A decentralized key management method based on homomorphic encryption
A technology of homomorphic encryption and key management, applied in key distribution to regulate user behavior and enhance control
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
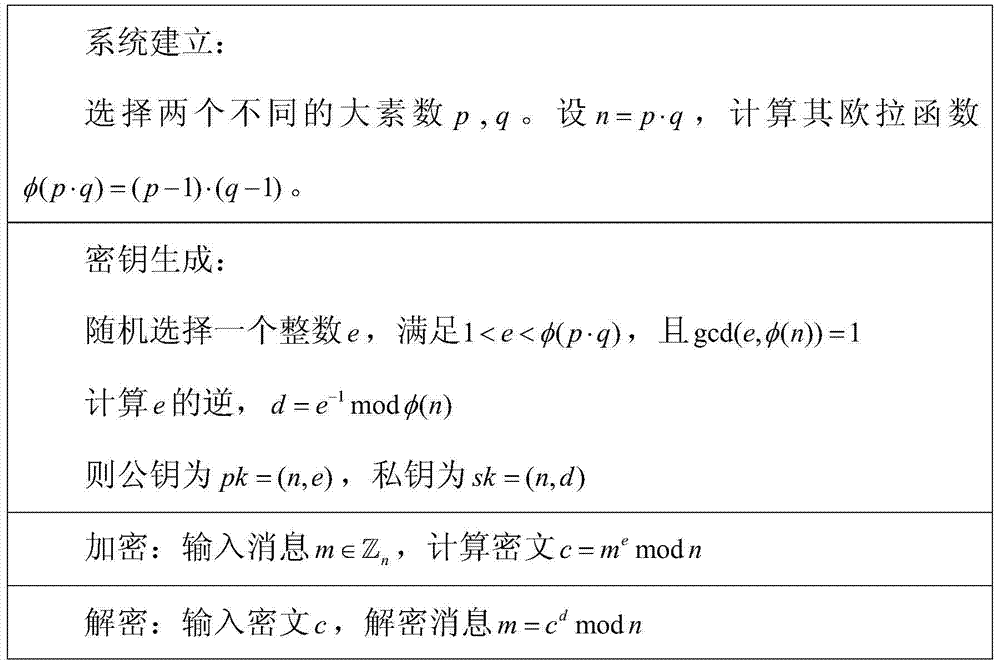
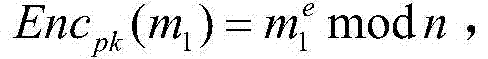
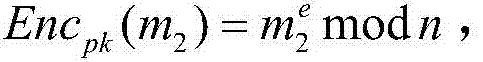
Method used
Image
Examples
Embodiment Construction
[0055] The participants in key management are:
[0056] (1) Users: users of cloud computing services.
[0057] (2) Department: The higher-level department to which the user belongs.
[0058] (3) Encryption proxy: provide users with data encryption services
[0059] (4) Key management center: a third-party key management center for cloud computing, which provides key management services for cloud services.
[0060] (5) Cloud service: the cloud service instance obtained by the user.
[0061] Homomorphic encryption can perform ciphertext calculation without decryption, and has broad application prospects. At present, fully homomorphic encryption can perform arbitrary ciphertext calculations, but its efficiency is very low and cannot be used in real systems. However, single homomorphism has the characteristics of high efficiency and has practical value. In this technical solution, a decentralized key management scheme will be designed using single homomorphic encryption. Two...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More