Side channel energy attack method aiming at SM4 password linear transformation output
A linear transformation and energy analysis attack technology, applied in the field of cryptographic algorithm analysis and detection, can solve problems such as wheel key attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0120] The specific embodiments of the present invention are described below so that those skilled in the art can understand the present invention, but it should be clear that the present invention is not limited to the scope of the specific embodiments. For those of ordinary skill in the art, as long as various changes Within the spirit and scope of the present invention defined and determined by the appended claims, these changes are obvious, and all inventions and creations using the concept of the present invention are included in the protection list.
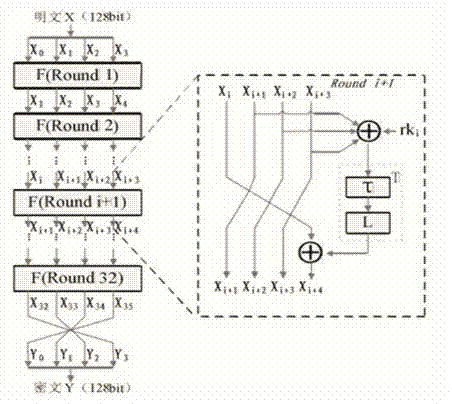
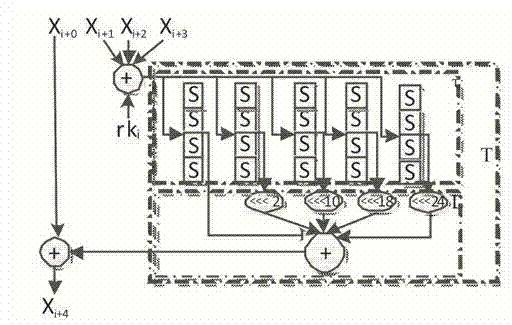
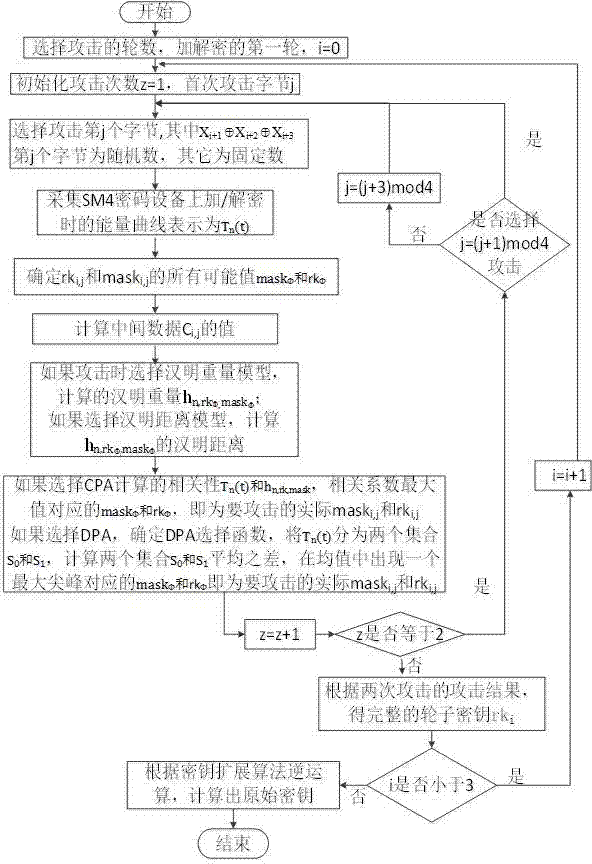
[0121] The side channel energy attack method aimed at the linear transformation output of the SM4 cryptographic algorithm specifically includes the following steps:
[0122] S1: Select the bytes for two attacks, and each corresponding input is (X i+1 ⊕X i+2 ⊕X i+3 ) and the bytes corresponding to the bytes to be attacked are random numbers, and the others are fixed numbers. Use the side channel energy attack method to att...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More