Embedded encryption method based on high-order second-order logistic mapping and embedded encryption device based on high-order second-order logistic mapping
An encryption method and encryption device technology, applied in the field of information security, can solve problems such as inability to secure information transmission, key changes at any time, and reduced reliability, so as to achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
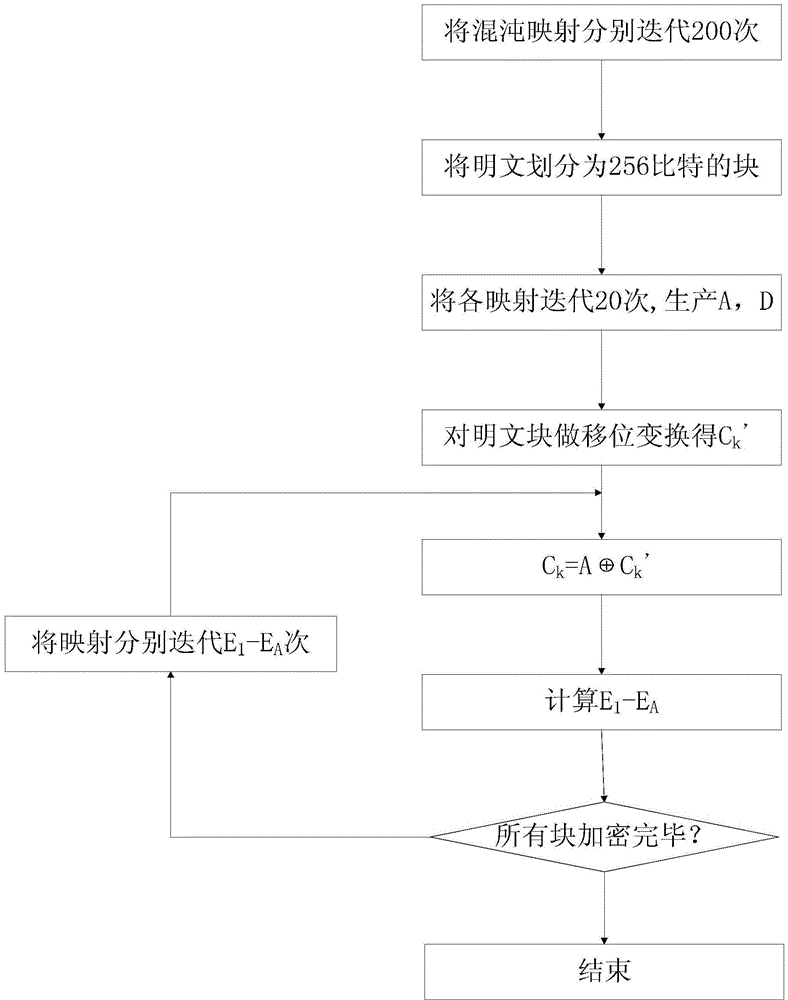
[0029] An embedded encryption method based on a high-order second-order logistic map, such as figure 1 shown, including the following steps:
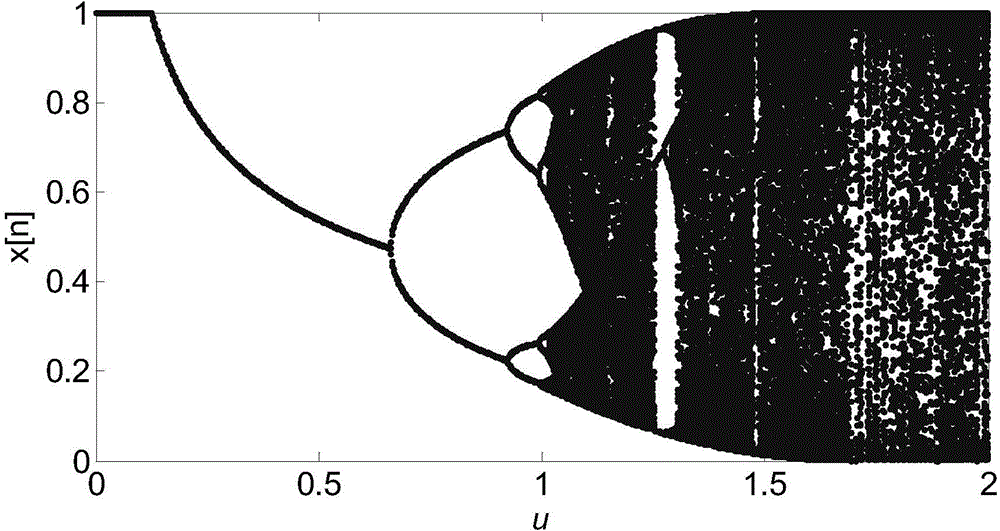
[0030] Step 1, select a logistic map as the generation method of the subkey series:
[0031] x n + 1 [ 1 - 4 u ( x n a - x n b ) ] [ 1 - 4 u ( x n - 1 a - 1 - x n - 1 b ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More