System and method for counting the number of jvm memory objects
A technology of statistical systems and objects, applied in the field of JAVA virtual machines, can solve the problems of security loopholes and limited number of monitors, and achieve the effect of avoiding security loopholes
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
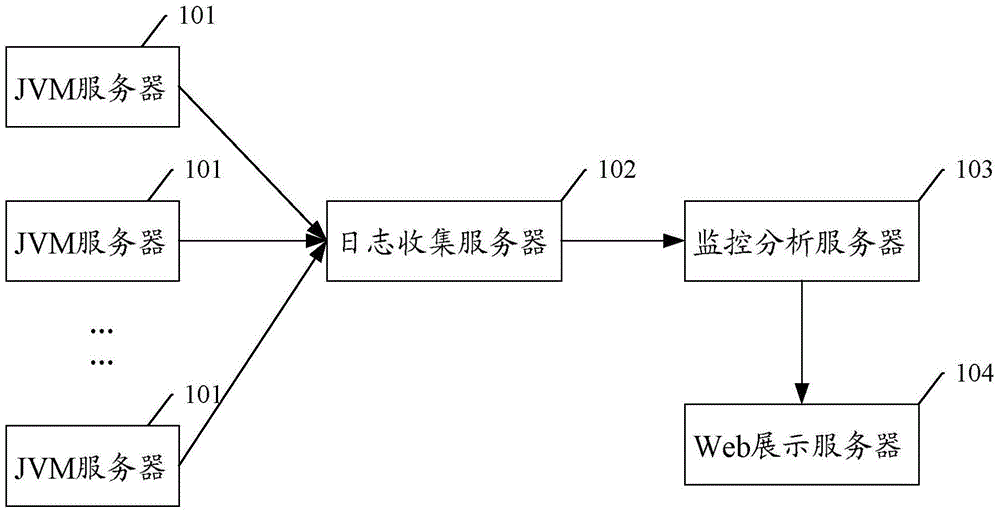
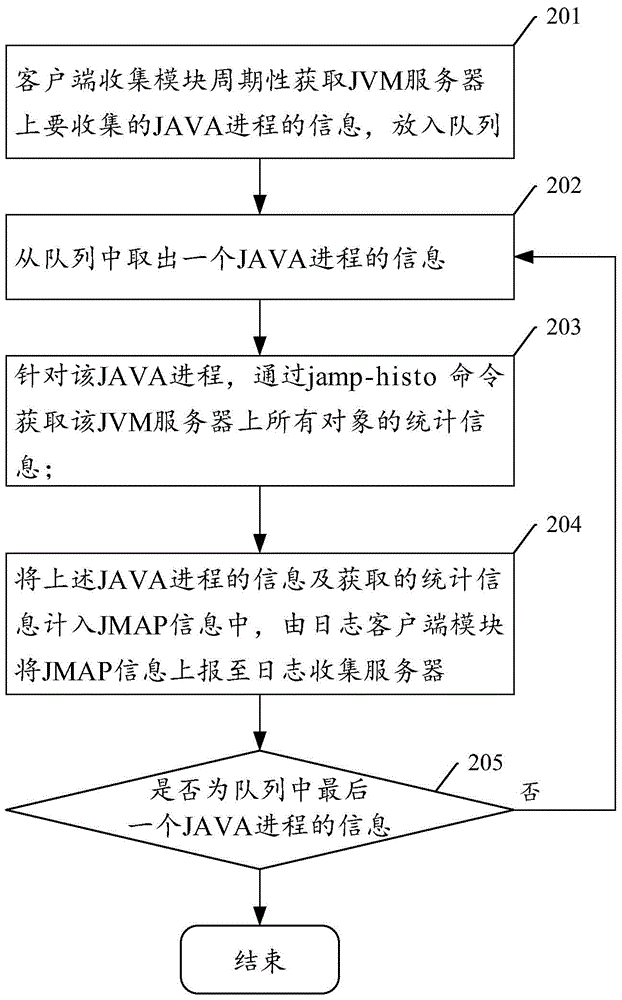
[0027] This embodiment introduces a specific implementation manner in which the JVM server 101 collects JMAP information and reports it to the log collection server 102 .
