Terminal encryption state switching method and system
A state switching and terminal technology, applied in the field of encryption, can solve the problem that the terminal working state switching is not convenient enough, and achieve the effect of improving convenience
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0048] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0049] The invention provides a terminal encryption state switching method.
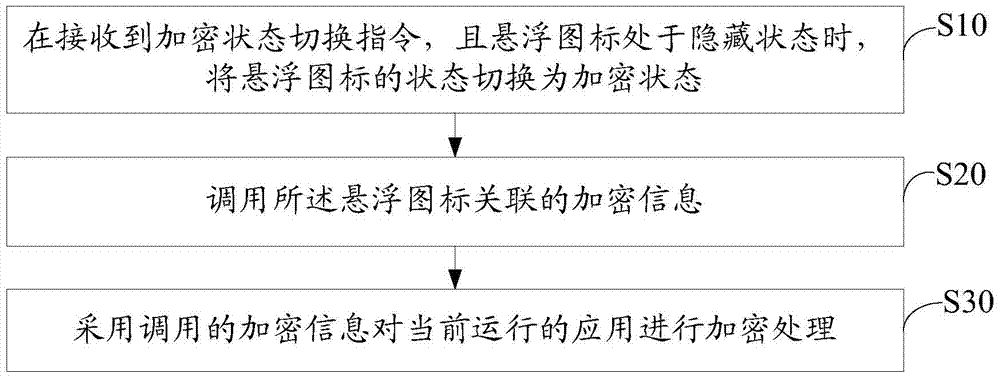
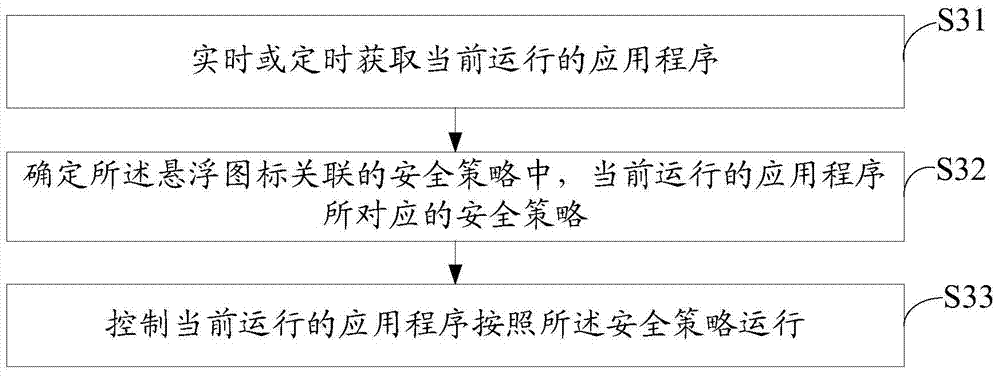
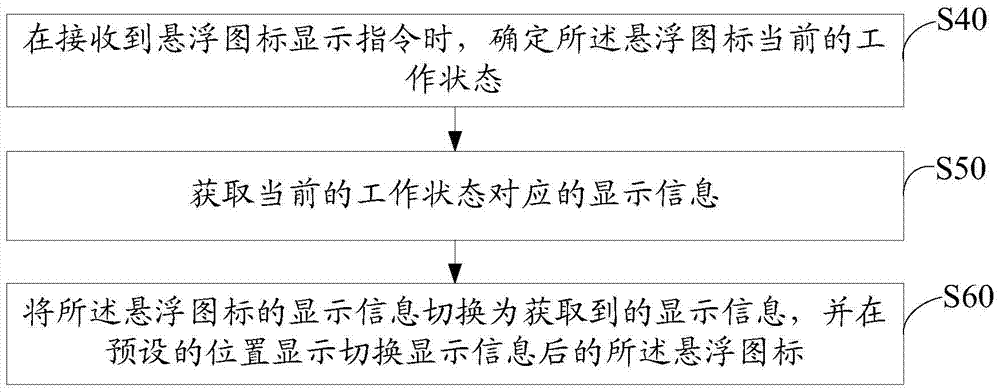
[0050] refer to figure 1 , figure 1 It is a schematic flowchart of the first embodiment of the terminal encryption state switching method of the present invention.
[0051] This embodiment proposes a terminal encryption state switching method, and the terminal encryption state switching method includes:
[0052] Step S10, when the encryption state switching instruction is received and the floating icon is in the hidden state, switch the state of the floating icon to the encrypted state;
[0053] In this embodiment, when the floating icon is in the hidden state, the user can trigger the encryption state switching instruction in various ways, specifically as follows: 1) Trigger the encryption state switching instruction through a control in...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More