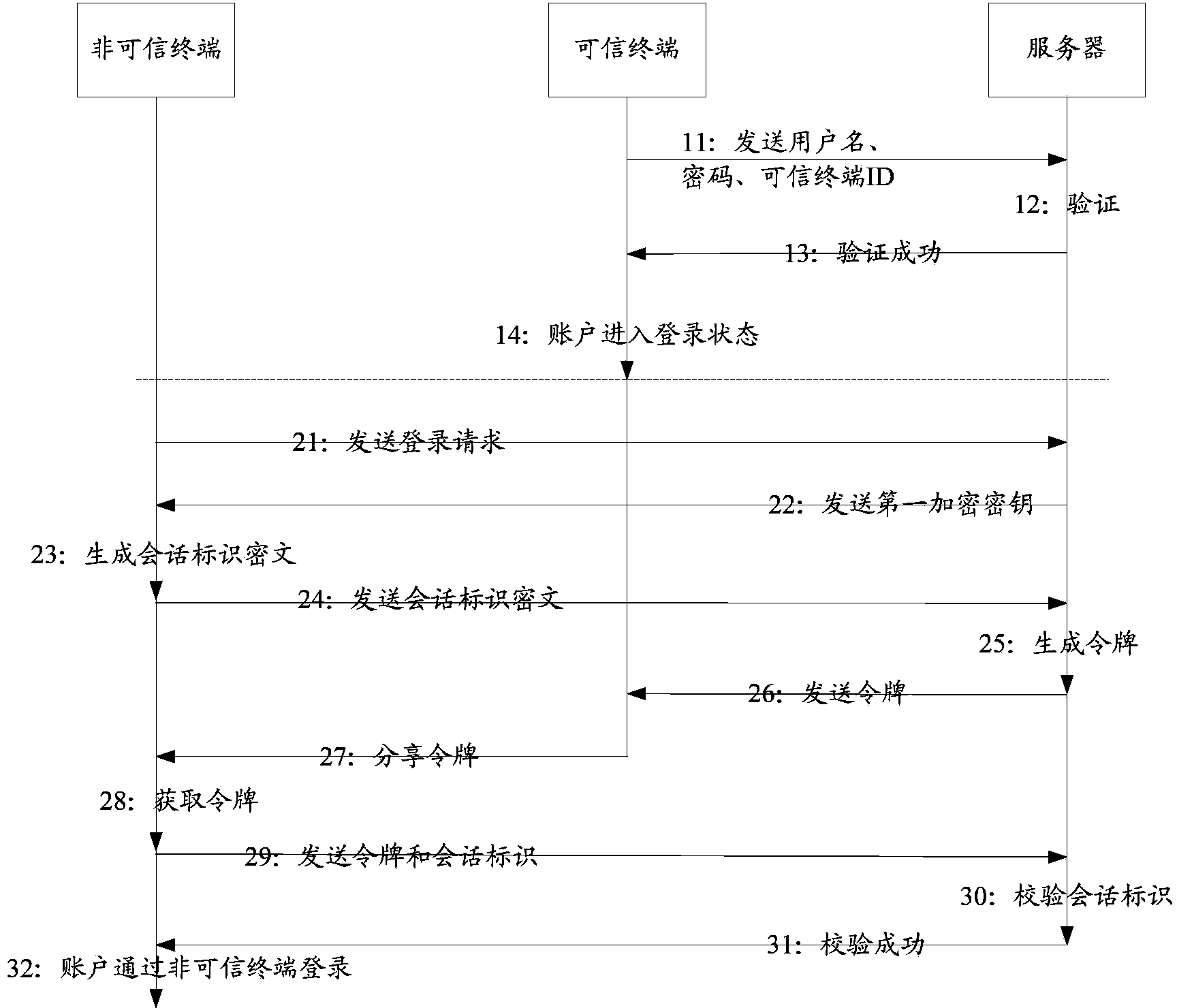
[0041] Such as figure 1 As shown, the present invention provides a trusted terminal-based non-trusted terminal login method with the same account, including:
[0042] A. Account login steps through a trusted terminal:
[0043] The user sends the user name and password to the server through the trusted terminal;
[0044] The server verifies the user name and password, and after the verification is passed, the account enters the login state;
[0045] B. Account login steps through an untrusted terminal:
[0046] The user sends a login request to the server through an untrusted terminal;
[0047] The server sends a first encryption key to the untrusted terminal;
[0048] The untrusted terminal obtains the user name, and randomly generates a session ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More