The method of embedding and extracting copyright images of vector graphics
A technology of vector graphics and images, which is applied in the field of embedding and extraction of copyright images of vector graphics, and can solve problems such as no transformation domain, loss of copyright image fragments, difficulties, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0055] 1. Embedding
[0056] Step 1.1
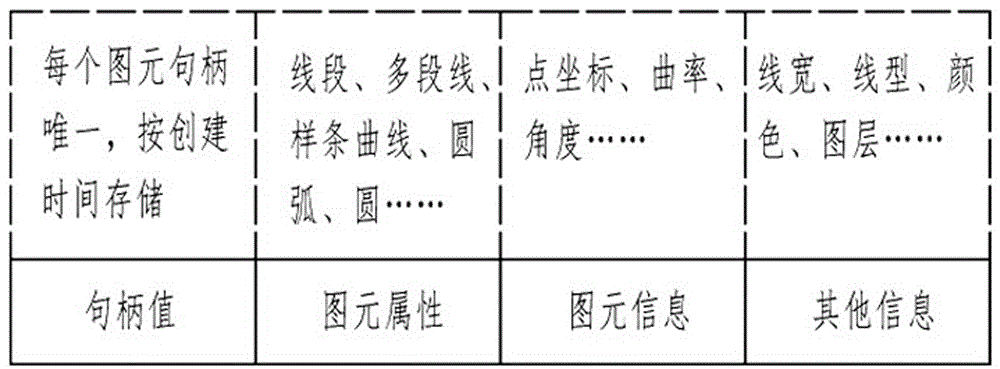
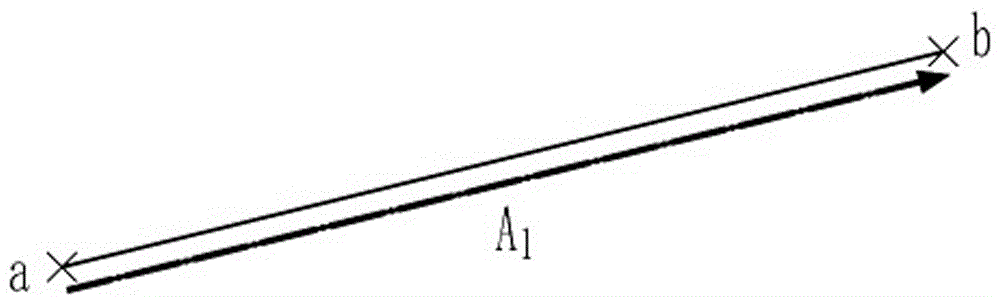
[0057] In this embodiment, the vector graphic to be embedded with the copyright image includes N graphic elements, and its length is N. by Figure 11 The discretized image represents the copyright owner, and the discretized image contains 42×42 pixels, and all the pixels constitute an image sequence. In order to prevent the image sequence from being illegally identified, the image sequence is encrypted, and the existing encryption algorithm (such as Arnold transformation) is preferably used as an input to obtain an encrypted image sequence. In this embodiment, the length of the encrypted image sequence remains unchanged, which is as long as the encrypted image sequence, that is, it consists of 42×42 image points. Divide the encrypted image sequence into L continuous digital fragments, that is, the image fragment e, and obtain e 1 ~e L The image sequence E, the number of bits of the image fragment e is its length t. For security rea...
Embodiment 2
[0146] 1. Embedding
[0147] Compared with Embodiment 1, this embodiment has the same steps 1.1 to 1.4; starting from step 1.5, the difference is that
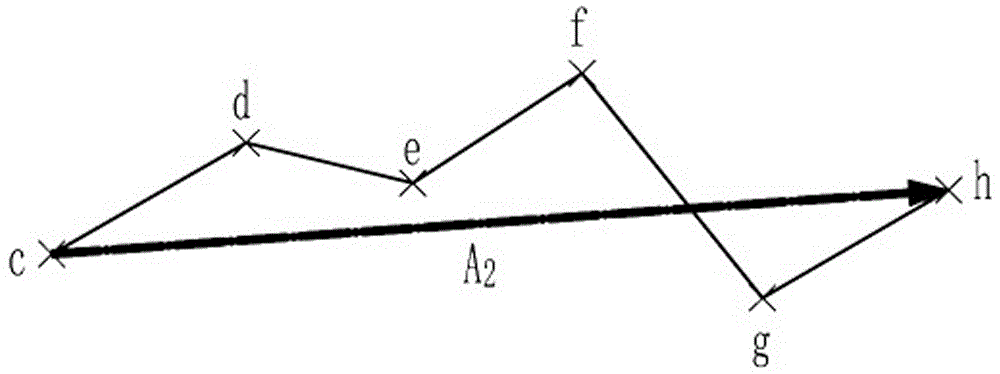
[0148] The first embodiment is to modify the primitives in the first order of the primitive alignment, and this embodiment is to modify the primitives in the second order of the primitive alignment, and thus the extraction steps of this embodiment are different. When this embodiment embeds traversal, it also embeds one by one according to the image sequence E. After embedding a set of image sequence E, continue to embed the traversal point and continue to embed a new set of image sequence E, as in Embodiment 1. After the embedding of this embodiment is completed, The entire vector graphics contains G complete image sequences E.
[0149] This implementation intends to use Figure 10 The 12 primitives in the graph are exaggerated, and the schematic diagram changes before and after embedding. What this embodiment modifies is t...
Embodiment 3
[0154] This embodiment is not intended to exemplify embedding and extraction. This embodiment mainly explains how the present invention can resist geometric attacks and why it is robust to interference attacks.
[0155] 1. Resistance to geometric attacks
[0156] Geometry attacks refer to global scaling, rotation, translation, or the combination of the above operations on the entire vector graphics, in order to modify the primitive function parameters and intend to destroy the image fragments embedded in the function parameters; due to global scaling, rotation, translation Or after the combination operation, although the graph element function parameters are changed, the graph as a whole remains unchanged, which does not affect the reading, so this method is the first choice for attackers.
[0157] The present invention constructs a complex vector operator, calculates the complex ratio of the graph element pair, and embeds the image fragments into the complex ratio. Fragments...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More