Method and system for identifying computer risks based on account clustering
A risk identification and computer technology, applied in the field of computer risk identification methods and systems based on account clustering, can solve the problems of not finding fraudulent account relationships, not well identifying different account groups and batches, etc., and achieve good service. , the effect of speeding up the recognition speed
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] In the following description, many technical details are proposed in order to enable readers to better understand the application. However, those skilled in the art can understand that without these technical details and various changes and modifications based on the following implementation modes, the technical solution claimed in each claim of the present application can be realized.
[0026] In order to make the purpose, technical solution and advantages of the present invention clearer, the following will further describe the implementation of the present invention in detail in conjunction with the accompanying drawings.
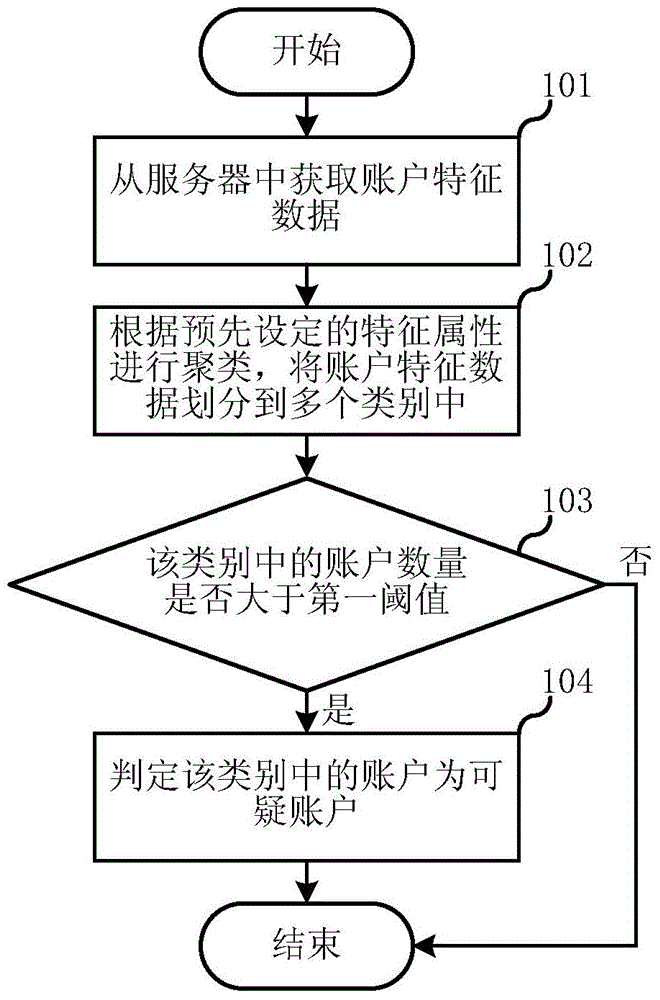
[0027] The first embodiment of the present invention relates to a computer risk identification method based on account clustering. figure 1 is a schematic flowchart of the computer risk identification method based on account clustering. like figure 1 As shown, the method includes the following steps:
[0028] In step 101, account feature data i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More