User information protection method and device
A user information and protection device technology, which is applied in the fields of digital data protection, generation of response errors, and error detection of data due to redundancy in operations, can solve problems such as poor user information protection methods, and achieve poor solutions. , the effect of flexible protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] Looking at the development of software technology in recent years, many software companies have developed corresponding security models. Such as blacklist, password, iris, fingerprint, private contacts and so on. However, as people's requirements for information protection are refined, these functions appear to be relatively simple, and the existing technical solutions cannot meet the needs of users.
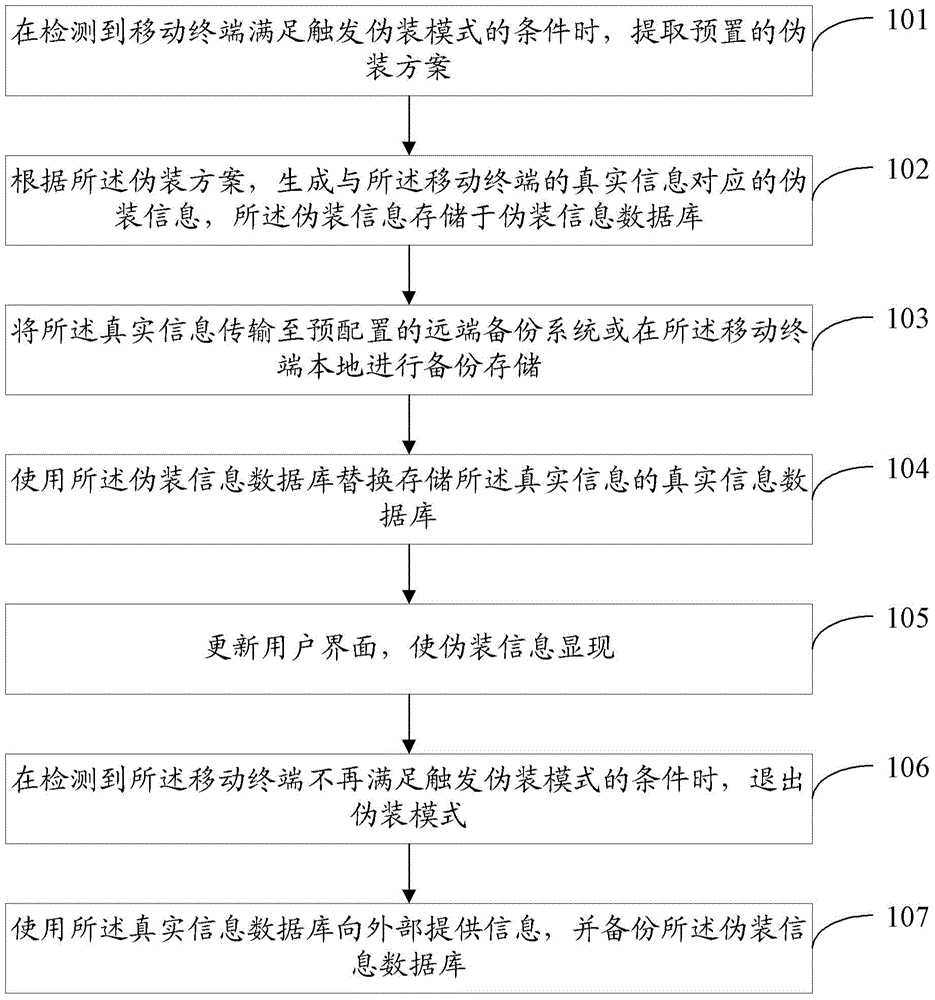
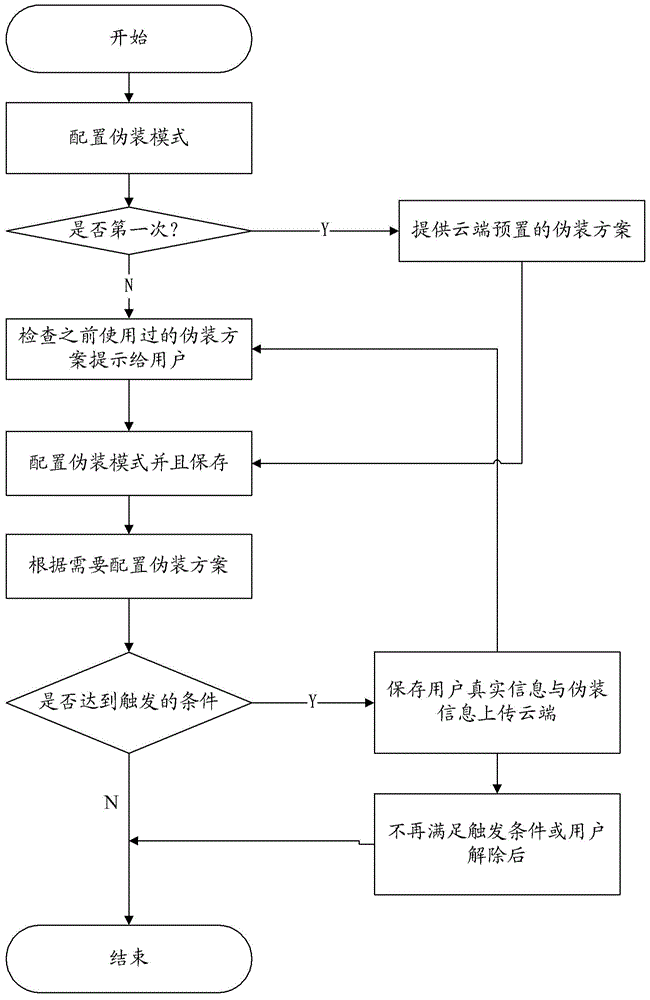
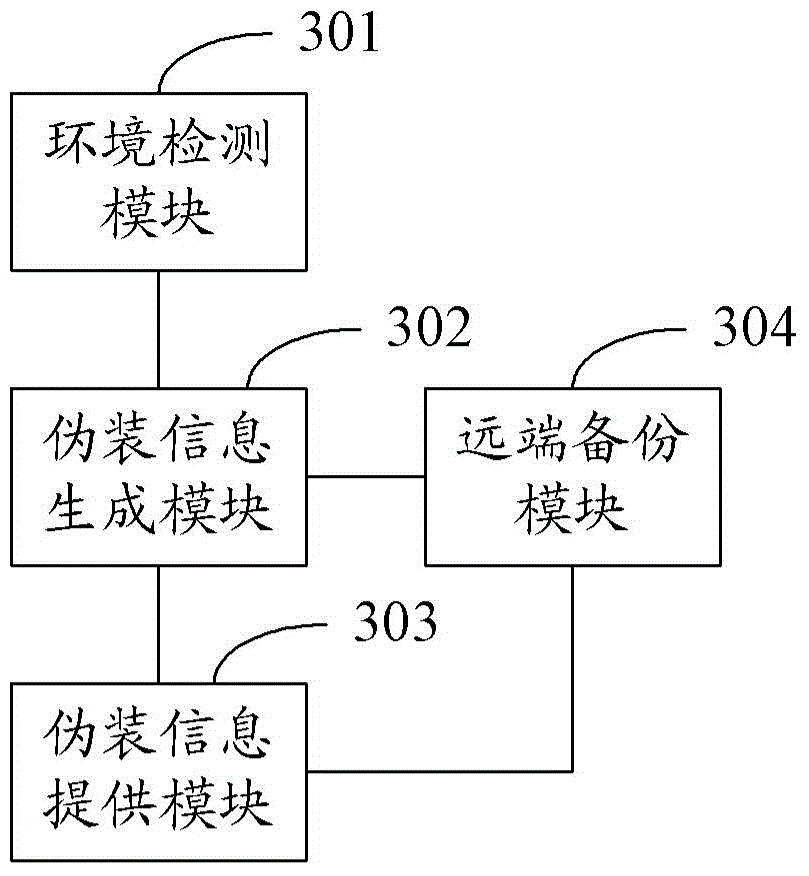
[0038] In order to solve the above problems, embodiments of the present invention provide a user information protection method and device. Embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined arbitrarily with each other.
[0039] First, Embodiment 1 of the present invention will be described with reference to the accompanying drawings.
[0040] The embodiment ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More