Vulnerability scanning method and system
A vulnerability scanning and vulnerability technology, which is applied in the field of vulnerability scanning methods and systems, can solve the problems of low correlation of missed scanning results, inability to integrate analysis and evaluation of missing scanning results of vulnerability scanning products, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
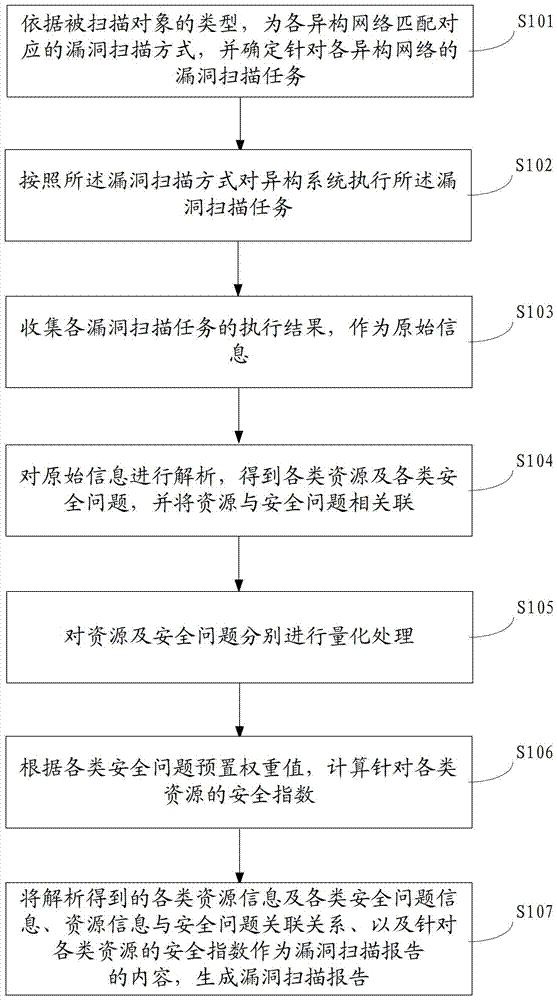
[0059] In order to make the object, technical solution and advantages of the present invention clearer, the implementation manner of the present invention will be further described in detail below in conjunction with the accompanying drawings.
[0060] The technical problem to be solved by the embodiments of the present invention is: in order to solve the problem that the missed scan results of various heterogeneous system vulnerability scan products cannot be integrated, analyzed and evaluated, resulting in a lack of guiding significance for actual security maintenance work.
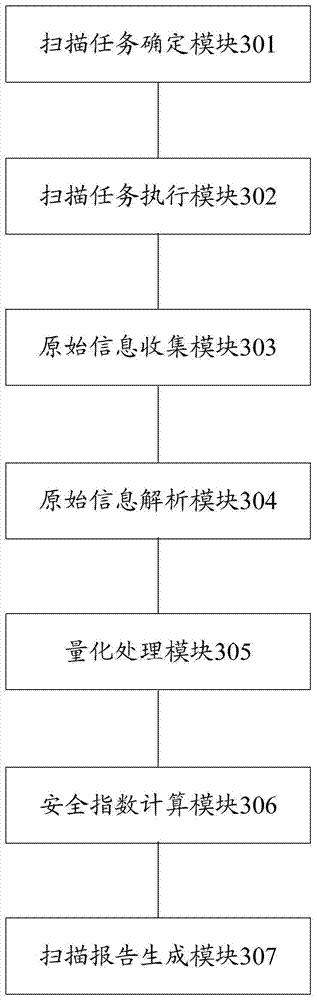
[0061]The overall idea of the embodiment of the present invention: select the corresponding vulnerability scanning product (vulnerability scanning mode) based on the heterogeneous system and automatically order the missed scanning task; The missed scan results after execution; integrate and quantify the missed scan results of heterogeneous systems, analyze and evaluate the missed scan problems through ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More