Permission auditing method and device
A technology for accessing users with authority and unauthorized access, applied in the field of communication, can solve problems such as the inability to implement business authority audits, and achieve the effect of satisfying security management and avoiding security risks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] In order to make the purpose, technical solutions and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings. Obviously, the described embodiments are only some of the embodiments of the present invention, rather than all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
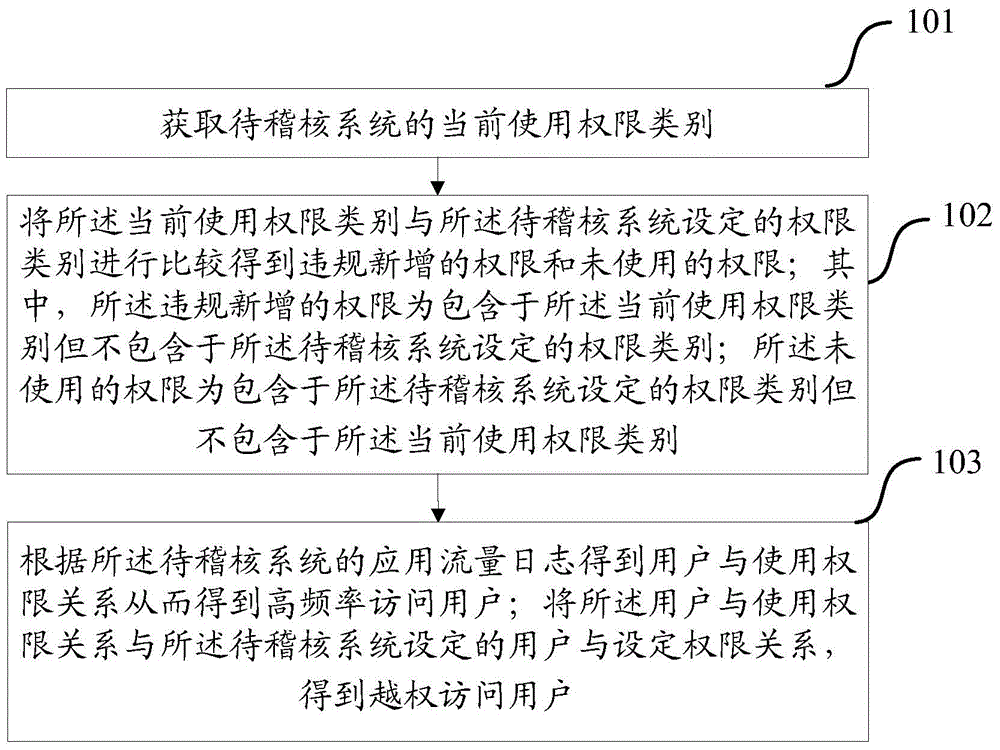
[0047] figure 1 It is a schematic flow chart corresponding to an authority audit method provided by the embodiment of the present invention, the method includes steps 101 to 103:
[0048] Step 101, obtaining the current usage authority category of the system to be audited;
[0049] Step 102: Comparing the current use authority category with the authority category set by the system to be audited to obtain the newly added authority in vi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More