Security estimation method and device
A security assessment and technology to be assessed, applied in the communication field, can solve problems such as inability to assess security accurately, and achieve the effect of accurate security assessment
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings. Obviously, the described embodiments are only some embodiments of the present invention, rather than all embodiments . Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0025] Compared with PCs, mobile terminals have an inherent advantage in terms of security, that is, the devices are relatively fixed. If a method can be used to classify the security of the device corresponding to a number, then this is undoubtedly an effective evaluation latitude.
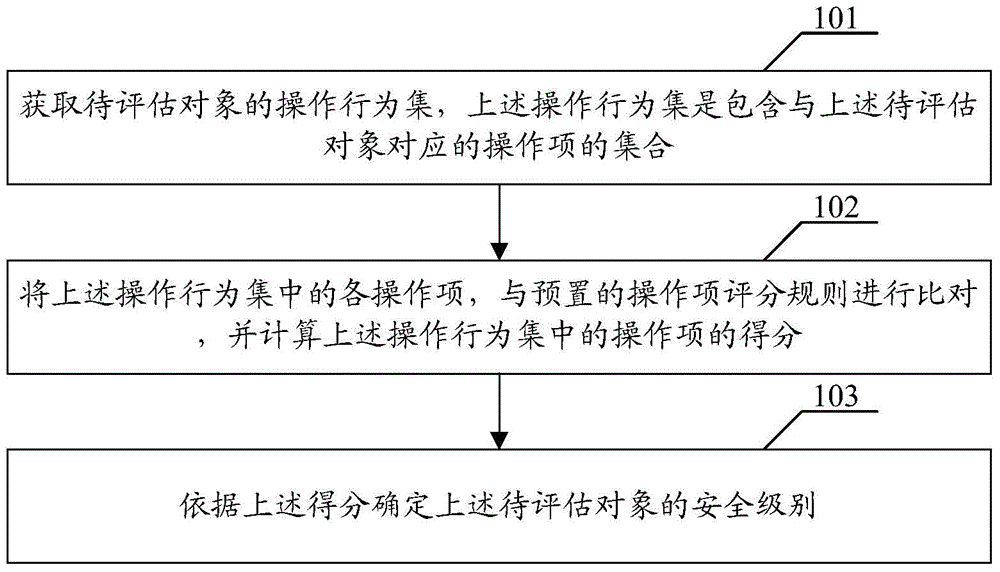
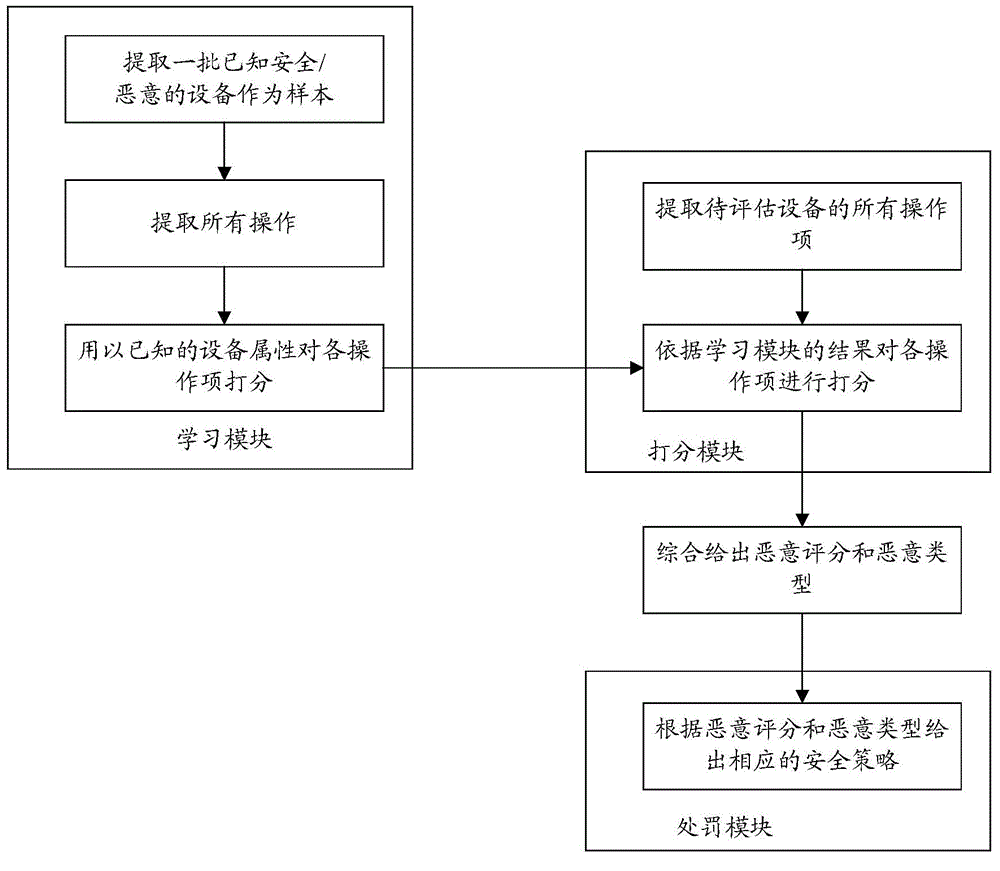
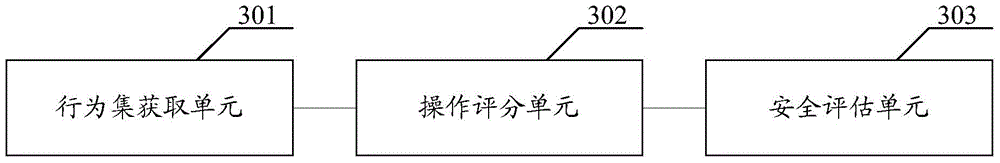
[0026] The embodiment of the present invention aims to propose a method of rating a device according to the credibility of the operation type based on the op...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More