Authentication method, device and system
An authentication method and technology of an authentication device, which are applied in the fields of authentication methods, devices and systems, can solve the problems of user information leakage, increasing the workload of the authentication server, and increasing the risk of being attacked on the network.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
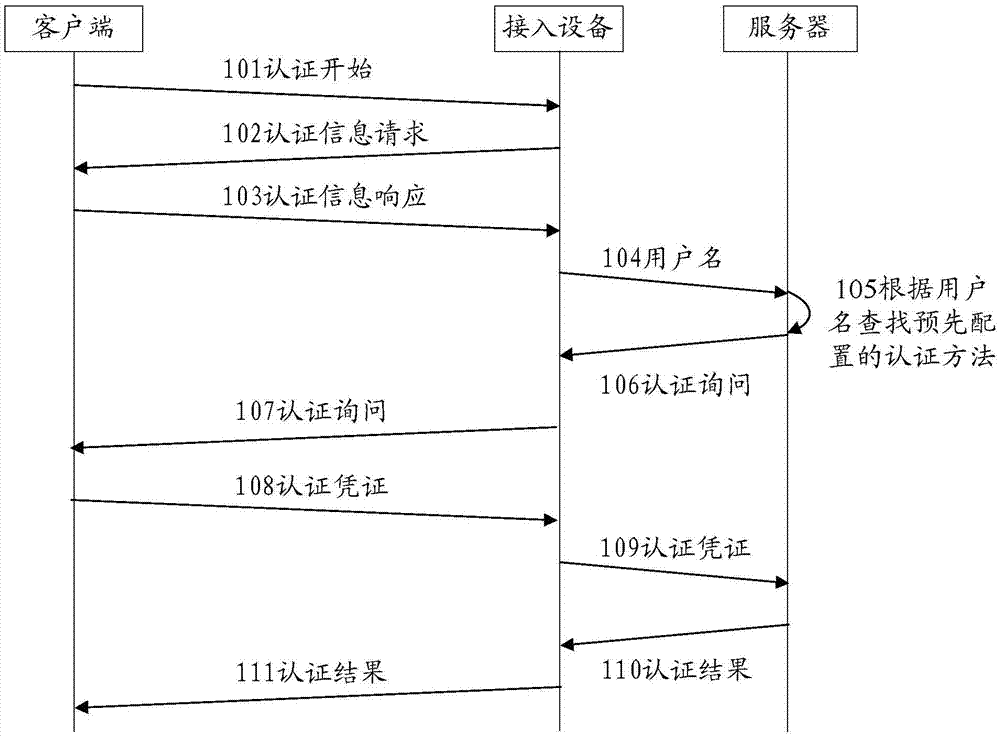
[0024] like figure 1 As shown, authentication methods based on the 802.1X protocol generally include:
[0025] 101. The client sends an authentication start message to the access device to start the authentication process;
[0026] 102. After receiving the authentication start message, the access device responds to the authentication start message sent by the client and sends an authentication information request message to the client, requesting the client t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More