Signcryption method from public key infrastructure environment to certificateless environment
A public key infrastructure and certificate-free technology, applied in the field of heterogeneous signcryption, can solve problems such as unusability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The present invention will be described in detail below in conjunction with the accompanying drawings.
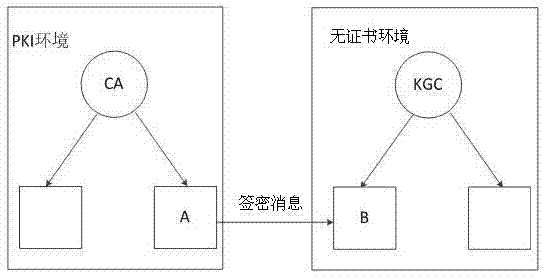
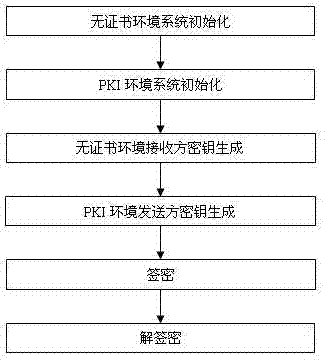
[0030] Such as figure 1 , 2 As shown, the present invention provides a heterogeneous signcryption method from a public key infrastructure environment to a certificate-free environment, and the specific process of the present invention is as follows:
[0031] Step 1. Initialize the system in the non-certificate environment.
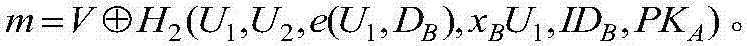
[0032] Security parameter k 1-1 is an integer, and the generator is P 1-1 An additive cyclic group G of 1-1 and a multiplicative cyclic group G 2-1 , the orders of both groups are prime numbers q 1-1 . e 1 :G 1-1 ×G 1-1 →G 2-1 is a bilinear map. Define a secure Hash function where {0,1} * Represents a collection of binary sequences of arbitrary bit length, Represents the additive group obtained by removing the identity element. The key generation center KGC randomly selects As the master private key, calculate P pub =sP 1-1 ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More