[0028] In this embodiment, the JVM server 101 may include a client collection module and a log client module; wherein,
[0029] The client collection module can be used to periodically obtain the information of the JAVA process to be collected on the JVM server; for each JAVA process, obtain the statistical information of all objects on the JVM server; the statistical information of the object includes: The corresponding number of instances and bytes;
[0030] The log client module is used to generate JMAP information from the information of the JAVA process and the statistical information, and report the JMAP information to the log collection server.
[0031] The JVM server 101 can first write the generated JMAP information locally and then upload it to the log collection server 102, or upload it to the l...
Embodiment 2
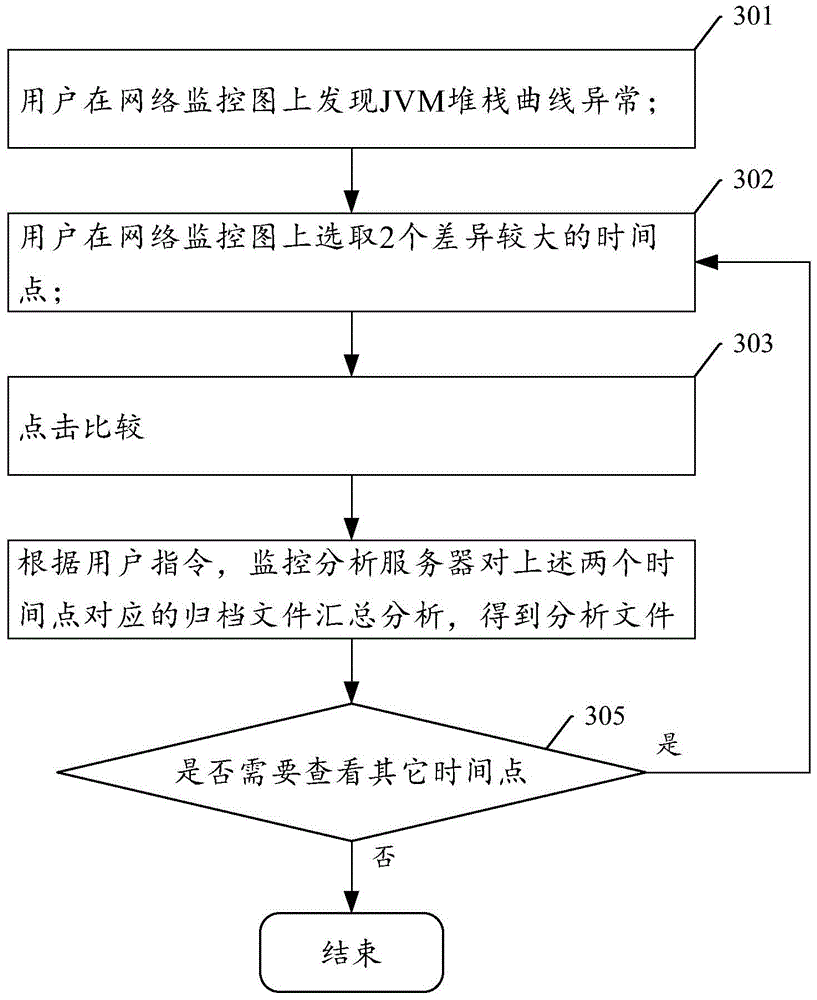
[0039] This embodiment introduces a specific implementation of selecting archive files for analysis according to user instructions, such as image 3 It is the implementation flowchart of this embodiment, including:
[0040] Step 301: The user finds that the JVM stack curve is abnormal on the network monitoring graph;
[0041] Step 302: the user selects two time points with large differences on the network monitoring map;
[0042] Step 303: click to compare;
Embodiment 3
[0046] This embodiment introduces an implementation manner of step 304 in Embodiment 2. like Figure 4 It is the implementation flowchart of this embodiment, including:
[0047] Step 401: read the archive file corresponding to the first time point, and mark it as archive file 1;
[0048] Step 402: For the archive file 1, summarize each class according to the class name, the summary content includes: the total number of instances and the total number of bytes corresponding to the classes existing in the archive file 1;
[0049] Step 403: read the archive file corresponding to the second time point, and mark it as archive file 2;
[0050] Step 404: For the archive file 2, summarize each class according to the class name, the summary content includes: the total number of instances and the total number of bytes corresponding to the classes existing in the archive file 2;
[0051] Step 405: Generate a first analysis file according to the summary content in the above-mentioned st...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap